Iranian Botnet Unveiled: Open Directory Leak Exposes 15-Node Relay Network
In a significant cybersecurity revelation, a botnet linked to Iranian actors has been uncovered due to an inadvertent open directory on their staging server. This exposure has provided researchers with an unprecedented glimpse into the operational mechanics of a live botnet.
Discovery of the Open Directory
On February 24, 2026, during routine scans, a server with the IP address 185.221.239[.]162, hosted by Dade Samane Fanava Company (PJS), an Iranian Internet Service Provider, was identified. This server contained 449 files organized into 59 subdirectories, revealing a comprehensive suite of tools and configurations used in the botnet’s operations.
Contents of the Exposed Server
The open directory housed a variety of critical components:
– Tunnel Configuration Files: These files detailed the setup for encrypted communication channels, facilitating covert data transmission.
– Python-Based Deployment Scripts: Scripts designed to automate the distribution and activation of malicious payloads across compromised systems.
– Compiled DDoS Binaries and Source Files: Tools and source code intended for launching Distributed Denial-of-Service attacks, capable of overwhelming target systems.
– Credential Lists: Databases of stolen or default credentials used to gain unauthorized access to victim systems via SSH.
Infrastructure and Network Analysis
Further investigation by Hunt.io analysts, utilizing their AttackCapture™ feature, revealed that the server’s TLS certificate was associated with the wildcard domain .server21[.]org. This led to the identification of 14 additional IP addresses sharing the same certificate fingerprint. These addresses were distributed across hosting services, with seven located on Hetzner Online GmbH in Finland and seven registered to Iranian ISPs, including Dade Samane Fanava Company (PJS) and Sindad Network Technology PJSC. The domain, registered in 2023, utilized DNS services from ArvanCloud (arvancdn[.]ir), an Iranian content delivery network provider.
Dual-Purpose Infrastructure
The exposed infrastructure served multiple functions:
– VPN Relay Service: A configuration file named config-client.yaml described a KCP-based packet tunnel using Paqet, an open-source tool designed to circumvent Iran’s national internet filtering system. This setup allowed the Iranian server to forward encrypted traffic to an exit node in Finland.
– Proxy Management: The presence of 3x-ui, a web-based proxy panel, indicated the operation of a commercial VPN relay service alongside the botnet activities.
Operational Insights from Bash History
An exposed bash history file provided a chronological view of the operator’s activities, segmented into three phases:
1. Tunnel Deployment: Establishing encrypted communication channels to facilitate covert operations.
2. DDoS Tool Development: Creating and testing tools for launching Distributed Denial-of-Service attacks.
3. Botnet Expansion: Deploying malware to expand the botnet’s reach and control over compromised systems.
Inline code comments written in Farsi and Arabic-script characters resulting from keyboard input errors suggest that the operators are likely based in Iran.
DDoS Targeting and Tool Development
The bash history revealed specific targets for DDoS attacks, including a FiveM GTA server at 5.42.223[.]60 on port 30120 and two HTTP/HTTPS-facing hosts. The operators utilized custom C tools—syn.c, flood.c, and au.c—alongside MHDDOS, a tool cloned from GitHub and compiled directly on the staging host.
