Unsecured Tire Pressure Systems in Major Car Brands Enable Covert Vehicle Tracking
Recent research has unveiled significant privacy vulnerabilities in Tire Pressure Monitoring Systems (TPMS) used by leading automotive manufacturers, including Toyota, Renault, Hyundai, and Mercedes. These systems, designed to enhance vehicle safety by monitoring tire pressure, inadvertently expose drivers to potential tracking risks due to unencrypted data transmissions.
Understanding TPMS and Its Vulnerabilities
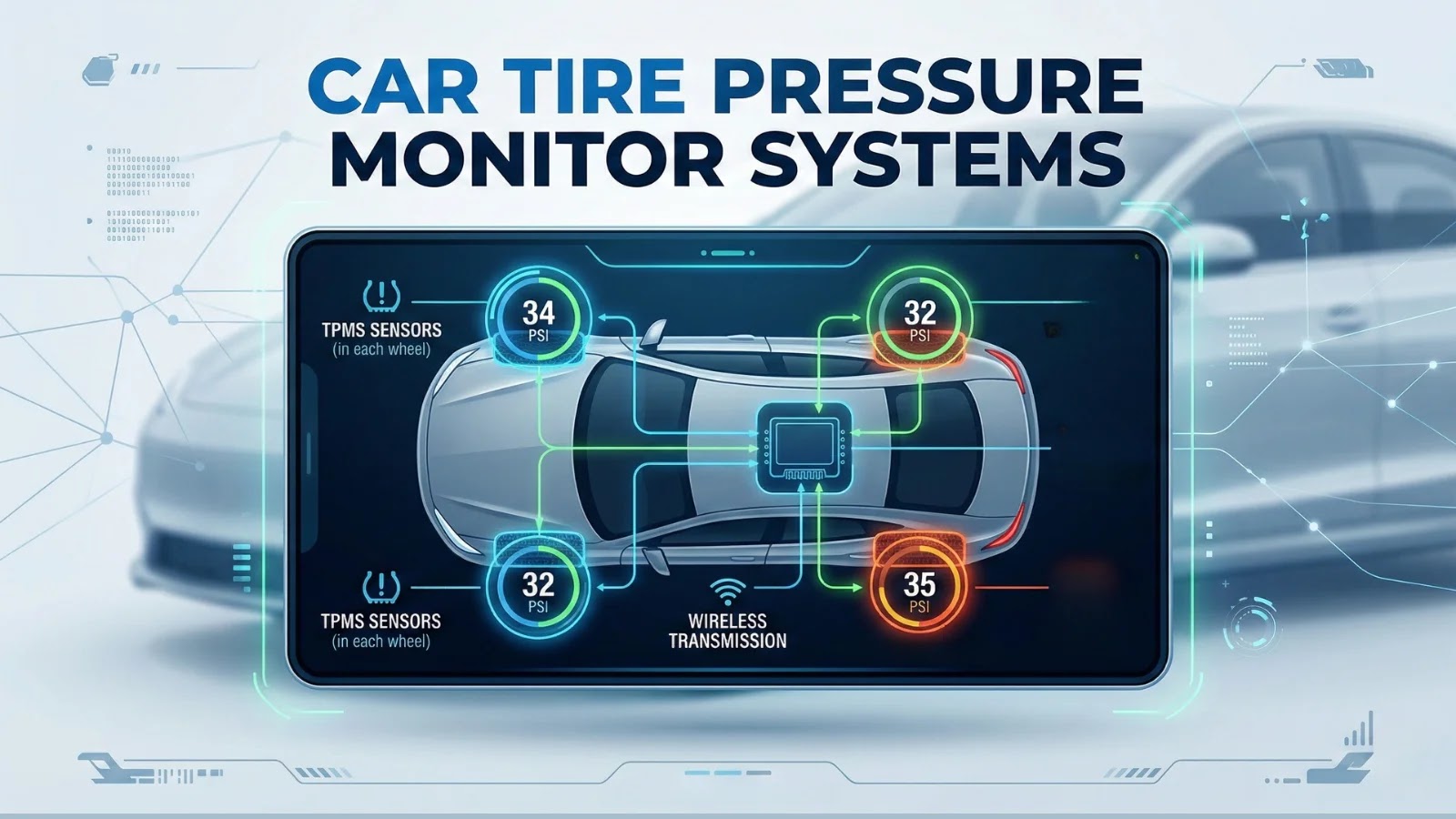
TPMS are integral to modern vehicles, ensuring optimal tire pressure for safety and efficiency. There are two primary types:
1. Direct TPMS (dTPMS): Utilizes sensors within each tire to measure pressure and temperature, transmitting data wirelessly to the vehicle’s onboard system.
