GhostClaw Exploits GitHub Workflows to Infiltrate macOS Systems
In a concerning development for macOS users, a new malware strain named GhostClaw has been identified, leveraging common GitHub practices to distribute its payload. This sophisticated infostealer capitalizes on developers’ routine habits, embedding itself seamlessly into the software development lifecycle.
Understanding GhostClaw’s Tactics
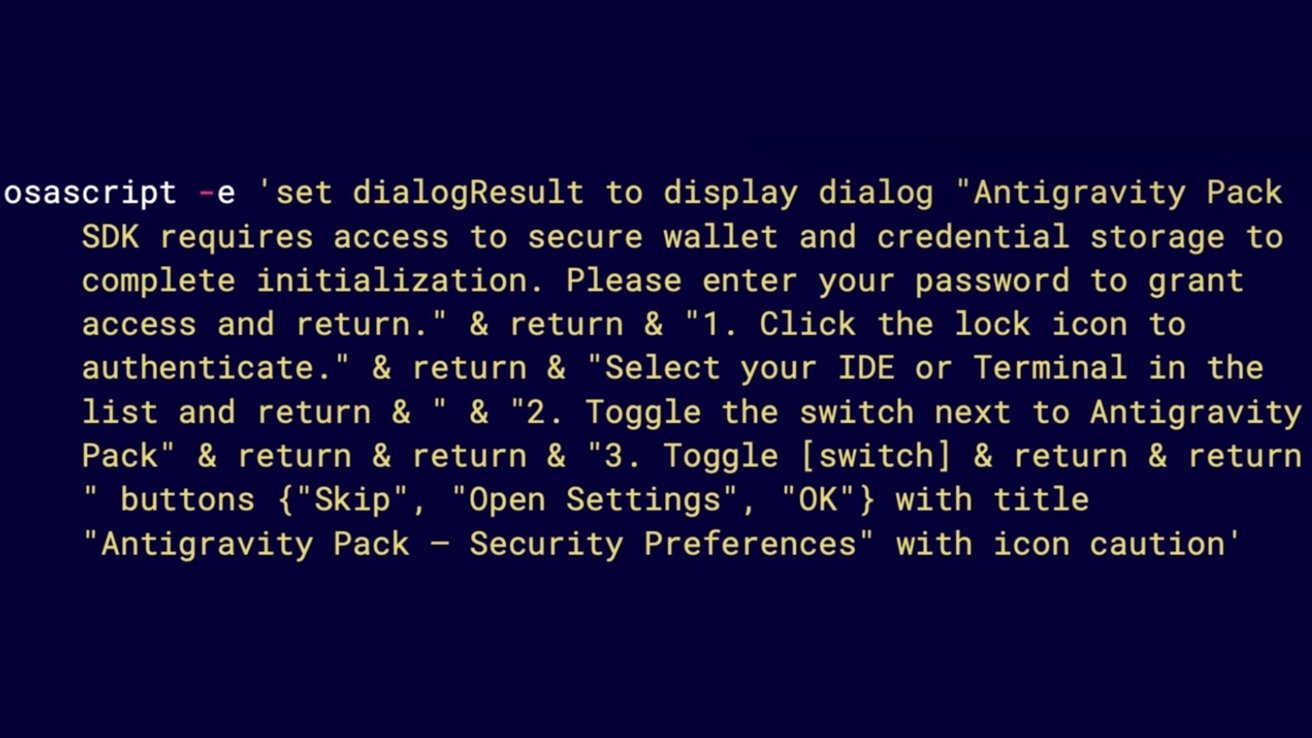
GhostClaw’s propagation method is particularly insidious due to its exploitation of GitHub repositories and developer tools. By infiltrating these platforms, the malware integrates into the development process, making its execution appear routine and thereby increasing the likelihood of successful infection.
The Evolution of the Threat
Security researchers at Jamf have been monitoring GhostClaw’s progression, noting its transition from targeting npm packages to embedding itself within GitHub repositories and AI-assisted development environments. This evolution underscores the malware’s adaptability and the growing sophistication of cyber threats facing macOS users.
Implications for Developers and Users
The integration of GhostClaw into trusted development tools poses a significant risk, as it can compromise the integrity of software projects and the security of end-users. Developers must exercise heightened vigilance, scrutinizing the sources of their tools and dependencies to prevent inadvertent inclusion of malicious code.
Protective Measures Against GhostClaw
To mitigate the risk posed by GhostClaw, consider the following strategies:
– Verify Sources: Ensure that all tools and dependencies are sourced from reputable and verified channels.
– Regular Audits: Conduct periodic reviews of your development environment to detect any unauthorized changes or additions.
– Stay Informed: Keep abreast of the latest security advisories and updates related to your development tools and platforms.
– Implement Security Protocols: Utilize robust security measures, such as code signing and integrity checks, to safeguard your development process.
Conclusion
The emergence of GhostClaw highlights the evolving landscape of cyber threats targeting macOS systems. By understanding its methods and implementing proactive security practices, developers and users can fortify their defenses against such insidious malware.