Iranian APT ‘Dust Specter’ Targets Iraqi Officials with AI-Enhanced Malware
In January 2026, a sophisticated cyberattack campaign emerged, targeting Iraqi government officials. The threat actor, identified as ‘Dust Specter,’ employed deceptive tactics by impersonating Iraq’s Ministry of Foreign Affairs to distribute malicious files to high-value targets. This operation introduced four previously undocumented malware tools: SPLITDROP, TWINTASK, TWINTALK, and GHOSTFORM, each demonstrating the precision and capabilities of a state-sponsored entity.
Researchers have attributed this campaign with medium-to-high confidence to an Iran-linked threat actor, citing consistent overlaps in tools, techniques, and victim selection with known Iranian Advanced Persistent Threat (APT) groups.
Attack Chain 1: SPLITDROP and DLL Sideloading
The initial attack vector involved a password-protected RAR archive named ‘mofa-Network-code.rar,’ masquerading as an official document from the Ministry. Upon extraction, the archive contained a .NET binary disguised as a WinRAR application—SPLITDROP. This binary decrypted an embedded payload using AES-256 encryption and deployed malicious files onto the victim’s system. To maintain the illusion of legitimacy, SPLITDROP displayed a false error message stating, The download did not complete successfully, while operating covertly.
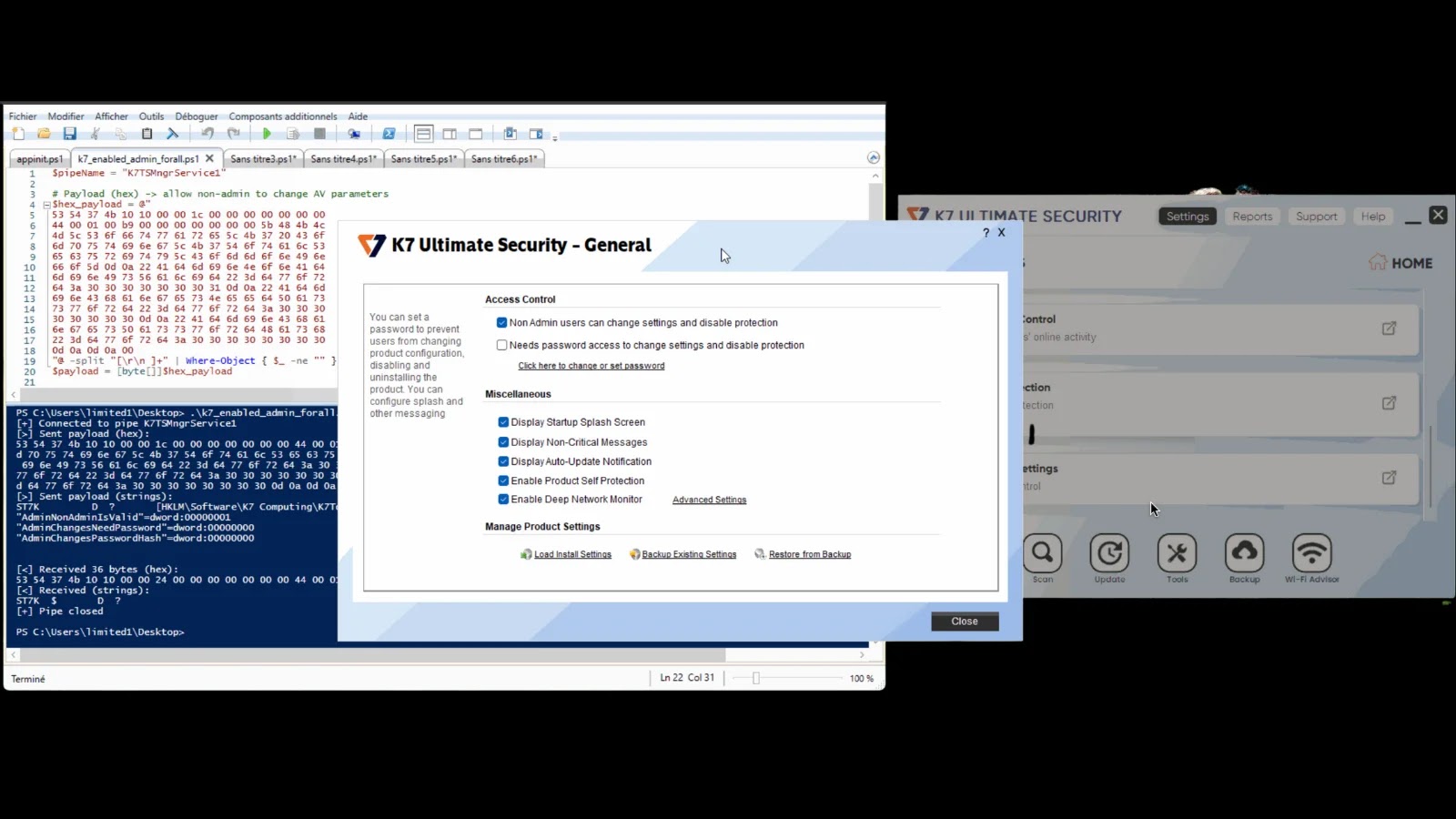
Following the payload deployment, SPLITDROP executed a legitimate VLC Media Player binary, which in turn sideloaded a malicious DLL named ‘libvlc.dll’ located in the same directory. This DLL sideloading technique exploits the trust Windows places in recognized applications, allowing the malware to run without elevated privileges.
