Trivy Supply Chain Attack Unleashes Self-Propagating CanisterWorm Across 47 npm Packages
In a significant escalation of software supply chain attacks, threat actors have compromised the widely-used Trivy scanner, leading to the dissemination of a novel self-replicating malware named CanisterWorm across 47 npm packages. This incident underscores the evolving tactics of cybercriminals and the vulnerabilities inherent in open-source ecosystems.
The Genesis of the Attack
The initial breach involved unauthorized access to Trivy’s distribution channels, allowing attackers to inject malicious code into its releases. This code was designed to steal credentials from infected systems, setting the stage for further exploitation. Security researchers have linked this sophisticated operation to a cloud-focused cybercriminal group known as TeamPCP.
Unveiling CanisterWorm
Following the Trivy compromise, the attackers expanded their reach by targeting multiple npm packages, embedding CanisterWorm—a previously undocumented self-propagating worm. The malware’s nomenclature, CanisterWorm, derives from its utilization of an Internet Computer Protocol (ICP) canister. These canisters function as tamperproof smart contracts on the Internet Computer blockchain, serving as decentralized command-and-control (C2) servers. This marks the first recorded instance of such technology being exploited for malware distribution.
Scope of the Compromise
The attack has affected a diverse array of npm packages, including:
– 28 packages under the @EmilGroup scope
– 16 packages within the @opengov scope
– @teale.io/eslint-config
– @airtm/uuid-base32
– @pypestream/floating-ui-dom
This widespread infiltration highlights the attackers’ strategic targeting of packages with substantial user bases to maximize the malware’s propagation.
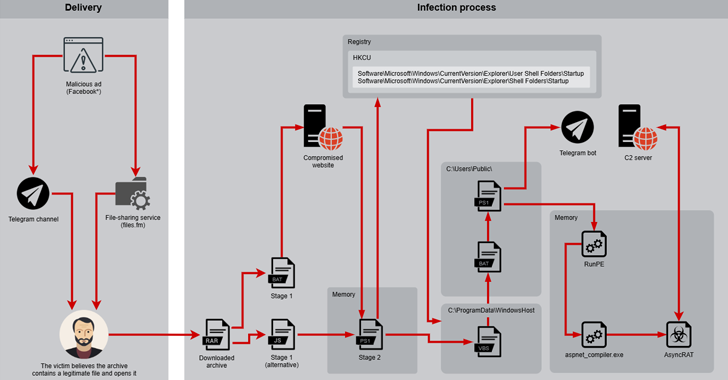
Mechanism of Infection
The infection process is multifaceted:
1. Post-Installation Execution: Upon installation of the compromised npm package, a postinstall script activates a loader.
2. Deployment of Python Backdoor: This loader installs a Python-based backdoor on the host system.
3. Communication with ICP Canister: The backdoor contacts the ICP canister to retrieve a URL pointing to the next-stage payload.
4. Payload Execution: The system downloads and executes the payload from the specified URL.
The decentralized nature of the ICP canister enhances the malware’s resilience, as it allows the attacker to modify the payload URL dynamically, complicating mitigation efforts.
Establishing Persistence
To maintain a foothold on infected systems, CanisterWorm employs several persistence techniques:
– Systemd Service Creation: The malware sets up a systemd user service named pgmon, masquerading as legitimate PostgreSQL monitoring tools.
– Automatic Restart Configuration: The service is configured with the Restart=always directive, ensuring it restarts automatically if terminated, with a brief delay to evade detection.
These methods ensure the malware’s continuous operation and complicate removal efforts.
Command and Control Dynamics
The backdoor communicates with the ICP canister every 50 minutes, using a spoofed browser User-Agent to fetch the current payload URL. Notably, if the canister returns a YouTube link, the malware enters a dormant state, effectively serving as a kill switch. This mechanism allows the attacker to activate or deactivate the malware across all infected systems by updating the canister’s content.
Propagation Strategy
CanisterWorm’s self-propagation is facilitated through a script named deploy.js, which the attacker executes manually. This script leverages stolen npm tokens to distribute the malicious payload across all accessible packages, enabling rapid and widespread dissemination within the npm ecosystem.
Implications and Recommendations
This incident highlights the critical need for robust security practices within software development and distribution channels. Developers and organizations are urged to:
– Implement Multi-Factor Authentication (MFA): Enhance account security to prevent unauthorized access.
– Regularly Audit Dependencies: Monitor and update third-party packages to identify and mitigate vulnerabilities.
– Utilize Automated Security Tools: Employ tools that can detect and alert on suspicious activities within development pipelines.
– Educate Teams on Supply Chain Risks: Foster awareness and training to recognize and respond to potential threats.
By adopting these measures, the software community can strengthen defenses against the evolving landscape of supply chain attacks.