SeaFlower Campaign: A Sophisticated Threat to Web3 Wallet Security
A highly sophisticated cyber threat campaign, known as SeaFlower (藏海花), has been identified targeting users of prominent Web3 cryptocurrency wallets. This operation involves embedding stealthy backdoors into cloned versions of legitimate wallet applications, enabling attackers to covertly steal seed phrases and deplete victims’ funds. The campaign is notable for its technical complexity, showcasing advanced skills in reverse engineering, application modification, automated deployment, and covert data exfiltration.
Targeted Wallets and Platforms
SeaFlower specifically focuses on four major cryptocurrency wallets: Coinbase Wallet, MetaMask, TokenPocket, and imToken, across both iOS and Android platforms. The malicious applications are meticulously crafted replicas of the legitimate ones, maintaining identical user interfaces and functionalities. This precision ensures that even experienced users may not detect any anomalies during their routine cryptocurrency transactions.
Indicators of Chinese Involvement
Analysts at Confiant have linked the SeaFlower campaign to Chinese-speaking threat actors. Evidence supporting this attribution includes:
– Source Code Analysis: Comments within the injected backdoor code are written in Chinese.
– Developer Identifiers: Leaked macOS developer usernames correspond to Chinese names.
– Modding Tools: The frameworks used for application modification are popular within Chinese-speaking developer communities.
– Infrastructure Traces: The campaign’s infrastructure is linked to Chinese and Hong Kong IP addresses, with domains registered under .cn top-level domains and the use of Alibaba Content Delivery Network (CDN) for content distribution.
The campaign’s name, SeaFlower, was inspired by a detail uncovered during the investigation. A leaked macOS username, Zhang Haike, found within one of the injected dynamic library (.dylib) files, corresponds to a character in the Chinese novel Tibetan Sea Flower. Additional developer usernames such as lanyu and trader were discovered across different backdoored wallet variants, indicating a common origin for the entire operation.
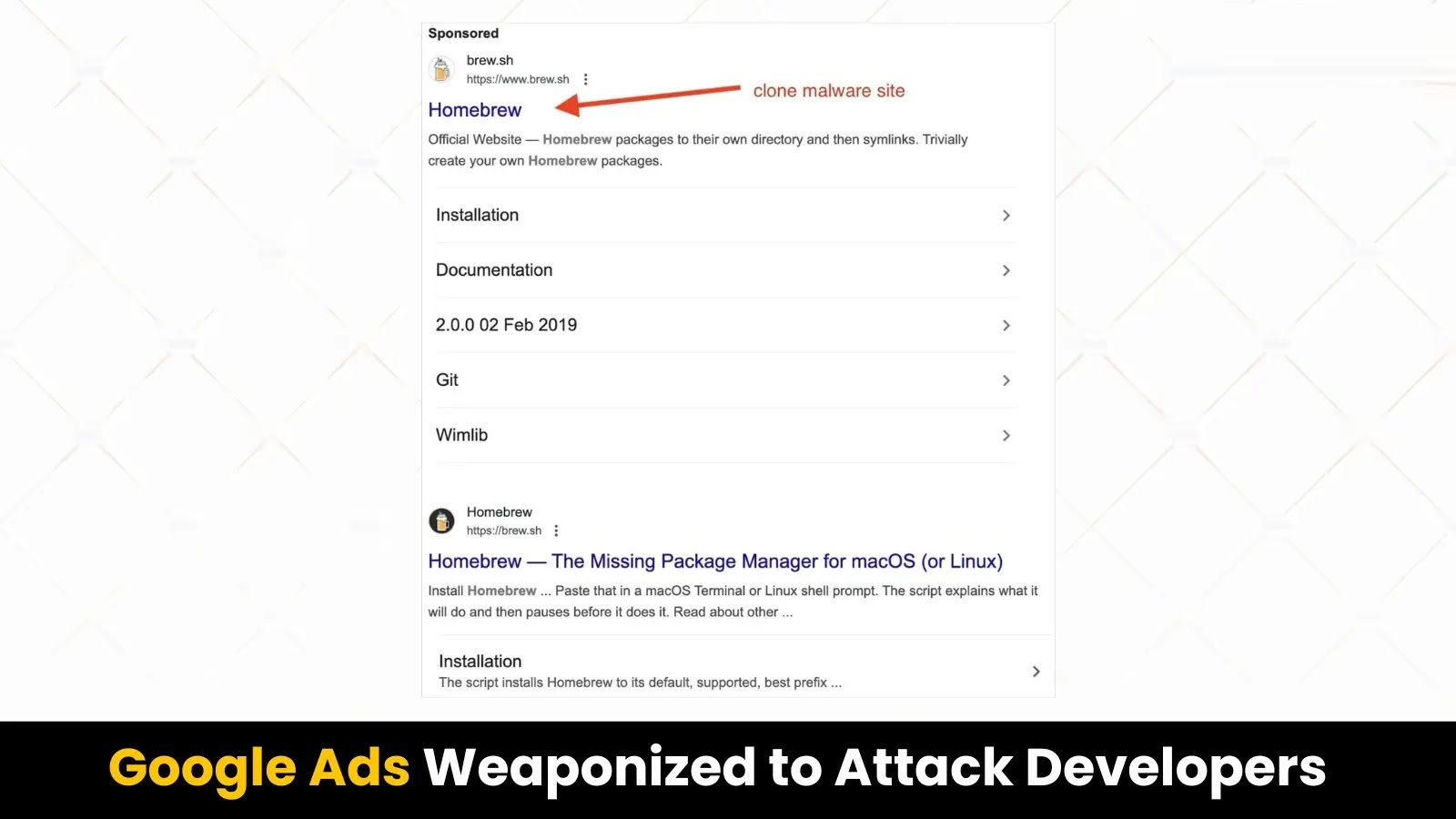
Infection Vector: Search Engine Manipulation
The primary method of infection begins with users conducting searches on Chinese search engines. When individuals search for terms like download MetaMask iOS, results from search engines such as Baidu, Sogou, 360 Search, and Shenma redirect them to websites operated by the SeaFlower campaign. These counterfeit sites are virtually indistinguishable from official wallet download pages, complete with fabricated ratings and download counts, deceiving users into downloading and installing the compromised applications.
