Kali Linux has unveiled a groundbreaking integration that merges its robust penetration testing capabilities with the advanced artificial intelligence of Anthropic’s Claude AI. This fusion enables security professionals to issue natural language commands, which are then translated into actionable terminal commands within a Kali Linux environment. The integration is facilitated through the open-source Model Context Protocol (MCP), streamlining and enhancing the efficiency of penetration testing workflows.
Revolutionizing Penetration Testing with AI
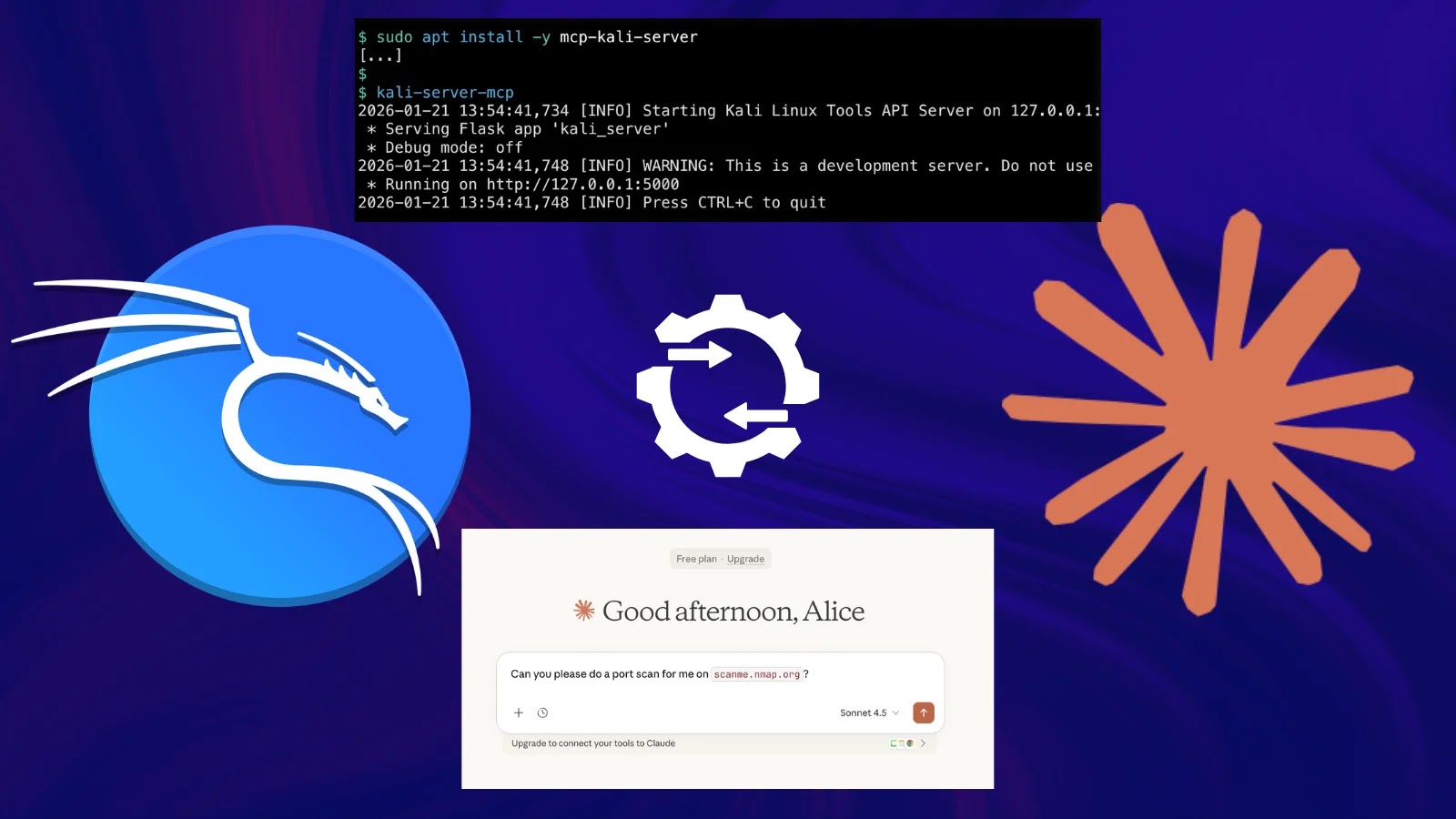
Traditionally, penetration testers have relied on manual execution of various tools like Nmap for network scanning or Gobuster for directory enumeration. This process often involves a steep learning curve and meticulous command-line operations. With the new AI-assisted workflow, testers can now input prompts such as, Port scan scanme.nmap.org and check if a security.txt file exists, and Claude AI autonomously interprets, plans, executes, and returns the results. This innovation significantly reduces the complexity and time required for comprehensive security assessments.
