Konni APT Exploits KakaoTalk to Spread EndRAT Malware via Spear-Phishing
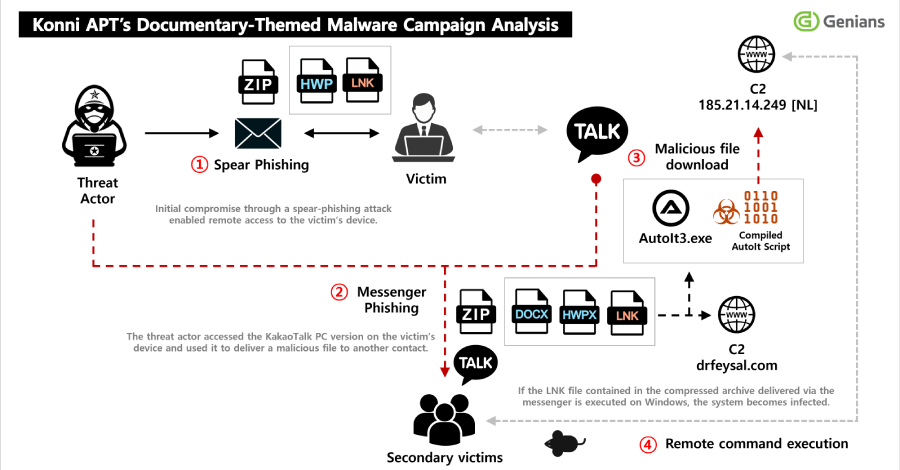
The North Korean cyber espionage group known as Konni has been identified leveraging spear-phishing tactics to infiltrate systems and exploit the KakaoTalk messaging application for malware dissemination. This sophisticated campaign underscores the group’s evolving strategies in cyber warfare.
Initial Intrusion via Spear-Phishing
Konni’s recent operations commence with meticulously crafted spear-phishing emails. These emails are designed to appear as official communications, such as notifications appointing recipients as lecturers on North Korean human rights. The primary objective is to deceive targets into opening malicious attachments.
Upon opening the attached ZIP file, victims encounter a Windows shortcut (LNK) file. Executing this file initiates a sequence that downloads additional payloads from external servers. To maintain persistence, the malware establishes scheduled tasks, ensuring its continued operation on the compromised system. Simultaneously, a decoy PDF document is displayed to divert the user’s attention from the malicious activities occurring in the background.
Deployment of EndRAT Malware
Central to this campaign is the deployment of EndRAT, also known as EndClient RAT. This remote access trojan, written in AutoIt, equips attackers with comprehensive control over the infected host. Its capabilities include:
– File Management: Accessing, modifying, and transferring files.
– Remote Shell Access: Executing commands remotely.
– Data Exfiltration: Extracting sensitive information.
– Persistence Mechanisms: Ensuring the malware remains active through system reboots.
The presence of additional malicious artifacts, such as RftRAT and Remcos RAT, indicates Konni’s intent to establish robust and redundant access points within the compromised environment.
Exploitation of KakaoTalk for Malware Propagation
A notable aspect of this campaign is the strategic use of the KakaoTalk desktop application installed on the victim’s system. Konni exploits the trust inherent in personal communications by sending malicious ZIP files to selected contacts from the victim’s friend list. These files are often disguised with filenames suggesting content related to North Korea, enticing recipients to open them.
This method effectively transforms the initial victim into an unwitting distributor of the malware, facilitating a chain reaction of infections. By leveraging the credibility of known contacts, the likelihood of recipients opening the malicious files increases significantly.
Historical Context and Evolution of Tactics
Konni’s utilization of KakaoTalk as a distribution vector is not unprecedented. In November 2025, the group was observed exploiting active KakaoTalk sessions to disseminate malware to contacts via ZIP archives. Concurrently, they initiated remote wipes of Android devices using stolen Google credentials, showcasing a multifaceted approach to cyber attacks.
The current campaign reflects an evolution in Konni’s tactics, emphasizing long-term persistence, strategic information theft, and the exploitation of trusted communication channels for malware distribution.
Implications and Recommendations
The sophistication of Konni’s operations highlights the critical need for heightened cybersecurity awareness and proactive defense measures. Organizations and individuals are advised to:
– Exercise Caution with Unsolicited Communications: Be wary of unexpected emails, especially those containing attachments or links, even if they appear to originate from known contacts.
– Implement Robust Security Protocols: Utilize advanced email filtering, endpoint protection solutions, and regular system updates to mitigate potential threats.
– Educate Users: Conduct regular training sessions to inform users about the latest phishing tactics and the importance of verifying the authenticity of communications.
– Monitor Communication Channels: Regularly review and monitor messaging applications for any unauthorized activities or anomalies.
By adopting a comprehensive and proactive approach to cybersecurity, individuals and organizations can better defend against the evolving threats posed by groups like Konni.