Malicious Rust Crates and AI Bot Compromise CI/CD Pipelines to Steal Developer Secrets
In a recent cybersecurity development, researchers have identified five malicious Rust crates designed to infiltrate Continuous Integration/Continuous Deployment (CI/CD) pipelines and exfiltrate sensitive developer information. These crates, masquerading as time-related utilities, were uploaded to the Rust package registry, crates.io, between late February and early March 2026.
Identified Malicious Crates:
– chrono_anchor
– dnp3times
– time_calibrator
– time_calibrators
– time-sync
These packages were designed to impersonate legitimate time synchronization utilities, specifically mimicking the services of timeapi.io. The threat actor behind these crates utilized a lookalike domain, timeapis[.]io, to collect the exfiltrated data, indicating a coordinated effort to deceive developers and steal sensitive information.
Mechanism of Attack:
Upon integration into a developer’s environment, these malicious crates targeted `.env` files, which commonly store API keys, tokens, and other confidential credentials. The crates would extract the contents of these files and transmit them to the attacker’s server. Notably, the chrono_anchor crate employed advanced obfuscation techniques to evade detection. It embedded its exfiltration code within a file named guard.rs, which was invoked through an optional sync helper function, making it less likely to raise suspicion during code reviews.
Unlike traditional malware that establishes persistence on the host system, these crates were designed to execute their payloads each time a developer’s CI workflow called the malicious code. This approach ensured repeated exfiltration of secrets without leaving persistent traces on the developer’s machine.
Implications for Developers:
The targeting of `.env` files is particularly concerning due to the sensitive nature of the data they contain. By accessing these files, attackers can compromise downstream users and gain unauthorized access to various services, including cloud platforms, databases, and code repositories. This breach underscores the critical need for developers to exercise caution when integrating third-party packages into their projects.
Recommended Actions:
Developers who have incorporated any of the aforementioned crates into their projects should assume that their credentials may have been compromised. Immediate steps should include:
– Rotating Keys and Tokens: Generate new API keys, tokens, and other credentials to replace potentially compromised ones.
– Auditing CI/CD Pipelines: Review and monitor CI/CD jobs that utilize publish or deploy credentials to ensure no unauthorized access has occurred.
