SmartApeSG’s Deceptive ClickFix Campaign Unleashes Multiple Malware Threats
A sophisticated cyber threat campaign known as SmartApeSG—also referred to as ZPHP and HANEYMANEY—has been actively deploying multiple malware strains through an advanced social engineering technique called ClickFix. As recently as March 24, 2026, this campaign successfully delivered four distinct malware payloads to a single host in one session: Remcos RAT, NetSupport RAT, StealC, and Sectop RAT (also known as ArechClient2). This multi-faceted attack underscores the increasing complexity and danger of modern cyber threats, where attackers layer multiple malicious tools to maximize damage from a single user interaction.
The ClickFix Technique: A Deceptive Entry Point
The SmartApeSG campaign operates by injecting malicious scripts into legitimate, yet compromised, websites. When an unsuspecting user visits one of these sites, they are redirected to a counterfeit CAPTCHA page—a seemingly routine verification check designed to deceive the user into executing harmful scripts. This fake CAPTCHA page employs the ClickFix technique, which silently copies a malicious script into the user’s clipboard and prompts them to paste and execute it manually via the Windows Run dialog box. Once executed, the infection chain initiates without any overt warning signs, making detection challenging.
Sequential Deployment of Multiple Malware Strains
The impact of this campaign is particularly severe due to its sequential deployment of multiple malware families. The infection timeline is as follows:
– 17:12 UTC: Remcos RAT traffic detected one minute after the ClickFix script execution.
– 17:16 UTC: NetSupport RAT activity observed four minutes later.
– 18:12 UTC: StealC begins exfiltrating data to its command-and-control server approximately one hour after NetSupport RAT.
– 19:30 UTC: Sectop RAT activity detected about one hour and eighteen minutes after StealC.
This staggered delivery method provides a narrow window for defenders to detect and mitigate the infection before multiple threats operate concurrently on the compromised system.
Technical Evasion Tactics: DLL Side-Loading
A notable aspect of this campaign is its use of DLL side-loading to evade detection. This technique involves embedding malicious code within packages that also contain legitimate software. The archive files for Remcos RAT, StealC, and Sectop RAT utilize trusted executable files to load malicious DLLs alongside them. Since the primary executable appears legitimate, many security tools may not immediately flag the malicious activity. In contrast, NetSupport RAT, a legitimate remote support application, is configured in this campaign to connect to attacker-controlled servers, subverting its intended purpose.
Network Indicators and Mitigation Strategies
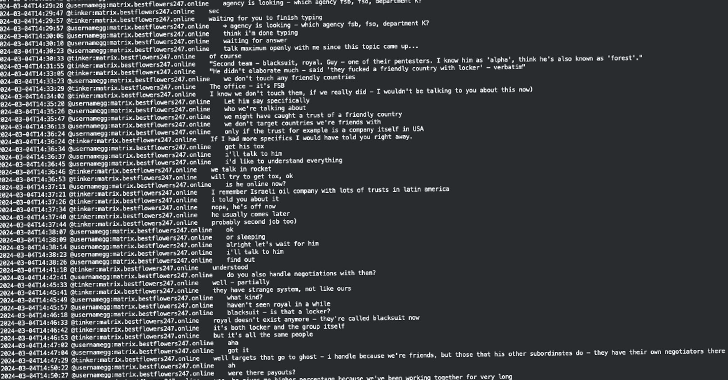
Network traffic analysis reveals distinct connections each malware strain makes to its respective command-and-control server. The HTA file initiating the Remcos RAT download is retrieved from `urotypos[.]com` and saved locally as `post.hta` before execution. The ClickFix script then deletes this HTA file post-execution, complicating forensic investigations.
Organizations are strongly advised to block the domains `urotypos[.]com` and `fresicrto[.]top` at the DNS and firewall levels to prevent further infections. Additionally, educating users about the risks of executing commands from untrusted sources and implementing robust endpoint detection and response solutions can help mitigate such sophisticated threats.
Conclusion
The SmartApeSG campaign exemplifies the evolving nature of cyber threats, where attackers employ advanced social engineering techniques like ClickFix to deceive users into executing malicious commands. By delivering multiple malware strains in a single infection chain and utilizing evasion tactics such as DLL side-loading, this campaign highlights the critical need for comprehensive cybersecurity measures, user education, and proactive threat intelligence to defend against such multifaceted attacks.