Iranian Cyberattack Targets Over 300 Israeli Microsoft 365 Organizations
In a significant escalation of cyber warfare, an Iran-affiliated threat actor has launched a sophisticated password-spraying campaign targeting Microsoft 365 environments across Israel and the United Arab Emirates (U.A.E.). This campaign, which unfolded in three distinct waves on March 3, March 13, and March 23, 2026, has impacted more than 300 organizations in Israel and over 25 in the U.A.E., according to cybersecurity firm Check Point.
The primary targets of this campaign include government entities, municipalities, technology firms, transportation companies, energy sector organizations, and various private-sector businesses within the region. Notably, similar activities have been observed against a limited number of targets in Europe, the United States, the United Kingdom, and Saudi Arabia, indicating a broader scope of this cyber offensive.
Understanding Password Spraying Attacks
Password spraying is a type of brute-force attack where a malicious actor attempts to access multiple accounts by using a single common password across numerous usernames. This method is particularly effective in identifying weak credentials on a large scale without triggering account lockouts or rate-limiting defenses.
Iranian hacking groups, such as Peach Sandstorm and Gray Sandstorm (formerly known as DEV-0343), have previously employed password spraying techniques to infiltrate target networks. The current campaign mirrors these tactics, unfolding in three phases:
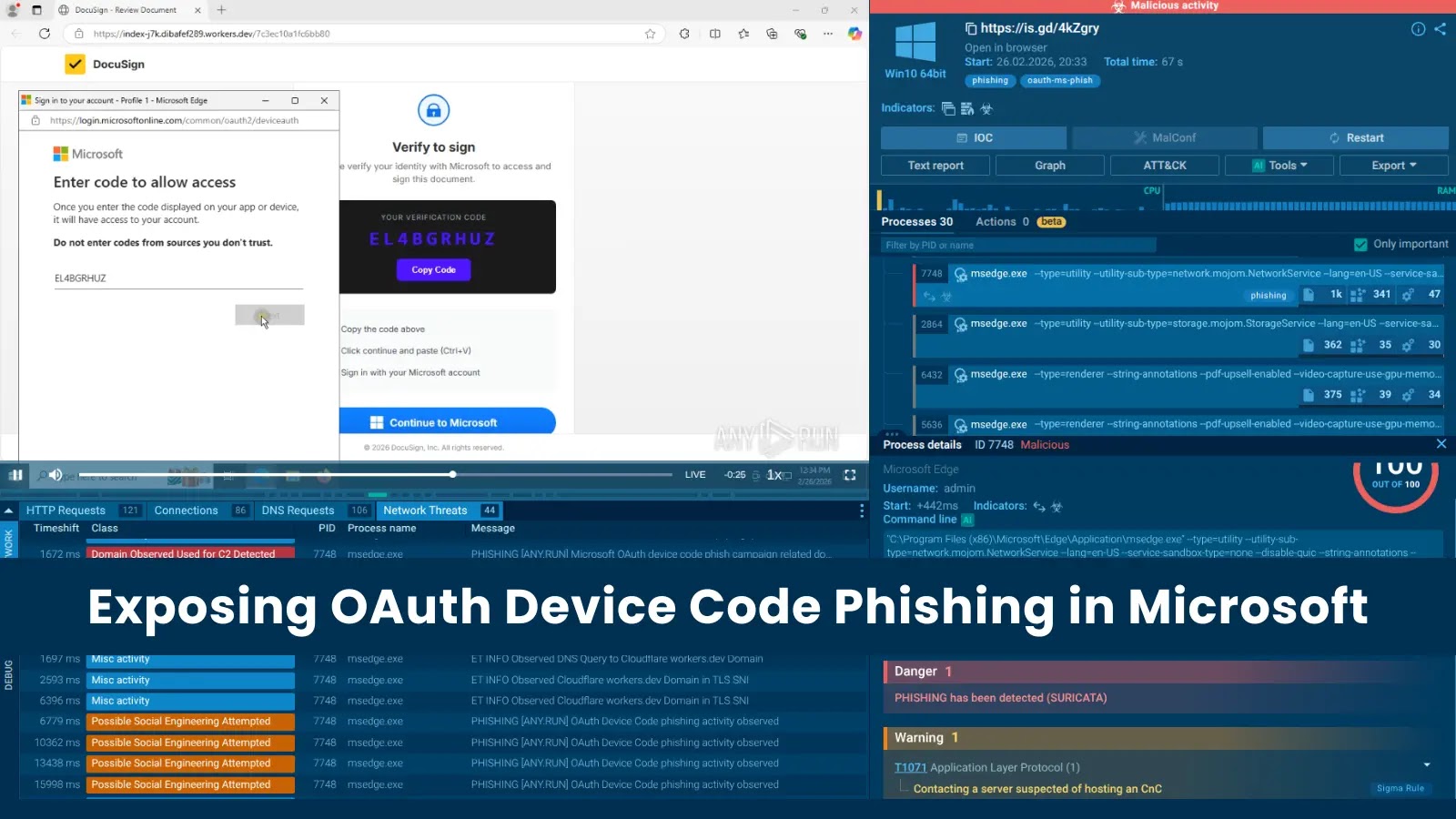
1. Initial Reconnaissance and Scanning: The attackers conduct aggressive scanning and password-spraying activities using Tor exit nodes to obscure their origins.
2. Credential Compromise and Access: Upon successful authentication, the threat actors proceed to log in to the compromised accounts.
3. Data Exfiltration: The final phase involves extracting sensitive information, such as mailbox contents, from the compromised accounts.
Analysis of Microsoft 365 logs suggests similarities to Gray Sandstorm’s previous activities, including the use of red-team tools to conduct these attacks via Tor exit nodes. Additionally, the threat actor utilized commercial VPN nodes hosted at AS35758 (Rachamim Aviel Twito), aligning with recent Iran-linked operations in the Middle East.
Mitigation Strategies
To defend against such threats, organizations are advised to implement the following measures:
– Monitor Sign-In Logs: Regularly review sign-in logs for indications of password spraying attempts.