The Three-Tiered Architecture
The integration operates on a sophisticated three-component architecture:
1. User Interface Layer: Claude Desktop serves as the natural language interface, allowing users to input commands in plain English.
2. Execution Layer: A Kali Linux environment, either local or cloud-hosted, runs the `mcp-kali-server`. This lightweight API bridge exposes security tools to MCP clients, facilitating seamless command execution.
3. Intelligence Layer: Anthropic’s Claude Sonnet 4.5 model, hosted in the cloud, processes user prompts and orchestrates the necessary tool calls to perform the requested tasks.
Understanding the Model Context Protocol (MCP)
The Model Context Protocol, introduced by Anthropic in 2024, provides a standardized mechanism for integrating external systems into AI workflows. Instead of developing individual API integrations for each tool, MCP acts as a universal connector, maintaining context across multiple tool interactions within a single session.
In the context of Kali Linux, when a user submits a prompt, Claude AI determines the appropriate security tool required and sends a structured request to the `mcp-kali-server`. The server executes the command on the Kali host and returns structured output back to the AI, which then interprets the results and presents findings to the user. If necessary, Claude AI can automatically iterate with follow-up commands to fulfill the original request, creating a self-contained loop: prompt → plan → execute → interpret → re-execute if needed.
Setting Up the Integration
To implement this integration, secure SSH-based communication is established between the macOS client and the Kali server, utilizing key-based authentication for passwordless access. On the Kali side, the `mcp-kali-server` is installed via the package manager and runs a Flask-based API on `localhost:5000`, serving as the command execution bridge.
The Claude Desktop’s MCP client configuration is updated to point to the Kali instance over SSH, using `stdio` transport. This setup ensures that the AI can effectively communicate with the Kali environment to execute commands and retrieve results.
Supported Penetration Testing Tools
The integration supports a comprehensive suite of essential penetration testing tools, including:
– Nmap: For network and port scanning.
– Gobuster/Dirb: For directory and web path enumeration.
– Nikto: For web server vulnerability scanning.
– Hydra/John the Ripper: For credential brute-forcing.
– Metasploit Framework: For exploitation and post-exploitation activities.
– SQLMap/WPScan: For database injection and WordPress auditing.
– Enum4linux-ng: For SMB/Windows enumeration.
Practical Application and Testing
During testing documented by the Kali team, a prompt requesting a port scan of `scanme.nmap.org` led Claude AI to verify tool availability, execute the command `nmap -sV scanme.nmap.org`, parse open ports on `80/TCP` and `443/TCP`, and report the findings—all without manual command input.
Server logs confirmed real-time execution, including tool availability checks, the Nmap invocation, and structured HTTP responses from the Flask API.
Security Considerations
While this integration offers significant advancements in penetration testing efficiency, it also introduces new security considerations. Potential risks include prompt injection attacks, over-permissioned tool access, and insufficient audit logging. To mitigate these risks, it is recommended to enforce the principle of least privilege, implement robust input validation, and maintain comprehensive audit logs to monitor AI-driven activities.
Conclusion
The integration of Claude AI into Kali Linux via the Model Context Protocol marks a significant milestone in the evolution of penetration testing methodologies. By enabling natural language commands to drive complex security assessments, this innovation not only enhances efficiency but also makes penetration testing more accessible to a broader range of security professionals. As with any powerful tool, it is essential to implement appropriate security measures to ensure its safe and effective use.