2. Indirect TPMS (iTPMS): Relies on wheel speed sensors to detect variations that may indicate under-inflation.
The study focused on dTPMS, which, unlike iTPMS, transmits data that can be intercepted due to the lack of encryption.
The Scope of the Study
Researchers from IMDEA Networks and collaborating institutions conducted a comprehensive 10-week analysis, capturing over 6 million signals from approximately 20,000 vehicles. Utilizing affordable equipment—specifically, $100 receivers—they demonstrated the feasibility of passive tracking through unencrypted TPMS data.
Technical Insights into dTPMS Vulnerabilities
dTPMS sensors operate by broadcasting data at frequencies of 315 or 433 MHz, with a transmission rate of 20 kbps. The data packets include:
– Tire pressure
– Temperature
– Battery status
– A unique identifier (24-32 bit ID)
This information is transmitted in cleartext, making it susceptible to interception. The study revealed that these signals could be captured from distances up to 55 meters, even without a direct line of sight. Transmission intervals vary by manufacturer, occurring every 30 to 120 seconds while driving and, for some brands, hourly when parked.
Manufacturer-Specific Findings
The research highlighted differences in TPMS implementations among manufacturers:
– Toyota: Employs dTPMS with continuous broadcasts, including hourly transmissions when the vehicle is stationary.
– Renault: Utilizes motion-triggered dTPMS, resulting in less frequent transmissions when the vehicle is not in motion.
– Hyundai: Features unencrypted IDs in their dTPMS, making them particularly vulnerable to data capture via software-defined radios (SDRs).
– Mercedes: Uses proprietary protocols with cleartext pressure data, posing similar privacy concerns.
Implications of Unsecured TPMS Data
The unencrypted nature of dTPMS transmissions presents several privacy risks:
– Vehicle Tracking: Persistent unique IDs allow for the monitoring of vehicle movements and routines, potentially revealing sensitive information such as work schedules, travel habits, and frequented locations.
– Personal Data Exposure: By correlating TPMS data with other information sources, malicious actors could identify vehicle owners, leading to targeted surveillance or theft.
– Security Threats: The ability to track vehicles covertly could facilitate criminal activities, including stalking, burglary (by determining when a vehicle is away from home), or corporate espionage.
Methodology of the Study
To assess the extent of these vulnerabilities, researchers deployed five RTL-SDR receivers connected to Raspberry Pi devices, each costing approximately $100. These receivers were strategically placed indoors near roadways, covering an area of 10,050 square meters. Over the 10-week period, the system captured and analyzed TPMS signals, successfully identifying and tracking 12 verified vehicles.
Vehicle Identification Techniques
The researchers employed advanced data analysis methods to match tire signals to specific vehicles. By analyzing the co-occurrence of TPMS IDs within short time frames, they could accurately cluster signals belonging to the same vehicle. This approach proved effective even with sparse data, demonstrating the feasibility of vehicle identification through TPMS signals.
Regulatory Landscape and Industry Response
Despite the critical role of TPMS in vehicle safety, current regulations, such as the United Nations Regulation No. 155, do not mandate encryption for TPMS data. This regulatory gap leaves a significant number of vehicles vulnerable to passive tracking. While some manufacturers have begun exploring more secure systems, such as Pirelli and Bosch’s Cyber Tyre utilizing Bluetooth Low Energy (BLE), these solutions are not yet widespread and may still be susceptible to eavesdropping.
Recommendations for Mitigating Privacy Risks
To address these vulnerabilities, the following measures are recommended:
– Manufacturers:
– Implement Encryption: Encrypt TPMS data transmissions to prevent unauthorized interception.
– Rotate Identifiers: Regularly change unique IDs to reduce the risk of persistent tracking.
– Adopt Low-Power Modes: Utilize transmission methods that minimize unnecessary broadcasts, especially when the vehicle is stationary.
– Policymakers:
– Update Regulations: Revise existing vehicle safety standards to include requirements for TPMS data security, ensuring that privacy considerations are addressed alongside safety concerns.
– Drivers:
– Verify TPMS Security: Use TPMS diagnostic tools to check for unencrypted transmissions and consult with manufacturers about potential security updates.
– Consider Aftermarket Solutions: Explore the availability of aftermarket TPMS sensors that offer enhanced security features, though their effectiveness may vary.
Conclusion
The study underscores a significant privacy vulnerability in the TPMS of several major car brands, highlighting the need for immediate action from manufacturers, regulators, and consumers. As vehicles become increasingly connected, ensuring the security of all onboard systems is paramount to protect user privacy and prevent potential misuse of vehicle data.