Inside Apple’s Fortress: Securing Pre-Release iOS at Assembly Plants
Apple’s reputation for innovation is matched by its commitment to secrecy, especially concerning pre-release versions of iOS. While software leaks are not uncommon, the assembly plants responsible for iPhone production are notably tight-lipped. This article delves into the stringent security protocols Apple enforces to protect its unreleased software during the manufacturing process.
The Challenge of Maintaining Secrecy
Each year, as Apple prepares to unveil new iterations of iOS, rumors and leaks surface, revealing potential features and design changes. These leaks often originate from various sources, including prototype devices and insider disclosures. However, assembly plants, despite their access to pre-release software, rarely contribute to these information breaches. This rarity is a testament to Apple’s rigorous security measures.
Fortifying the Assembly Line
Apple imposes a comprehensive set of security requirements on its assembly partners, covering every aspect of the production process. This includes the handling of unreleased hardware, confidential projects, and even packaging materials. Specific protocols are in place to safeguard pre-release operating systems:
– Restricted Access Areas: Devices running unreleased iOS versions are confined to specialized rooms with a single entry point, monitored by badge scanners and security personnel. This setup ensures that only authorized individuals can access these areas.
– Visual Barriers: Curtains or other obstructions prevent unauthorized personnel from glimpsing the pre-release user interface, maintaining the confidentiality of the software’s appearance and functionality.
– Controlled Entry: Access to these secure rooms is limited to select Apple employees and vetted third-party staff. Additional Apple personnel may enter only with proper authorization and after signing in.
– Stringent Policies for Third-Party Staff: Non-Apple employees must sign non-disclosure agreements and are prohibited from bringing personal devices, cameras, or recording equipment into the secure areas. They are also subject to physical scans upon entry and exit to prevent unauthorized items from being smuggled in or out.
– Surveillance Measures: High-resolution CCTV cameras monitor all activities within the secure rooms, covering workstations, storage areas, and equipment. The recorded footage is stored in a separate, restricted-access room to ensure its integrity.
Inside the Secure Rooms
Within these fortified areas, the security measures continue:
– Isolated Workstations: The primary computers used are Mac minis with disabled email and Wi-Fi capabilities. USB ports are locked to prevent unauthorized data transfers. The network within the secure area is physically separated from other parts of the facility to prevent external access.
– Controlled Device Handling: Only designated employees are authorized to transport devices with unreleased iOS versions in and out of the secure rooms. Each movement is meticulously logged, noting the date, time, and quantity of devices.
– Monitored Connectivity: Devices running pre-release software have their Wi-Fi activity continuously monitored. For testing purposes, they can only access a whitelist of websites, such as Apple’s official site and select services like Google Maps. Bluetooth and Wi-Fi are generally kept disabled, and camera lenses are sealed or removed to prevent unauthorized image capture. SIM card slots are covered with tamper-evident seals.
– Purpose-Specific Usage: Each test device is labeled with its intended purpose. When not in use, these devices are stored in locked containers with tamper-evident stickers. A comprehensive list of all equipment, including serial numbers, is maintained and displayed within the secure area.