– Restricting Outbound Network Access: Implement network policies to limit outbound connections from build environments, reducing the risk of data exfiltration.
This incident highlights the importance of implementing robust security measures within the software supply chain. As Socket, the security firm that identified the malicious crates, emphasized:
This campaign shows that low-complexity supply chain malware can still deliver high-impact when it runs inside developer workspaces and CI jobs. Prioritize controls that stop malicious dependencies before they execute.
AI-Powered Bot Exploits GitHub Actions:
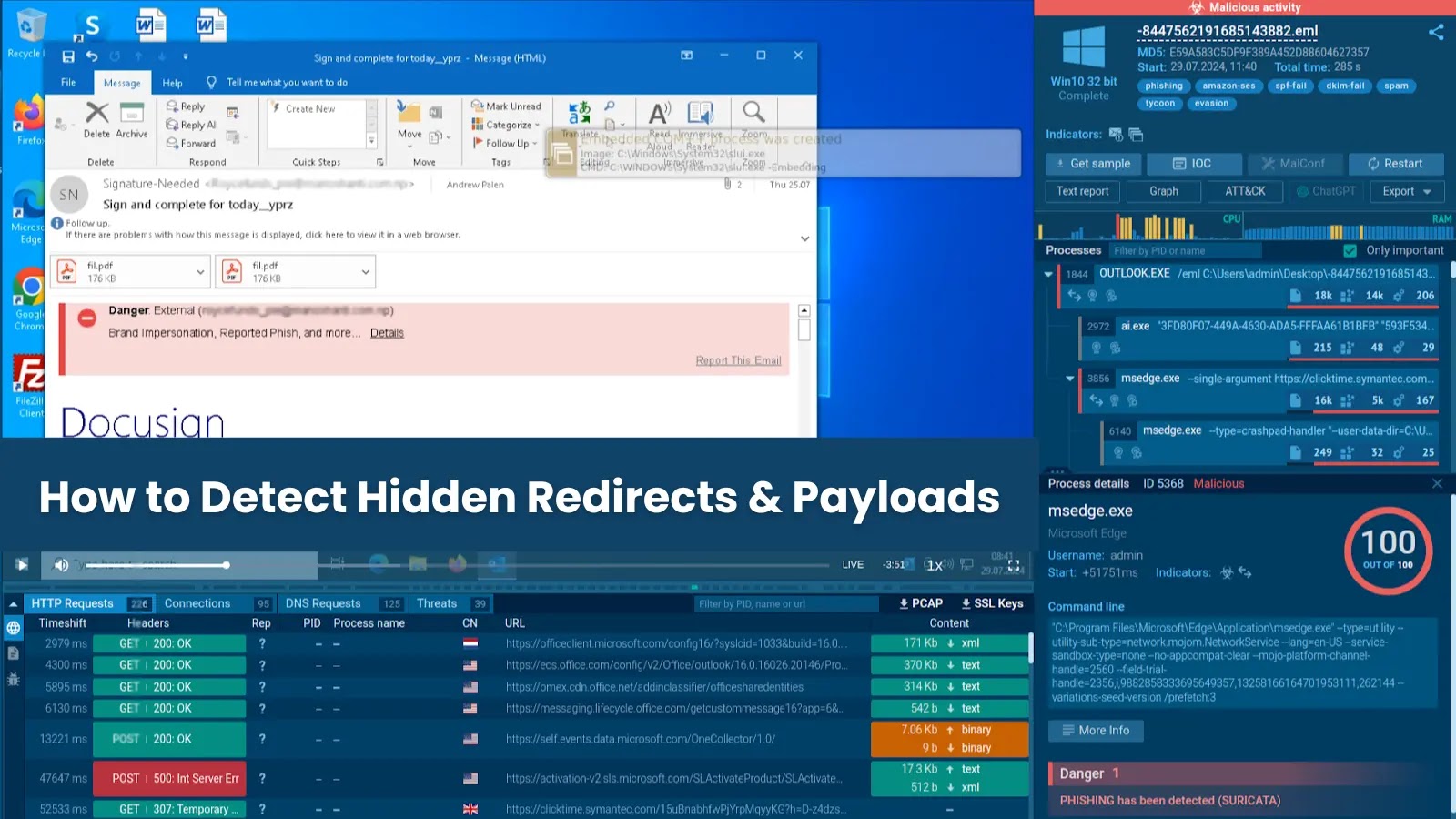
In a related development, an automated attack campaign has been discovered targeting CI/CD pipelines across major open-source repositories. An AI-powered bot, identified as hackerbot-claw, has been scanning public repositories for exploitable GitHub Actions workflows to harvest developer secrets.
Attack Methodology:
Between February 21 and February 28, 2026, the bot targeted at least seven repositories belonging to organizations such as Microsoft, Datadog, and Aqua Security. The attack sequence involved:
1. Scanning Public Repositories: Identifying misconfigured CI/CD pipelines within public repositories.
2. Forking Target Repositories: Creating forks of the target repositories and preparing malicious payloads.
3. Opening Pull Requests: Submitting pull requests with minor changes, such as typo corrections, while embedding the malicious payload within the branch name, file name, or CI script.
4. Triggering CI Pipelines: Exploiting the automatic activation of workflows on pull requests to execute the malicious code on the build server.
Protective Measures:
To safeguard against such sophisticated attacks, developers and organizations should:
– Review CI/CD Configurations: Ensure that workflows are configured securely and do not automatically execute code from untrusted sources.
– Implement Code Review Processes: Establish thorough code review protocols to detect and prevent the inclusion of malicious code.
– Monitor Repository Activity: Keep an eye on repository activities, especially pull requests from unfamiliar contributors, for any signs of suspicious behavior.
These incidents serve as a stark reminder of the evolving threats within the software development ecosystem. As attackers continue to devise new methods to infiltrate development environments, it is imperative for developers and organizations to remain vigilant and adopt comprehensive security practices to protect their codebases and sensitive information.