Elevating Tier 1 SOC Performance: Three Essential Steps for CISOs
In the realm of cybersecurity, the Security Operations Center (SOC) serves as the frontline defense against digital threats. At the heart of this defense lies the Tier 1 analyst team, responsible for the initial detection and triage of potential security incidents. Despite their critical role, these entry-level analysts often grapple with challenges that can compromise the effectiveness of the entire SOC.
The Tier 1 Conundrum: High Responsibility, Limited Resources
Tier 1 analysts are tasked with processing a vast volume of alerts, performing initial assessments, and determining which incidents require escalation. However, several factors hinder their performance:
– Alert Fatigue: The relentless influx of alerts can desensitize analysts, leading to overlooked genuine threats.
– Decision Fatigue: Continuous decision-making without adequate support can degrade judgment quality over time.
– Cognitive Overload: Managing multiple dashboards and tools without sufficient context can overwhelm analysts.
– High Turnover Rates: The demanding nature of the role often results in burnout and attrition, leading to a loss of institutional knowledge.
These challenges not only affect individual analysts but also have broader implications for the organization:
– Increased Dwell Time: Delays in identifying and responding to threats allow adversaries more time within the network.
– Escalated Incident Costs: Prolonged detection and response times can lead to more severe breaches, incurring higher remediation costs.
– Erosion of Executive Confidence: Persistent security lapses can diminish trust in the organization’s cybersecurity posture.
Monitoring and Triage: The Pillars of SOC Operations
The effectiveness of a SOC hinges on two primary processes:
1. Monitoring: Continuous surveillance of the organization’s digital environment to detect anomalies.
2. Triage: Evaluating detected anomalies to determine their severity and the appropriate response.
Inefficiencies in these processes can lead to:
– Overburdened Senior Analysts: Tier 2 and Tier 3 analysts may become inundated with false positives, diverting attention from genuine threats.
– Delayed Incident Response: Late identification of threats can result in extended periods of vulnerability.
– Operational Disruptions: Security incidents can impede business operations, affecting productivity and revenue.
– Regulatory Non-Compliance: Failure to promptly address security incidents can lead to violations of industry regulations.
Empowering Tier 1 with Actionable Threat Intelligence
To enhance the efficacy of Tier 1 analysts, integrating actionable threat intelligence is paramount. This integration provides:
– Indicator of Compromise (IOC) Validation: Confirming whether specific artifacts are associated with known threats.
– Campaign Context: Understanding the broader attack campaigns targeting the organization or industry.
– Tactics, Techniques, and Procedures (TTP) Mapping: Identifying the methods employed by adversaries.
– Infrastructure Associations: Recognizing connections between malicious domains, IP addresses, and other infrastructure components.
– Malware Family Attribution: Determining the specific malware variants involved in an incident.
By equipping Tier 1 analysts with this intelligence, organizations can:
– Reduce Dwell Time: Accelerate the identification and mitigation of threats.
– Enhance Detection Precision: Minimize false positives, allowing analysts to focus on genuine threats.
– Optimize Resource Allocation: Ensure that alerts are appropriately escalated, preventing unnecessary workload on senior analysts.
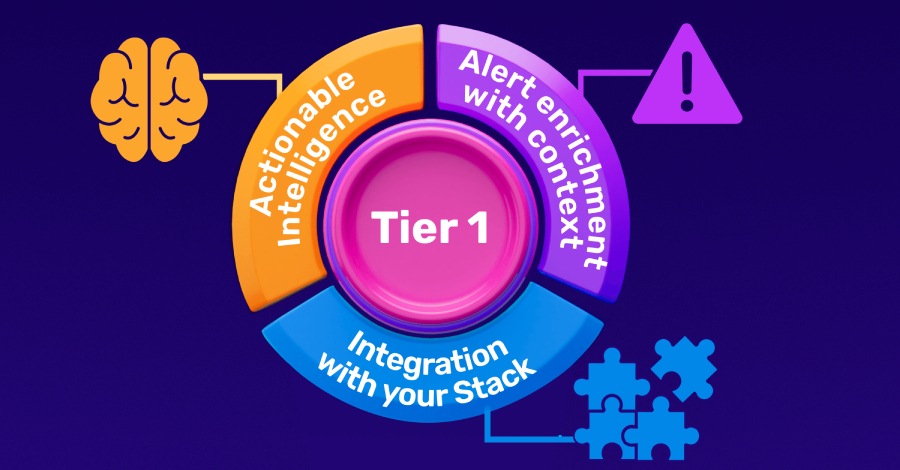
Three Steps to Building a High-Impact Tier 1 SOC
To transform Tier 1 operations, Chief Information Security Officers (CISOs) can implement the following steps:
Step 1: Integrate Live Threat Intelligence Feeds into Monitoring
Enhancing monitoring capabilities with real-time threat intelligence feeds enables the detection of sophisticated threats that evade traditional signature-based methods. These feeds, delivered in standardized formats like STIX and MISP, can be integrated with existing security tools such as Security Information and Event Management (SIEM) systems, firewalls, and endpoint detection solutions. Each indicator is accompanied by contextual metadata, providing analysts with comprehensive information to assess and respond to threats effectively.
Step 2: Enrich Alerts with Contextual Information
When an alert is generated, providing analysts with immediate context is crucial. Utilizing interactive sandbox environments allows analysts to observe the behavior of suspicious files or links in real-time. This approach offers:
– Behavioral Analysis: Understanding how a file or link behaves upon execution.
– Malware Attribution: Identifying the malware family associated with the artifact.
– Infrastructure Insights: Recognizing connections to malicious domains or IP addresses.
By integrating sandbox analysis into the triage process, analysts can make informed decisions swiftly, reducing reliance on manual research and minimizing the risk of misclassification.
Step 3: Seamlessly Integrate Tools and Processes
To maximize efficiency, it’s essential to integrate threat intelligence feeds, sandbox environments, and lookup tools into the existing security infrastructure. This integration ensures:
– Automated Enrichment: Alerts are automatically supplemented with relevant context, reducing manual effort.
– Consistent Intelligence Sharing: All security tools operate based on the same intelligence, enhancing coherence across the security stack.
– Streamlined Workflows: Analysts can access necessary information within their primary interfaces, minimizing context switching.
By adopting standardized formats and APIs, organizations can facilitate seamless integration, enabling a more responsive and resilient SOC.
Conclusion
Elevating the performance of Tier 1 analysts is not merely an operational enhancement; it’s a strategic imperative. By integrating actionable threat intelligence, enriching alerts with contextual information, and ensuring seamless tool integration, organizations can transform their SOC into a proactive defense mechanism. This approach not only mitigates risks but also fosters a more engaged and effective analyst team, ultimately strengthening the organization’s overall security posture.