Operation Epic Fury and Roaring Lion Ignite Unprecedented Cyber Warfare
On February 28, 2026, the United States and Israel initiated a synchronized military offensive—dubbed Operation Epic Fury by the U.S. and Operation Roaring Lion by Israel—targeting strategic assets within Iran. This decisive action triggered an expansive cyber conflict that rapidly engulfed the Middle East and extended its reach globally.
Immediate Cyber Repercussions
In the immediate aftermath of the strikes, Iran launched a multifaceted retaliatory cyber campaign. This involved a coalition of hacktivist groups, state-sponsored entities, and opportunistic cybercriminals, culminating in one of the most intense cyber confrontations in recent history.
A significant early development was Iran’s near-total internet blackout. By the morning of February 28, domestic connectivity plummeted to between 1% and 4%. This abrupt disruption severed state-aligned cyber units from their command and control infrastructures, severely impairing their capacity to coordinate and execute sophisticated cyberattacks in the short term. Consequently, Iranian cyber cells transitioned into operational isolation, potentially leading to unpredictable deviations from their established attack methodologies.
Exploitation of Public Fear
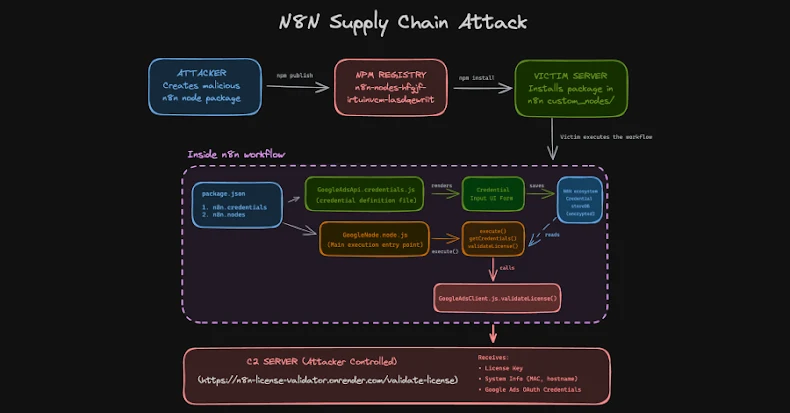
Capitalizing on the prevailing public anxiety, attackers disseminated a counterfeit version of the Israeli Home Front Command’s RedAlert emergency alert application. This malicious Android Package Kit (APK) was distributed via SMS phishing messages, deceiving users into downloading malware designed for mobile surveillance and data exfiltration. This tactic underscores the exploitation of public trust in safety tools during periods of crisis.
Surge in Hacktivist Activity
Despite Iran’s internal connectivity challenges, hacktivist activities outside the nation escalated rapidly. By March 2, approximately 60 distinct groups—including pro-Russian collectives—were actively engaged in operations targeting Israeli, Western, and regional assets. Many of these groups coordinated through the newly established Electronic Operations Room, claiming responsibility for a spectrum of attacks ranging from Distributed Denial of Service (DDoS) assaults on financial institutions and government websites to comprehensive infrastructure compromises affecting energy, payment, and defense systems.
Global Cyber Threats
The conflict’s ramifications extended well beyond the Middle East. In the United Arab Emirates, cybercriminals initiated vishing scams by impersonating the Ministry of Interior to illicitly obtain national identification numbers. Concurrently, the ransomware-as-a-service group Tarnished Scorpius (also known as INC Ransomware) listed an Israeli industrial machinery company on its leak site, egregiously replacing the company’s logo with a swastika. The rapid proliferation and diversity of these attacks signify a shift from traditional state-versus-state cyber engagements to a complex, multi-actor cyber warfare landscape.
The Hacktivist Threat Ecosystem
The Electronic Operations Room has emerged as the central coordination hub for Iran-aligned hacktivist operations since the onset of the conflict. Notably, Handala Hack, a persona linked to Iran’s Ministry of Intelligence and Security (MOIS), has been particularly active. This entity has claimed responsibility for breaching an Israeli energy exploration company, compromising Jordan’s fuel systems, and issuing death threats to Iranian-American and Iranian-Canadian influencers, including sharing their home addresses with physical operatives. This escalation from digital disruption to physical intimidation marks a dangerous evolution in hacktivist behavior.
Other actors within this ecosystem include the Cyber Islamic Resistance—a collective coordinating groups like RipperSec and Cyb3rDrag0nzz—which has claimed to have compromised drone defense systems and Israeli payment infrastructures. The FAD Team reported unauthorized access to multiple Supervisory Control and Data Acquisition (SCADA) and Programmable Logic Controller (PLC) systems in Israel, while DieNet targeted airports and banks across Bahrain, Saudi Arabia, Jordan, and the UAE. Pro-Russian groups such as NoName057(16) and the Russian Legion have also joined the fray, with the latter claiming access to Israel’s Iron Dome radar system, though these assertions remain unverified.
Strategic Recommendations for Organizations
In light of the escalating cyber threats, organizations are advised to implement the following measures:
– Data Backup: Maintain at least one offline copy of critical data to safeguard against ransomware and wiper attacks.
– Asset Hardening: Ensure all internet-facing assets are fully patched and fortified against potential exploits.
– Employee Training: Educate staff on recognizing phishing attempts and social engineering tactics to prevent unauthorized access.
– Geographic IP Blocking: Consider restricting access from high-risk regions to mitigate potential threats.
– Business Continuity Planning: Update and test business continuity plans to ensure resilience against cyber incidents.
– Breach Verification: Establish processes to verify claims of breaches to prevent misinformation and panic.
– Stay Informed: Continuously monitor guidance from authoritative bodies such as the Cybersecurity and Infrastructure Security Agency (CISA) and the UK National Cyber Security Centre (NCSC) to stay abreast of emerging threats and recommended practices.
Indicators of Compromise (IoCs):
– Malicious RedAlert APK Delivery URL: `hxxps[:]//www[.]shirideitch[.]com/wp-content/uploads/2022/06/RedAlert[.]apk`
– Command and Control Data Exfiltration Endpoint: `hxxps[:]//api[.]ra-backup[.]com/analytics/submit.php`
– Shortened URL Used in SMS Phishing Campaign: `hxxps[:]//bit[.]ly/4tWJhQh`
Conclusion
The initiation of Operations Epic Fury and Roaring Lion has precipitated an unprecedented escalation in cyber warfare, characterized by a complex interplay of state-sponsored actions, hacktivist interventions, and cybercriminal opportunism. This evolving landscape necessitates heightened vigilance and proactive measures from organizations worldwide to safeguard against the multifaceted cyber threats that continue to emerge.