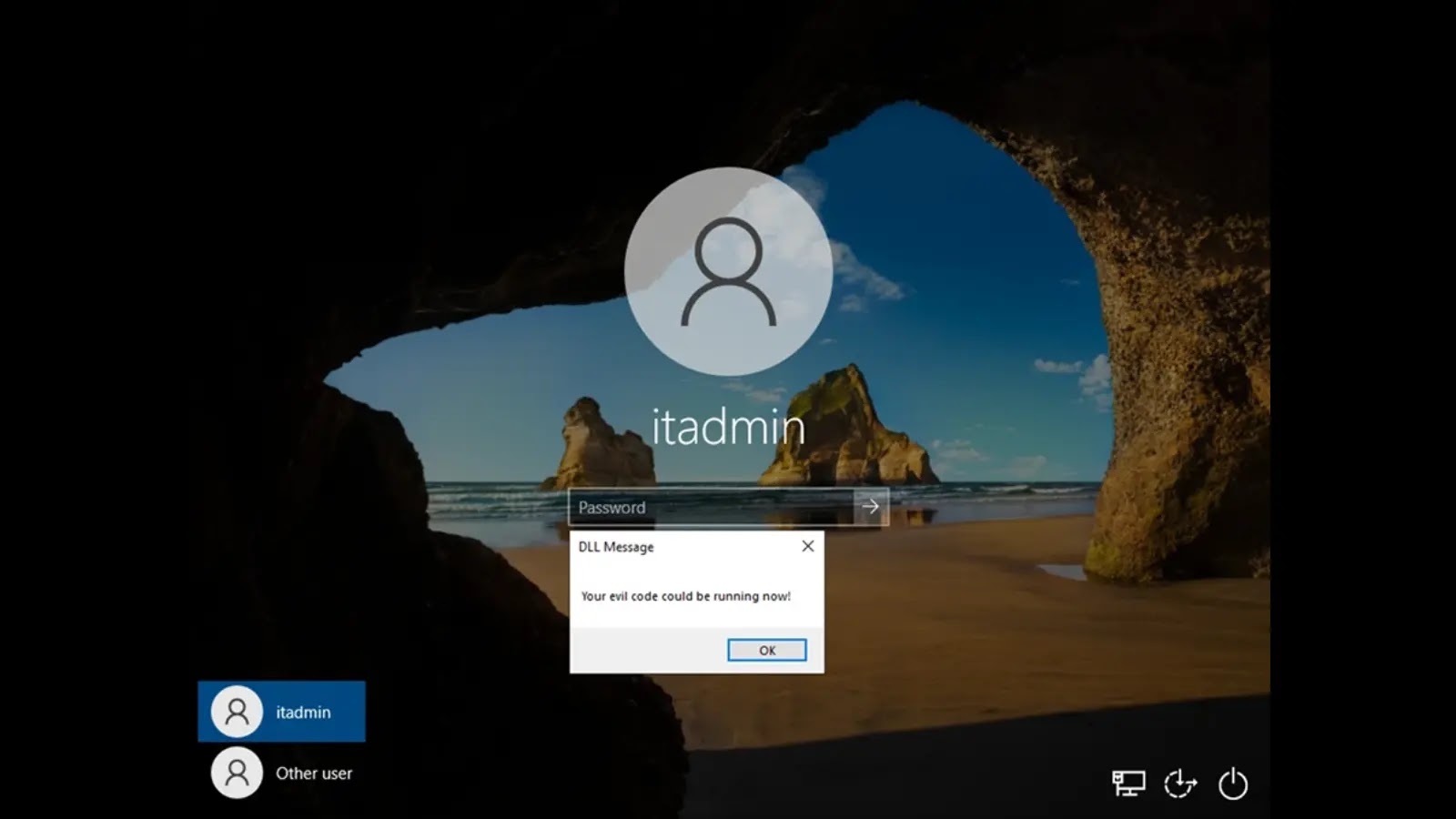
SSH-Based Mass Deployment Mechanism
A critical component of the botnet’s propagation was a Python script named ohhhh.py. This script read credentials formatted as host:port|username|password and initiated 500 concurrent SSH sessions against target machines. Upon establishing a session, the bot client source file cnc.c was transferred from the staging server, compiled on the victim machine using gcc -pthread, and executed in a detached screen session. This method of on-host compilation was likely employed to evade detection, as no pre-compiled binaries were transferred, rendering hash-based scanning ineffective.
Implications and Recommendations
The inadvertent exposure of this botnet’s infrastructure underscores the critical importance of securing operational assets. For organizations, this incident highlights the necessity of:
– Regular Security Audits: Conducting thorough reviews of servers and directories to prevent unauthorized access.
– Credential Management: Implementing robust password policies and regularly updating credentials to mitigate unauthorized SSH access.
– Network Monitoring: Utilizing advanced monitoring tools to detect unusual activities indicative of botnet operations.
By adopting these measures, organizations can enhance their defenses against sophisticated cyber threats and prevent inadvertent exposures that could be exploited by malicious actors.