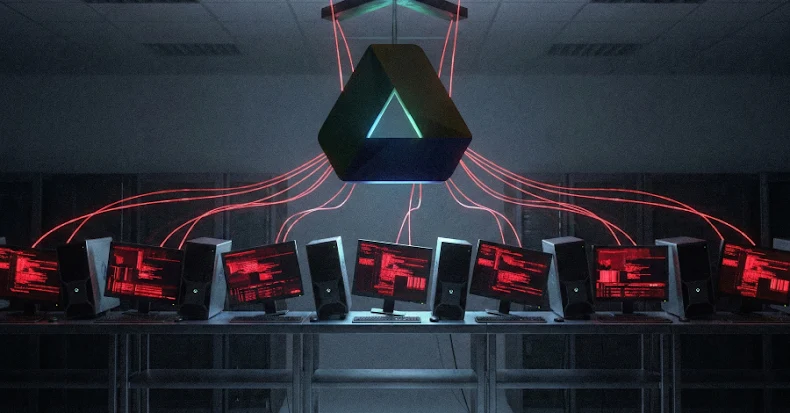
TA446 Deploys Leaked DarkSword iOS Exploit Kit in Targeted Cyber Attacks
In a significant cybersecurity development, the threat actor known as TA446 has been identified utilizing the DarkSword iOS exploit kit in a series of targeted attacks. This sophisticated toolkit, which surfaced in the cybercriminal underground, has been repurposed by TA446 to compromise iOS devices, raising alarms about the evolving tactics of cyber espionage groups.
Unveiling DarkSword: A Potent iOS Exploit Kit
DarkSword is an advanced exploit kit designed to target Apple iOS devices. It leverages a combination of six vulnerabilities, including three zero-day flaws, to achieve full device takeover. The vulnerabilities exploited by DarkSword are:
– CVE-2025-31277: A memory corruption issue in JavaScriptCore, patched in iOS version 18.6.
– CVE-2026-20700: A user-mode Pointer Authentication Code (PAC) bypass in dyld, addressed in version 26.3.
– CVE-2025-43529: Another memory corruption vulnerability in JavaScriptCore, fixed in versions 18.7.3 and 26.2.
– CVE-2025-14174: A memory corruption flaw in ANGLE, patched in versions 18.7.3 and 26.2.
– CVE-2025-43510: A memory management vulnerability in the iOS kernel, resolved in versions 18.7.2 and 26.1.
– CVE-2025-43520: Another memory corruption issue in the iOS kernel, fixed in versions 18.7.2 and 26.1.
By chaining these vulnerabilities, DarkSword enables attackers to execute arbitrary code, escalate privileges, and gain complete control over the targeted device.
TA446’s Deployment of DarkSword
TA446, a group with suspected ties to Russian state-sponsored activities, has been observed deploying DarkSword in attacks targeting users in Ukraine. The group’s modus operandi involves compromising legitimate websites to serve as watering holes. Unsuspecting visitors to these sites are redirected to malicious pages hosting the DarkSword exploit kit.
Once a user visits an infected site via Safari, the exploit chain is triggered, leading to the execution of the DarkSword payload. This payload, known as GHOSTBLADE, is a sophisticated infostealer written in JavaScript. It is designed to rapidly collect and exfiltrate a wide array of sensitive data, including:
– User credentials
– Cryptocurrency wallet information
– Emails
– iCloud Drive files
– Contacts
– SMS messages
– Safari browsing history and cookies
– Photos
– Call history
– Wi-Fi configurations and passwords
– Location history
– Calendar entries
– Cellular and SIM information
– Installed app lists
– Data from Apple apps like Notes and Health
– Message histories from apps like Telegram and WhatsApp
Notably, DarkSword operates with a hit-and-run approach, exfiltrating data within seconds or minutes and then cleaning up to minimize detection.
Technical Breakdown of the Attack Chain
The DarkSword attack chain is a multi-stage process:
1. Initial Compromise: The user visits a compromised website containing a malicious iFrame that loads JavaScript to fingerprint the device.
2. Exploit Execution: If the device is running a vulnerable iOS version (between 18.4 and 18.6.2), the exploit chain is executed.
3. Sandbox Escape: The exploit breaks out of the WebContent sandbox (Safari’s renderer process) and leverages WebGPU to inject into mediaplaybackd, a system daemon responsible for media playback.
4. Privilege Escalation: The injected code gains elevated privileges, allowing access to restricted parts of the file system.
5. Data Exfiltration: The GHOSTBLADE payload collects and exfiltrates sensitive data to an external server over HTTP(S).
This sophisticated chain underscores the advanced capabilities of DarkSword and the significant resources likely invested in its development.
Implications and Broader Context
The deployment of DarkSword by TA446 highlights several critical concerns:
– Exploit Proliferation: The availability of high-quality exploit kits like DarkSword in the cybercriminal market enables less sophisticated actors to execute advanced attacks.
– State-Sponsored Cyber Activities: The use of such tools by groups like TA446 suggests a strategic intent aligned with national interests, particularly in geopolitical contexts like the conflict in Ukraine.
– Rapid Data Exfiltration: The hit-and-run nature of DarkSword’s operations indicates a focus on quick data theft, reducing the window for detection and response.
Mitigation and Protective Measures
To defend against threats like DarkSword, users and organizations should consider the following measures:
– Regular Updates: Ensure that all devices are running the latest versions of iOS, as Apple has patched the vulnerabilities exploited by DarkSword in subsequent releases.
– Cautious Browsing: Be vigilant when visiting unfamiliar websites, especially those that prompt unexpected downloads or redirects.
– Security Solutions: Utilize reputable security software that can detect and prevent exploit attempts.
– User Education: Educate users about the risks of phishing and the importance of not clicking on suspicious links.
The emergence of DarkSword and its deployment by TA446 serve as a stark reminder of the evolving landscape of cyber threats. Staying informed and proactive is essential in mitigating the risks posed by such sophisticated exploit kits.