Overcoming Alert Overload: Strategies to Minimize False Positives in Cybersecurity
In the realm of cybersecurity, the prevalence of false positives—alerts that indicate a threat where none exists—poses a significant challenge. While these alerts may seem benign, they can lead to substantial operational inefficiencies and increased vulnerability to actual threats.
The Impact of False Positives
Security Operations Centers (SOCs) are inundated with alerts daily. Even a modest false positive rate can result in hours of wasted analyst time. This overload leads to:
– Alert Fatigue: Analysts become desensitized, potentially overlooking genuine threats.
– Delayed Response: Critical threats may be buried under a deluge of benign alerts.
– Operational Inefficiency: Resources are diverted from proactive security measures to unnecessary investigations.
The cumulative effect is a distorted detection pipeline, where increased alerts do not equate to enhanced visibility.
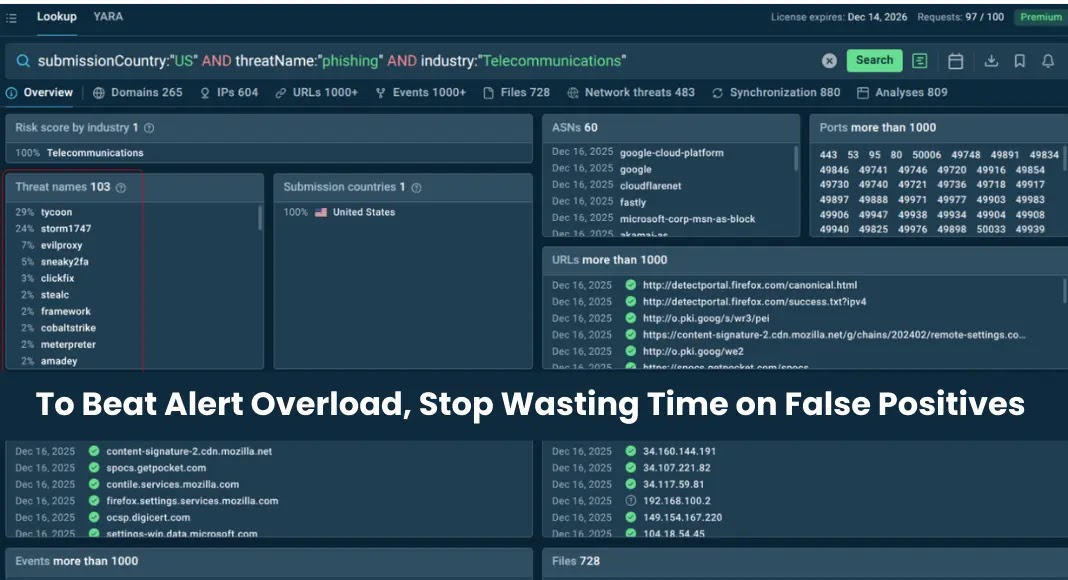
The Role of Threat Intelligence
High-quality threat intelligence is pivotal in refining the detection process. It provides:
– Accurate Indicators of Compromise (IOCs): Ensuring that alerts are based on current and relevant data.
– Contextual Information: Allowing analysts to assess the severity and relevance of alerts swiftly.
– Behavioral Signatures: Identifying patterns indicative of malicious activity.
Integrating reliable threat intelligence reduces false positives, enabling analysts to focus on genuine threats.
Implementing Effective Strategies
To combat alert overload, organizations should:
1. Enhance Threat Intelligence Feeds: Utilize sources that offer real-time, validated data to minimize outdated or irrelevant alerts.
2. Automate Routine Tasks: Implement tools that can handle repetitive tasks, allowing analysts to concentrate on complex investigations.
3. Regularly Review Detection Rules: Ensure that correlation rules are updated to reflect the evolving threat landscape, reducing unnecessary alerts.
4. Invest in Analyst Training: Equip analysts with the skills to discern between false positives and genuine threats efficiently.
5. Foster Collaboration: Encourage communication between teams to share insights and improve detection accuracy.
By adopting these strategies, organizations can enhance their cybersecurity posture, ensuring that resources are allocated effectively and genuine threats are addressed promptly.