The malicious DLL, identified as TWINTASK, functioned as a worker module that polled a local text file every 15 seconds, reading and executing Base64-encoded PowerShell commands received from the Command and Control (C2) orchestrator. TWINTASK then launched ‘WingetUI.exe,’ which sideloaded another malicious DLL named ‘hostfxr.dll,’ referred to as TWINTALK. TWINTALK acted as the C2 orchestrator, communicating with remote servers at randomized intervals between 108 and 180 seconds to evade detection.
To ensure persistence, the malware established Windows Registry Run keys, causing both ‘VLC.exe’ and ‘WingetUI.exe’ to relaunch automatically upon system restart, thereby maintaining the infection across reboots.
Attack Chain 2: GHOSTFORM and AI-Generated Code
In the second attack chain, Dust Specter utilized GHOSTFORM, which presented a fake Arabic Google Form survey posing as a government questionnaire. While the victim interacted with the decoy form, the malware operated undetected in the background.
Notably, researchers identified fingerprints in the codebase indicating the use of generative AI during malware development. Emojis and Unicode characters embedded within both TWINTALK and GHOSTFORM source code matched patterns associated with AI-generated programming. Additionally, a hardcoded seed value of ‘0xABCDEF’—a placeholder commonly found in AI-written code—was discovered within TWINTALK’s checksum generation function. This signifies a shift in threat actor methodologies, with AI being utilized not only for planning but also for writing functional malicious code.
Historical Context and Attribution
Dust Specter’s activities align with previous campaigns attributed to Iranian-linked groups. For instance, in July 2025, a similar attack involved a webpage mimicking a Cisco Webex Government meeting invitation, directing victims to execute a PowerShell command that downloaded a malicious binary and registered a scheduled task to execute every two hours. Iraq’s Ministry of Foreign Affairs has historically been a priority target for Iran-linked groups like APT34, and this campaign follows that established pattern closely.
Technical Analysis: Infection Mechanisms and Evasion Techniques
The infection mechanisms employed by Dust Specter were meticulously designed to blend into legitimate system activity without raising alarms. After SPLITDROP extracted its payload into a local directory, it launched a genuine VLC Media Player binary, which automatically sideloaded a malicious DLL named ‘libvlc.dll’ placed in the same folder. This DLL sideloading technique exploits the trust that Windows places in recognized applications and does not require elevated privileges to run.
The malicious DLL, named TWINTASK, functioned as a worker module that polled a local text file every 15 seconds, reading and executing Base64-encoded PowerShell commands received from the C2 orchestrator. TWINTASK then launched ‘WingetUI.exe,’ which sideloaded a second malicious DLL named ‘hostfxr.dll’—the component called TWINTALK. This acted as the C2 orchestrator, beaconing to remote servers at randomized intervals between 108 and 180 seconds to avoid pattern-based network detection rules.
To verify that requests came from genuinely infected machines rather than automated scanners, TWINTALK generated dynamic URI paths with appended checksum values. The C2 server added verification through a hardcoded browser User-Agent string and applied geofencing to restrict responses to traffic from specific geographic regions only.
Persistence was established through Windows Registry Run keys, ensuring both ‘VLC.exe’ and ‘WingetUI.exe’ relaunched automatically after every system restart, keeping the infection alive across reboots.
GHOSTFORM took a more creative approach—it launched an invisible Windows form with near-zero opacity, hidden from the taskbar—to delay its own execution without calling any Windows API that could trigger behavioral analysis tools.
Recommendations for Defense
To mitigate the risks associated with such sophisticated attacks, security teams should enforce strict application allowlisting to prevent unauthorized DLL sideloading through trusted binaries. Email and web gateways should be configured to block password-protected archives from unverified senders. Enabling PowerShell script block logging and monitoring Windows Registry Run keys for unexpected new entries are critical defensive steps against this type of intrusion. Network teams should flag outbound HTTPS traffic with randomized URI patterns and non-standard JWT authorization headers, as these behavioral indicators align with the C2 communication profile observed in this campaign.