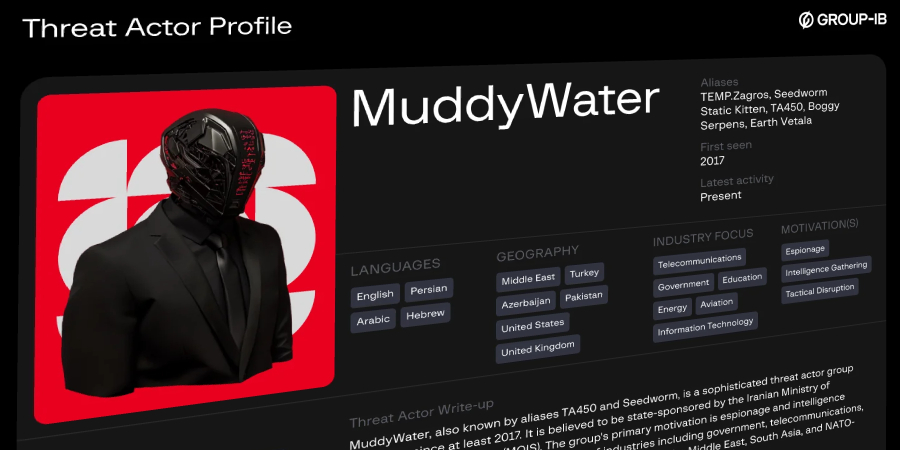
MuddyWater’s New Cyber Offensive: Unveiling Operation Olalampo in the MENA Region
The Iranian state-sponsored cyber espionage group known as MuddyWater, also referred to as Earth Vetala, Mango Sandstorm, and MUDDYCOAST, has initiated a sophisticated cyber campaign dubbed Operation Olalampo. This operation, first detected on January 26, 2026, has primarily targeted organizations and individuals across the Middle East and North Africa (MENA) region. The campaign is characterized by the deployment of novel malware families, including GhostFetch, HTTP_VIP, CHAR, and GhostBackDoor, marking a significant evolution in MuddyWater’s cyber arsenal.
The Emergence of Operation Olalampo
Operation Olalampo represents a strategic escalation in MuddyWater’s cyber activities. The campaign employs a series of meticulously crafted phishing emails, each containing malicious Microsoft Office documents embedded with macro codes. When recipients enable these macros, the embedded payloads are decoded, dropped onto the system, and executed, granting the attackers remote control over the compromised systems. This method aligns with previously observed tactics employed by MuddyWater, underscoring the group’s reliance on social engineering to initiate their attack chains.
Unpacking the Malware Arsenal
The operation introduces several new malware tools, each designed to perform specific functions within the attack framework:
1. GhostFetch: Serving as a first-stage downloader, GhostFetch conducts an initial reconnaissance of the infected system. It validates user activity through mouse movements and screen resolution checks, detects the presence of debuggers, virtual machines, and antivirus software, and subsequently fetches and executes secondary payloads directly in memory.
2. GhostBackDoor: Delivered by GhostFetch, this second-stage backdoor provides the attackers with an interactive shell, enabling file read/write operations and the capability to re-run GhostFetch, thereby maintaining persistent access to the compromised system.
3. HTTP_VIP: This native downloader performs system reconnaissance and connects to an external server to authenticate and deploy the AnyDesk remote desktop software. A newer variant of HTTP_VIP has expanded functionalities, including the ability to retrieve victim information, initiate an interactive shell, download and upload files, capture clipboard contents, and adjust the sleep or beaconing interval to evade detection.
4. CHAR: A Rust-based backdoor controlled via a Telegram bot named Olalampo, CHAR allows attackers to change directories and execute commands through cmd.exe or PowerShell. It is designed to execute a SOCKS5 reverse proxy or another backdoor named Kalim, upload data stolen from web browsers, and run additional executables referred to as sh.exe and gshdoc_release_X64_GUI.exe.
The Role of Artificial Intelligence in Malware Development
An intriguing aspect of CHAR is the evidence suggesting the use of artificial intelligence (AI) in its development. Analysis of CHAR’s source code revealed the presence of emojis in debug strings, a characteristic indicative of AI-assisted coding practices. This finding aligns with previous reports indicating that MuddyWater has been experimenting with generative AI tools to facilitate the creation of custom malware capable of file transfer and remote execution. The incorporation of AI into malware development signifies a concerning advancement in the capabilities of state-sponsored threat actors, enabling them to produce more sophisticated and adaptable malicious tools.
Comparative Analysis with Previous Campaigns
Operation Olalampo is not an isolated incident but rather a continuation of MuddyWater’s persistent cyber activities targeting the MENA region. In December 2025, ESET researchers identified MuddyWater’s attacks on critical infrastructure in Israel and Egypt, where the group deployed a new backdoor named MuddyViper. This backdoor was delivered using a loader called Fooder, which reflectively loaded the payload into memory to evade detection. The campaign primarily targeted sectors such as technology, engineering, manufacturing, local government, and education.
Similarly, in October 2025, MuddyWater orchestrated a large-scale cyber-espionage campaign targeting over 100 government organizations across the Middle East, North Africa, and select international regions. This operation involved highly targeted phishing emails delivering the Phoenix v4 backdoor, alongside custom infostealers and legitimate remote management tools. The attackers demonstrated advanced persistence, credential theft, and data exfiltration capabilities, underscoring the evolving threat landscape facing government and diplomatic entities.
