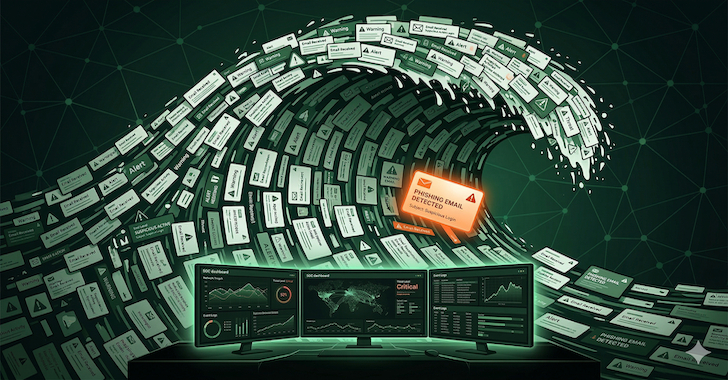
Phishing Attacks Evolve: Overwhelming SOCs to Breach Defenses
In the ever-evolving landscape of cyber threats, phishing attacks have transcended their traditional boundaries. No longer solely focused on deceiving individual employees, sophisticated attackers now aim to inundate Security Operations Centers (SOCs) with a deluge of phishing attempts, effectively weaponizing the investigative workload of cybersecurity teams. This strategic shift poses a significant challenge: when the time required to investigate a phishing incident escalates from mere minutes to several hours, the risk of a contained incident escalating into a full-scale breach increases exponentially.
The Traditional Focus on Phishing Defense
Historically, organizations have concentrated their phishing defense strategies on frontline measures:
– Employee Training: Educating staff to recognize and report suspicious emails.
– Email Gateways: Implementing filters to block known phishing threats.
– Reporting Programs: Encouraging users to flag potential phishing attempts for further analysis.
While these measures are essential, they primarily address the initial stages of a phishing attack. Less attention has been given to the subsequent investigative processes within SOCs, a gap that attackers are increasingly exploiting.
The Emergence of Informational Denial-of-Service (IDoS) Attacks
A concerning trend has emerged where attackers orchestrate high-volume phishing campaigns not just to compromise individual targets but to overwhelm the SOCs responsible for investigating these threats. This tactic, known as Informational Denial-of-Service (IDoS), leverages the finite capacity of SOCs, turning their workload into an attack vector.
How IDoS Attacks Unfold
1. Mass Phishing Campaigns: Attackers dispatch thousands of generic phishing emails. While many are intercepted by email filters or identified by trained employees, they generate a substantial number of alerts and reports.
2. SOC Overload: The influx of reports inundates the SOC, creating a backlog that analysts struggle to manage.
3. Targeted Spear-Phishing: Amidst the chaos, attackers send carefully crafted spear-phishing emails to specific individuals with access to critical systems. These targeted attacks are more likely to slip through the overwhelmed investigative process.
This method effectively serves as a denial-of-service attack against the SOC’s attention and resources, allowing the most dangerous threats to evade detection.
The Predictable Failure Mode of SOCs
The success of IDoS attacks hinges on the predictable responses of SOCs to high-volume phishing incidents:
– Reduced Investigation Depth: Analysts, under pressure to clear the growing queue, may spend less time on each report, leading to superficial investigations.
– Deprioritization of Phishing Reports: Managers might prioritize other alerts over user-submitted phishing reports, assuming the latter are of lower fidelity.
– Anchoring Bias: Analysts may rely on familiar indicators, potentially overlooking novel threats embedded within the flood of reports.
These responses, while individually rational, collectively create an environment where sophisticated phishing attacks can thrive.
Strategic Recommendations for SOCs
To counteract the evolving tactics of phishing attackers, SOCs must adopt a more resilient and adaptive approach:
1. Implement Advanced Automation:
– Automated Triage: Deploy systems capable of initial triage, categorizing and prioritizing phishing reports based on predefined criteria.
– Machine Learning Models: Utilize models trained to identify and flag high-risk phishing attempts, reducing the manual workload on analysts.
2. Enhance Analyst Training:
– Recognize IDoS Tactics: Educate analysts on the signs of IDoS attacks and the importance of maintaining thorough investigative practices, even under pressure.
– Adaptive Investigation Techniques: Train analysts to adjust their investigative depth based on the evolving threat landscape, ensuring critical threats are not overlooked.
3. Optimize Resource Allocation:
– Dynamic Staffing: Implement flexible staffing models that allow for rapid scaling of resources in response to surges in phishing reports.
– Cross-Training: Ensure team members are cross-trained to handle various aspects of phishing investigations, promoting agility and resilience.
4. Develop Robust Incident Response Plans:
– Scenario Planning: Regularly conduct exercises simulating high-volume phishing attacks to test and refine response strategies.
– Continuous Improvement: Establish feedback loops to learn from each incident, continuously enhancing the SOC’s capabilities.
Conclusion
The landscape of phishing attacks is rapidly evolving, with adversaries employing tactics designed to exploit not just individual vulnerabilities but also systemic weaknesses within SOCs. By recognizing and adapting to these sophisticated strategies, organizations can fortify their defenses, ensuring that their SOCs remain resilient in the face of increasingly complex cyber threats.