Mechanism of the Backdoor
Upon installation of a SeaFlower-modified wallet, the malicious code operates discreetly in the background. For iOS devices, the infection process involves the download of a provisioning profile from the fraudulent website, allowing the backdoored application to run outside the Apple App Store’s ecosystem. After installation, the application appears to function normally; however, embedded within its code is an injected dynamic library that operates covertly.
In the case of the MetaMask iOS wallet (SHA-256: 9003d11f9ccfe17527ed6b35f5fe33d28e76d97e2906c2dbef11d368de2a75f8), researchers identified two injected .dylib files within the compiled Mach-O binary. The primary malicious library utilizes iOS modding tools—Cydia Substrate, Cycript, and MonkeyDev—to hook into the application’s runtime without triggering any visible alerts.
The backdoor intercepts the core iOS function `dataWithContentsOfFile:options:error` at the moment MetaMask reads its main JavaScript bundle. Within the injected library is an obfuscated class named `FKKKSDFDFFADS`, containing RSA-encrypted backdoor code. Once decrypted at runtime, it reveals a `startupload()` function that silently transmits the victim’s seed phrase, wallet address, and other sensitive information to attacker-controlled servers.
Implications and Recommendations
The SeaFlower campaign underscores the evolving sophistication of cyber threats targeting the cryptocurrency sector. By leveraging advanced techniques to create nearly identical clones of legitimate wallet applications, attackers can effectively deceive users and compromise their digital assets.
To mitigate the risk of such attacks, users are advised to:
1. Download Applications from Official Sources: Always obtain wallet applications directly from official websites or trusted app stores.
2. Verify Application Authenticity: Check for official developer credentials and reviews before downloading and installing applications.
3. Be Cautious with Search Engine Results: Be wary of search engine results that lead to unfamiliar websites, especially when downloading financial applications.
4. Regularly Update Software: Keep all applications and operating systems up to date to benefit from the latest security patches.
5. Monitor Account Activity: Regularly review wallet transactions for any unauthorized activity.
By adopting these practices, users can enhance their security posture and reduce the likelihood of falling victim to sophisticated campaigns like SeaFlower.