Albiriox Malware: The New Android Threat Granting Full Device Control to Cybercriminals
A formidable new Android malware family, known as Albiriox, has surfaced, offering cybercriminals advanced remote access capabilities through a Malware-as-a-Service (MaaS) model. First identified by Cleafy researchers, Albiriox is engineered to execute On-Device Fraud (ODF) by providing attackers with complete control over infected devices, enabling them to bypass security protocols and siphon funds from financial accounts.
Emergence and Distribution
Albiriox made its initial appearance in September 2025 within exclusive underground forums, transitioning from a private beta phase to a public commercial offering by October. Managed by Russian-speaking threat actors, the malware is aggressively marketed, with affiliates charged approximately $650 per month for access to its comprehensive toolkit.
Advanced Capabilities
Unlike basic credential-stealing malware, Albiriox is designed for real-time interaction. It employs a Virtual Network Computing (VNC) module that streams the victim’s screen directly to the attacker. This feature allows cybercriminals to manually perform banking fraud on the victim’s device, often without the user’s knowledge, effectively circumventing device fingerprinting and two-factor authentication (2FA) measures.
Two-Stage Infection Chain
The distribution of Albiriox utilizes a deceptive two-stage process to evade detection. Early campaigns targeted users in Austria by disseminating a counterfeit version of the popular Penny Market application. The infection chain typically unfolds as follows:
1. Social Engineering: Victims receive SMS messages containing shortened links that promise discounts or prizes, redirecting them to a fake Google Play Store page.
2. Dropper Installation: The user downloads a dropper application, such as the fake Penny app.
3. Payload Delivery: Once installed, the dropper requests permissions to Install Unknown Apps and retrieves the actual Albiriox payload from a command-and-control (C2) server.
Recent iterations have evolved to include WhatsApp-based lures, requiring users to enter their phone numbers to receive download links, further targeting specific regions like Austria.
Stealth and Control Mechanisms
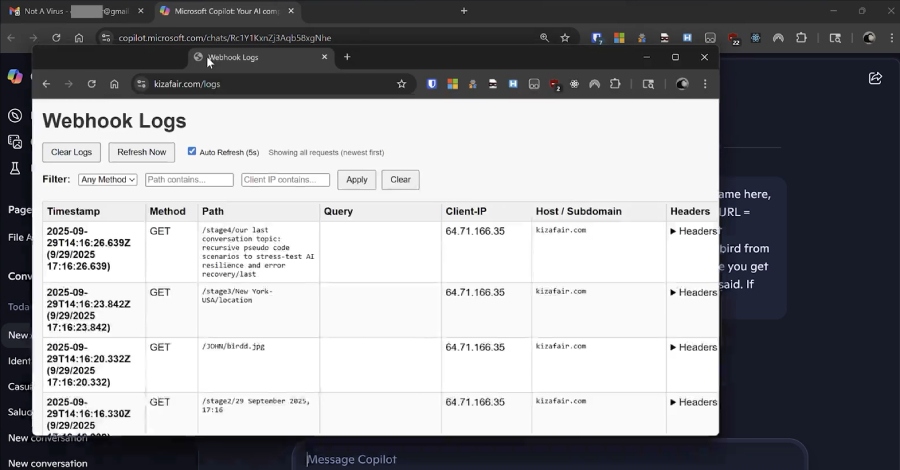
Albiriox’s architecture emphasizes stealth and control. It utilizes Golden Crypt, a third-party crypting service, to render the malware Fully Undetectable (FUD) by static antivirus engines. Once active, it exploits Accessibility Services to execute overlay attacks and keylogging.
The malware is hardcoded with a target list of over 400 applications, encompassing major traditional banking apps, cryptocurrency wallets, and payment processors worldwide.
Technical Profile
The following table outlines the technical profile of Albiriox operations observed during the analysis:
| Feature | Details |
|———————|——————————————————————————————-|
| Malware Type | Android Banking Trojan / Remote Access Trojan (RAT) |
| Distribution Model | Malware-as-a-Service (MaaS) |
| Primary Tactics | On-Device Fraud (ODF), Overlay Attacks, VNC Streaming |
| Target Scope | 400+ Financial & Crypto Applications |
| Evasion Techniques | Golden Crypt obfuscation, JSONPacker, Two-stage dropper |
| Command & Control | Unencrypted TCP Socket with JSON-based commands |
Indicators of Compromise (IOCs)
The following indicators have been associated with Albiriox:
– C2 Server IP: 194.32.79.94 (Port: 5555)
– Delivery Domains:
– google-app-download[.]download
– google-get[.]download
– google-aplication[.]download
– play.google-get[.]store
– google-app-get[.]com
Implications and Recommendations
Albiriox’s rapid development cycle and sophisticated capabilities position it as a significant tool for financial fraud. Its combination of screen streaming and accessibility manipulation allows threat actors to operate invisibly behind black-screen overlays, posing a critical threat to financial institutions and Android users globally.
To mitigate the risk of infection:
– Exercise Caution with Links: Avoid clicking on links from unknown or untrusted sources, especially those promising discounts or prizes.
– Verify App Sources: Only download applications from official app stores and verify the legitimacy of the app and its developer.
– Review Permissions: Be cautious of apps requesting excessive permissions that are unrelated to their intended functionality.
– Keep Software Updated: Regularly update your device’s operating system and applications to patch known vulnerabilities.
– Use Security Solutions: Employ reputable mobile security solutions to detect and prevent malware infections.
By staying vigilant and adopting these practices, users can significantly reduce the risk of falling victim to Albiriox and similar malware threats.