Microsoft Uncovers Sophisticated ClickFix Campaign Exploiting Windows Terminal to Deploy Lumma Stealer
In February 2026, Microsoft’s Threat Intelligence team identified a widespread ClickFix social engineering campaign that leverages the Windows Terminal application to execute a complex attack chain, culminating in the deployment of the Lumma Stealer malware. ([linkedin.com](https://www.linkedin.com/posts/microsoft-threat-intelligence_microsoft-defender-experts-identified-a-widespread-activity-7435454977893924864-u9Zh?utm_source=openai))
Evolution of ClickFix Tactics
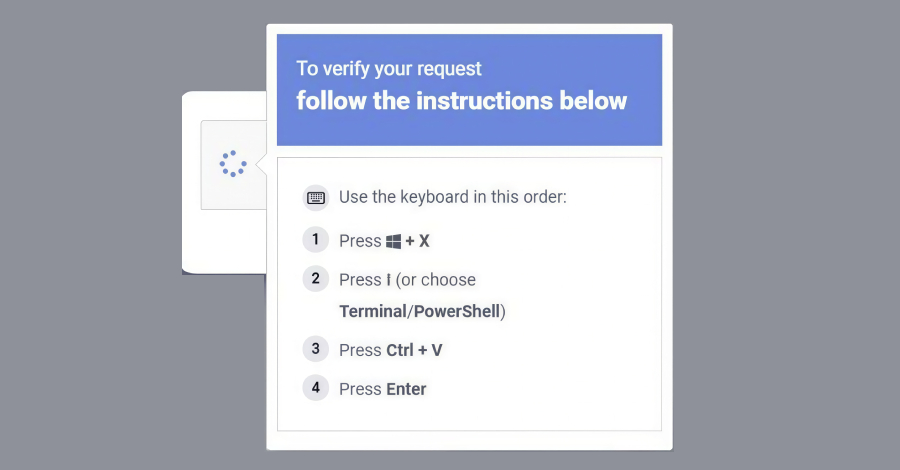
Traditionally, ClickFix campaigns have deceived users into opening the Windows Run dialog (Win + R) and pasting malicious commands. However, this latest variant instructs targets to use the Windows + X → I shortcut to launch Windows Terminal (wt.exe) directly. This method guides users into a privileged command execution environment that blends seamlessly into legitimate administrative workflows, thereby appearing more trustworthy. ([linkedin.com](https://www.linkedin.com/posts/microsoft-threat-intelligence_microsoft-defender-experts-identified-a-widespread-activity-7435454977893924864-u9Zh?utm_source=openai))
Attack Chain Details
Once the terminal is opened, victims are prompted to paste a hex-encoded, XOR-compressed PowerShell command delivered through fake CAPTCHA pages, troubleshooting prompts, or verification-style lures designed to appear routine and benign. Executing this command initiates a multi-stage attack chain:
1. Decoding and Execution: The pasted command spawns additional Terminal/PowerShell instances to decode the script.
2. Payload Retrieval: A ZIP payload and a legitimate but renamed 7-Zip binary are downloaded.
3. Extraction and Deployment: The 7-Zip utility extracts the contents of the ZIP file, triggering further payloads.
4. Persistence and Evasion: The malware sets up persistence via scheduled tasks, configures Microsoft Defender exclusions, and exfiltrates machine and network data.
5. Malware Deployment: Lumma Stealer is deployed using the QueueUserAPC() technique, injecting the malware into chrome.exe and msedge.exe processes. ([linkedin.com](https://www.linkedin.com/posts/microsoft-threat-intelligence_microsoft-defender-experts-identified-a-widespread-activity-7435454977893924864-u9Zh?utm_source=openai))
Lumma Stealer Capabilities
Lumma Stealer targets high-value browser artifacts, including Web Data and Login Data, harvesting stored credentials and exfiltrating them to attacker-controlled infrastructure. ([linkedin.com](https://www.linkedin.com/posts/microsoft-threat-intelligence_microsoft-defender-experts-identified-a-widespread-activity-7435454977893924864-u9Zh?utm_source=openai))
Alternative Attack Pathway
Microsoft also detected a second attack pathway wherein the compressed command, when pasted into Windows Terminal, downloads a randomly named batch script to the AppData\Local folder. This script writes a Visual Basic Script to the Temp folder and executes it via cmd.exe with the /launched command-line argument. The batch script is then executed through MSBuild.exe, resulting in LOLBin abuse. The script connects to Crypto Blockchain RPC endpoints, indicating an etherhiding technique, and performs QueueUserAPC()-based code injection into chrome.exe and msedge.exe processes to harvest Web Data and Login Data. ([linkedin.com](https://www.linkedin.com/posts/microsoft-threat-intelligence_microsoft-defender-experts-identified-a-widespread-activity-7435454977893924864-u9Zh?utm_source=openai))
Implications and Recommendations
This campaign underscores the evolving sophistication of social engineering attacks, particularly those exploiting trusted system utilities like Windows Terminal. Users and organizations are advised to exercise caution when prompted to execute commands, even within seemingly legitimate contexts. Implementing robust security measures, including user education and advanced threat detection systems, is crucial to mitigating such threats.