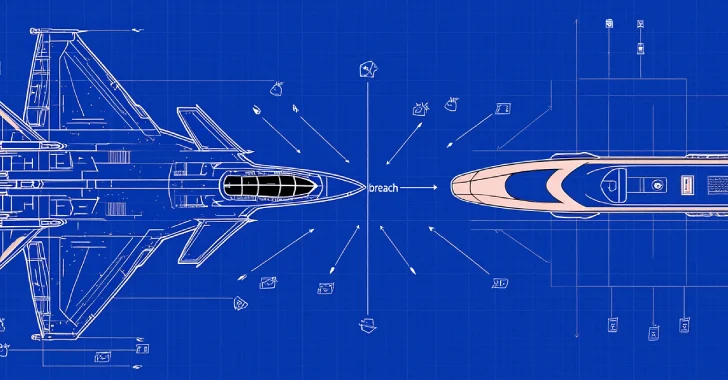
Hackers Rapidly Exploit Critical Oracle WebLogic RCE Vulnerabilities
In the ever-evolving landscape of cybersecurity, threat actors are demonstrating unprecedented speed in exploiting newly disclosed vulnerabilities. A recent study has highlighted this alarming trend, focusing on a critical flaw in Oracle WebLogic Server, designated as CVE-2026-21962. This vulnerability, assigned a maximum severity score of 10.0 on the Common Vulnerability Scoring System (CVSS), enables unauthenticated attackers to execute arbitrary remote code via the WebLogic Console.
Immediate Exploitation Observed
Security researchers observed that exploitation attempts for CVE-2026-21962 commenced on January 22, 2026—the same day the exploit code was publicly released. This rapid weaponization underscores the critical risk posed to organizations operating unpatched WebLogic Server instances.
Honeypot Deployment and Findings
To gain deeper insights into the threat landscape, researchers deployed a high-interaction honeypot emulating a vulnerable Oracle WebLogic Server (version 14.1.1.0.0) over a 12-day period. The honeypot recorded a significant surge in malicious activity, with attackers primarily utilizing rented Virtual Private Servers (VPS) from well-known hosting providers to conduct extensive, automated scans. This approach allowed threat actors to obscure their true origins while executing widespread attacks.
Automated Scanning and Exploitation Techniques
The study revealed that attackers employed automated tools such as libredtail-http and the Nmap Scripting Engine to flood the honeypot with malicious requests. While the primary focus was on exploiting CVE-2026-21962 through specific ProxyServlet HTTP GET requests, attackers also targeted several older, unpatched vulnerabilities, including:
– CVE-2020-14882 and CVE-2020-14883: Critical remote code execution flaws targeting the administrative console by bypassing authentication.
– CVE-2020-2551: A severe deserialization vulnerability in the IIOP protocol allowing remote code execution.
– CVE-2017-10271: An XML deserialization flaw in the WLS-WSAT component, often exploited via crafted SOAP requests.
This pattern indicates that cybercriminals continue to exploit both new and longstanding vulnerabilities to maximize their attack surface.
Broader Implications and Unrelated Vulnerability Scanning
Interestingly, the automated scanners also identified unrelated vulnerabilities, such as those in Hikvision cameras and PHPUnit, demonstrating that attackers are casting a wide net to identify any exploitable weaknesses.
Mitigation Strategies
Given the rapid exploitation of CVE-2026-21962, it is imperative for organizations to implement the following mitigation measures:
1. Apply Patches Immediately: Administrators should install the latest Oracle Critical Patch Updates (CPUs) across all components, prioritizing fixes for CVE-2026-21962.
2. Restrict Console Access: The WebLogic administrative console should not be exposed directly to the public internet. Secure it behind a strict VPN or internal firewall.
3. Deploy a Web Application Firewall (WAF): Configure WAF rules to detect and block malicious path traversal requests, deep packet inspection evasion attempts, and known exploit signatures.
4. Monitor System Logs: Closely monitor for unusual administrative access attempts or the sudden execution of suspicious operating system commands such as wget or curl.
Failure to promptly address these vulnerabilities leaves systems susceptible to complete compromise, emphasizing the necessity for proactive security measures.