Mitigation Strategies and Recommendations
Given the sophisticated nature of MuddyWater’s operations, organizations, particularly those within the MENA region, must adopt comprehensive cybersecurity measures to mitigate the risks associated with such advanced persistent threats. Key recommendations include:
– User Education and Awareness: Conduct regular training sessions to educate employees about the dangers of phishing attacks and the importance of not enabling macros in unsolicited documents.
– Email Filtering and Verification: Implement robust email filtering solutions to detect and block phishing emails. Verify the authenticity of emails, especially those containing attachments or links, before opening them.
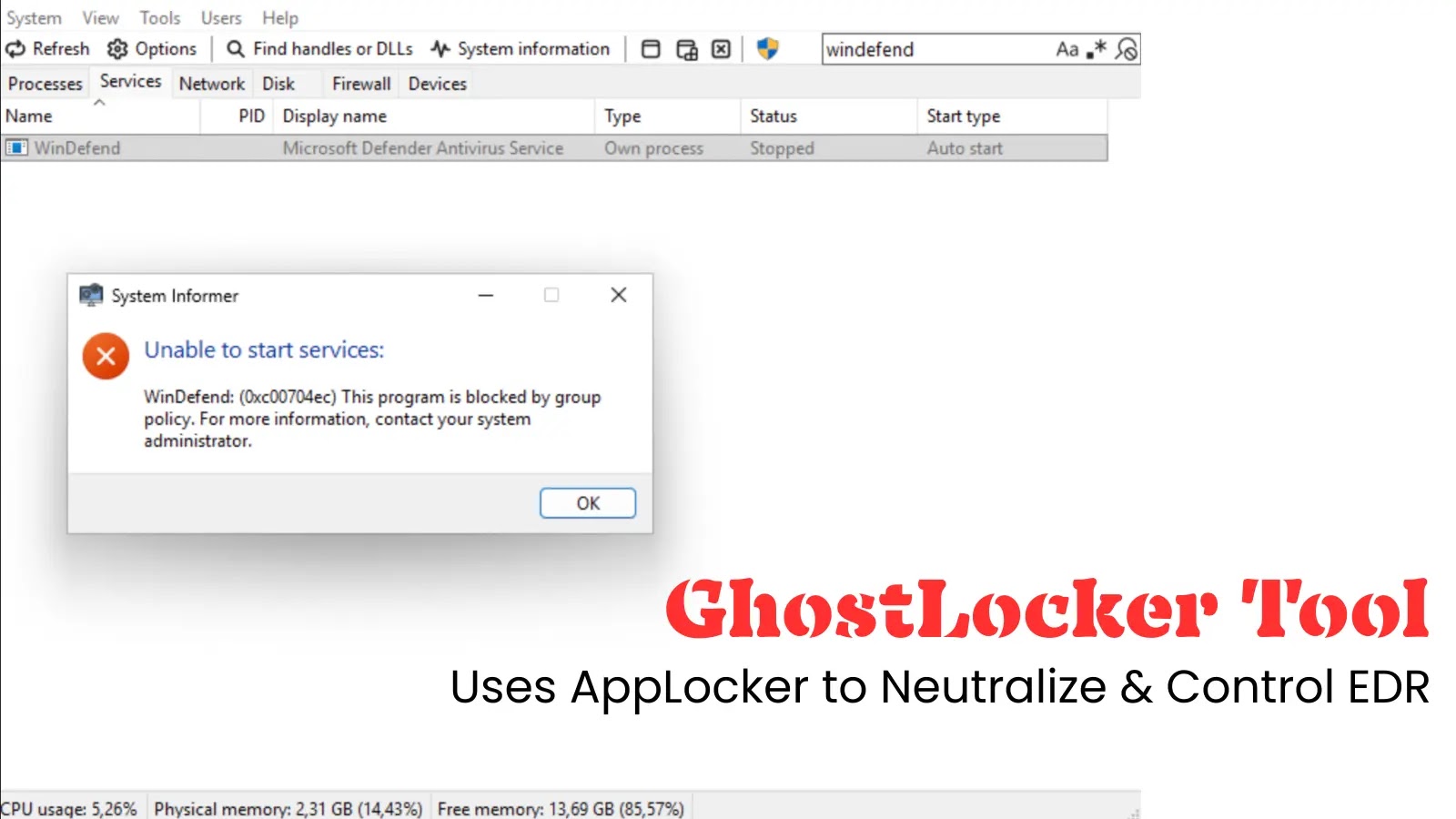
– Endpoint Protection: Deploy advanced endpoint detection and response (EDR) solutions capable of identifying and mitigating malicious activities in real-time.
– Regular Software Updates: Ensure that all systems and software are up-to-date with the latest security patches to prevent exploitation of known vulnerabilities.
– Network Segmentation: Implement network segmentation to limit the lateral movement of attackers within the organization’s infrastructure.
– Incident Response Planning: Develop and regularly update incident response plans to ensure a swift and effective response to potential security breaches.
Conclusion
MuddyWater’s Operation Olalampo exemplifies the evolving tactics and tools employed by state-sponsored cyber espionage groups. The introduction of new malware families and the potential use of AI in malware development highlight the increasing sophistication of cyber threats. Organizations within the MENA region and beyond must remain vigilant, continuously enhance their cybersecurity posture, and adopt proactive measures to defend against such advanced persistent threats.