Preparing for the Quantum Era: Safeguarding Data with Post-Quantum Cryptography
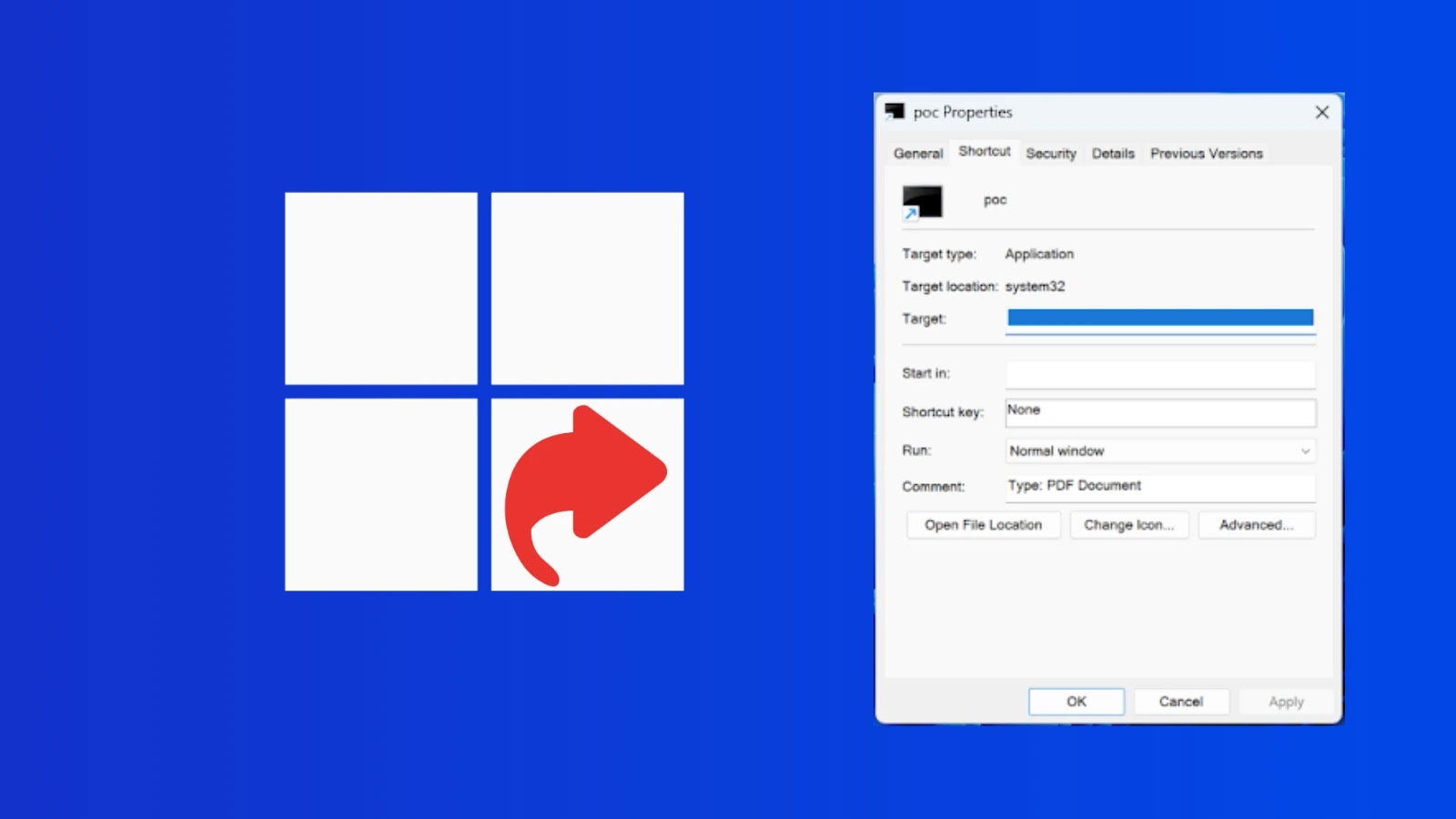
In today’s digital landscape, encryption is the cornerstone of data security, ensuring that sensitive information remains confidential and intact. However, the rapid advancement of quantum computing poses a significant threat to current encryption methods. Malicious actors are already employing a strategy known as harvest now, decrypt later, where they collect encrypted data today with the intention of decrypting it in the future using quantum computers. This means that data considered secure now could be exposed once quantum capabilities mature.
To address this looming threat, security leaders must proactively understand and implement post-quantum cryptography (PQC) strategies. An upcoming webinar titled Future-Ready Security will delve into PQC best practices, offering practical guidance on protecting data before quantum decryption becomes feasible.
The Imperative of Post-Quantum Cryptography
Quantum computing is progressing at an unprecedented pace, and it’s only a matter of time before it can break widely used encryption algorithms like RSA and ECC. For organizations that handle sensitive data requiring long-term confidentiality—such as financial records, intellectual property, and government communications—waiting until quantum computers become a reality is not an option.
A viable solution emerging today is hybrid cryptography, which integrates traditional encryption methods with quantum-resistant algorithms like Module-Lattice-based Key-Encapsulation Mechanism (ML-KEM). This approach enhances security without disrupting existing systems, providing a seamless transition to quantum-safe protections.
The Future-Ready Security webinar will provide insights into how hybrid cryptography functions in real-world environments and guide organizations on initiating the shift to quantum-resistant security measures.
Steps to Prepare for the Quantum Era
Organizations aiming to fortify their defenses against quantum threats should focus on the following key steps:
1. Identify Sensitive Data: Determine which data assets require long-term protection and could be vulnerable to future quantum attacks.
2. Assess Encryption Usage: Conduct a comprehensive audit to understand where and how encryption is applied across all systems and processes.
3. Adopt Hybrid Cryptography: Begin integrating hybrid cryptographic strategies that combine existing encryption methods with quantum-resistant algorithms.
4. Ensure Compliance and Visibility: Maintain clear oversight of cryptographic algorithms in use and ensure adherence to evolving compliance requirements.
Simultaneously, security teams must continue to monitor encrypted traffic and enforce policies across their networks. Implementing modern Zero Trust architectures is crucial in maintaining control and ensuring that only authorized entities have access to sensitive data.
These strategies, along with practical implementations by platforms like Zscaler, will be thoroughly discussed during the live webinar session tailored for IT, security, and networking leaders.
Key Takeaways from the Webinar
Participants of the webinar can expect to gain:
– Understanding of Harvest Now, Decrypt Later Attacks: Insights into the growing risk posed by adversaries collecting encrypted data for future decryption using quantum computers.
– Knowledge of ML-KEM Hybrid Encryption: An exploration of how ML-KEM hybrid encryption facilitates a safe transition to quantum-resistant security measures.
– Post-Quantum Traffic Inspection Techniques: Strategies for enforcing security policies at scale through post-quantum traffic inspection.
– Best Practices for Quantum-Era Data Protection: Practical steps and methodologies to safeguard sensitive data in anticipation of quantum advancements.
The advent of quantum computing is set to revolutionize cybersecurity. Organizations that take proactive steps now will be better positioned to protect their most critical data assets in the future.
Join the webinar to learn how to develop a practical, quantum-ready security strategy before the threat becomes imminent.