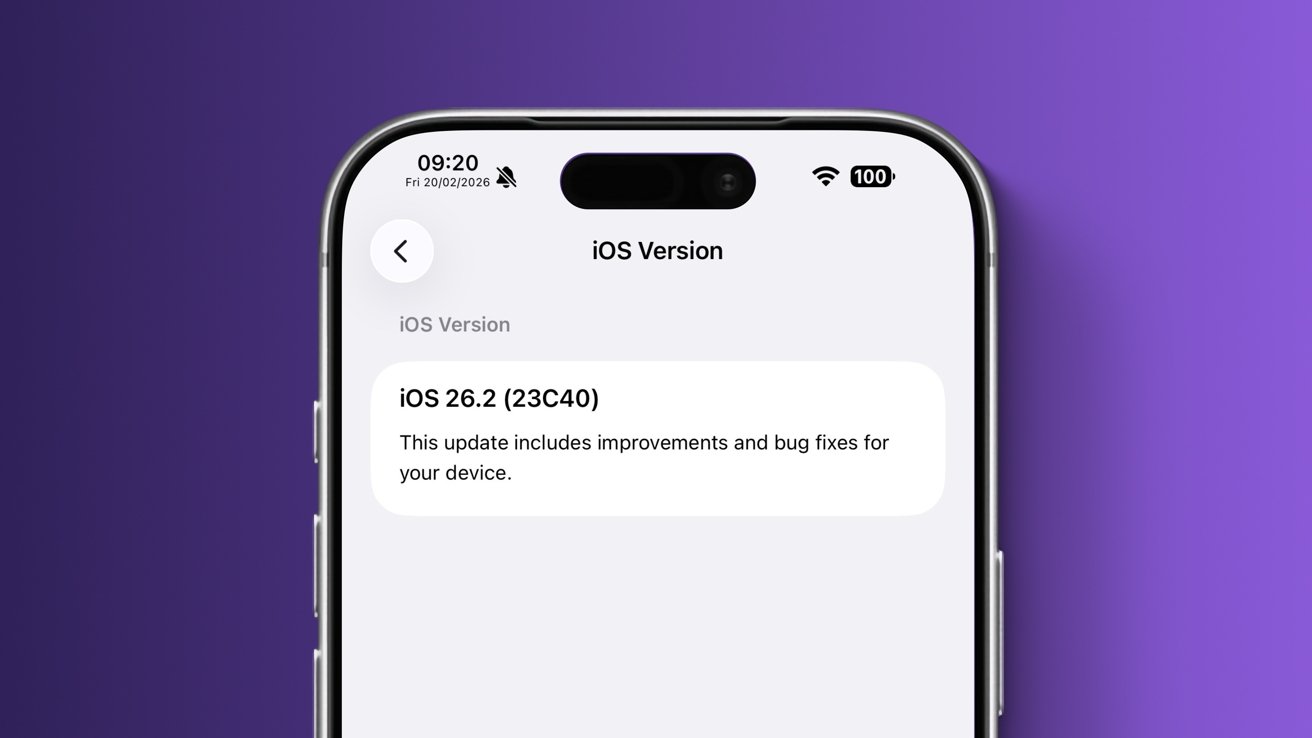
Utilizing Pre-Release iOS Builds
Apple’s assembly partners employ various iOS versions, internally referred to as ReleaseTypes, for different testing and quality control purposes:
– VendorUI ReleaseType: Access to this variant is highly restricted, granted only to select authorized employees. Unlike NonUI and LLDiags versions used for hardware diagnostics, VendorUI includes most system applications necessary for comprehensive testing.
– Application Availability: While essential apps like Phone, Camera, and Safari are typically present, certain applications containing sensitive UI elements or those not required for testing are removed. This selective inclusion ensures that only necessary features are accessible during the testing phase.
– Internal Testing Tools: Specialized internal applications, such as the Radar bug-reporting utility and other diagnostic tools, may be installed depending on the specific tests being conducted.
Quality Control and Testing Procedures
The specialized iOS builds are integral to the quality control process:
– Hardware Functionality Tests: Employees test all physical components, including buttons, speakers, ports, and biometric features like Face ID or Touch ID. For instance, Face ID functionality is verified using the Animoji feature in Messages.
– Sensor Calibration: Motion sensors are assessed using apps like Compass and Measure. The ambient light sensor is tested by enabling Auto Brightness and observing changes in screen brightness when the sensor is covered.
– Application Performance: The Photos app is used to view, edit, and markup images, ensuring the software’s responsiveness and stability. Video playback is similarly tested to confirm smooth performance.
– Camera Testing: Each camera sensor undergoes thorough testing, including capturing photos with and without flash, time-lapse photography, portrait mode shots, panoramas, and videos in both regular and slow-motion modes.
Any anomalies or malfunctions, such as non-functional camera modes or unresponsive applications, are meticulously logged and reported for further investigation.
Effectiveness of Apple’s Security Measures
Despite the occasional appearance of devices running specialized iOS versions in the hands of collectors, this typically occurs long after the testing phase and the public release of the corresponding retail units. Apple’s stringent security protocols and leak prevention strategies have proven effective in safeguarding pre-release software during active development, ensuring that assembly plants remain a fortress of confidentiality.