Critical EngageLab SDK Vulnerability Exposes 50 Million Android Users, Including 30 Million Cryptocurrency Wallets
A significant security vulnerability has been identified in the EngageLab SDK, a widely utilized third-party Android software development kit (SDK), potentially compromising the data of millions of users, particularly those using cryptocurrency wallets.
The Microsoft Defender Security Research Team disclosed that this flaw enables applications on the same device to circumvent Android’s security sandbox, thereby gaining unauthorized access to private data.
EngageLab SDK provides a push notification service designed to deliver timely notifications based on user behavior tracked by developers. Once integrated into an application, the SDK facilitates personalized notifications and enhances real-time user engagement.
A substantial number of applications incorporating the EngageLab SDK are part of the cryptocurrency and digital wallet ecosystem. The affected wallet applications account for over 30 million installations. When including non-wallet applications built on the same SDK, the total installation count exceeds 50 million.
While Microsoft did not disclose the specific names of the affected applications, it confirmed that all detected apps using vulnerable versions of the SDK have been removed from the Google Play Store. Following responsible disclosure in April 2025, EngageLab released version 5.2.1 in November 2025 to address the vulnerability.
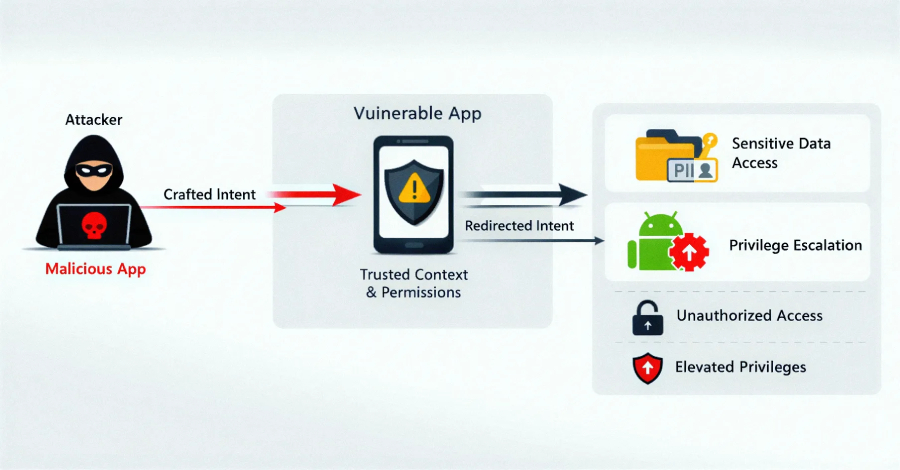
The vulnerability, identified in version 4.5.4, is classified as an intent redirection flaw. In the Android operating system, intents are messaging objects used to request actions from other app components. Intent redirection occurs when the contents of an intent sent by a vulnerable application are manipulated, exploiting its trusted context (i.e., permissions) to gain unauthorized access to protected components, expose sensitive data, or escalate privileges within the Android environment.
An attacker could exploit this vulnerability by installing a malicious application on the device through various means. This malicious app could then access internal directories associated with an application that has the EngageLab SDK integrated, resulting in unauthorized access to sensitive data.
There is currently no evidence to suggest that this vulnerability has been exploited maliciously. However, developers who have integrated the EngageLab SDK are strongly advised to update to the latest version promptly. Even minor flaws in upstream libraries can have cascading effects, potentially impacting millions of devices.
This case underscores how weaknesses in third-party SDKs can have large-scale security implications, especially in high-value sectors like digital asset management. Applications increasingly rely on third-party SDKs, creating extensive and often opaque supply-chain dependencies. These risks are heightened when integrations expose exported components or rely on trust assumptions that are not validated across application boundaries.