– Apply Conditional Access Controls: Restrict authentication processes to approved geographic locations to minimize unauthorized access.
– Enforce Multi-Factor Authentication (MFA): Require MFA for all users to add an additional layer of security beyond just passwords.
– Enable Audit Logs: Activate audit logs to facilitate post-compromise investigations and understand the scope of any breaches.
Resurgence of Pay2Key Operations
In a related development, the Iranian ransomware group Pay2Key has resurfaced, targeting a U.S. healthcare organization in late February 2026. Pay2Key, which operates as a ransomware-as-a-service (RaaS) and is linked to the Fox Kitten group, first emerged in 2020.
The latest variant deployed in this attack showcases enhanced evasion, execution, and anti-forensics techniques compared to previous campaigns observed in July 2025. Notably, no data was exfiltrated during this attack, marking a departure from the group’s typical double extortion tactics.
The attack sequence involved:
1. Initial Access: The attackers gained entry through an undetermined access route, utilizing legitimate remote access tools like TeamViewer to establish a foothold.
2. Credential Harvesting and Lateral Movement: Once inside, they harvested credentials to move laterally within the network.
3. Disabling Security Measures: The attackers disarmed Microsoft Defender Antivirus by falsely signaling the presence of a third-party antivirus product.
4. Ransomware Deployment: They deployed the ransomware payload, dropped a ransom note, and cleared logs to cover their tracks.
By clearing logs at the end of execution rather than the beginning, the attackers ensured that even the ransomware’s own activity was wiped, not just preceding events.
Following its return last year, Pay2Key made significant changes to its operations, including offering affiliates an 80% cut of ransom proceeds, up from 70%, for participating in attacks targeting Iran’s adversaries. Additionally, a Linux variant of the Pay2Key ransomware was detected in the wild, indicating the group’s evolving capabilities.
Conclusion
The recent password-spraying campaign targeting Israeli and U.A.E. organizations, coupled with the resurgence of Pay2Key operations, underscores the persistent and evolving cyber threats emanating from Iranian-linked actors. Organizations must remain vigilant, implement robust security measures, and stay informed about emerging threats to safeguard their digital assets.