Enhancing SOC Efficiency: Reducing Escalation Rates Through Improved Tier-1 Alert Triage
In the dynamic realm of cybersecurity, Security Operations Centers (SOCs) serve as the frontline defense against a myriad of threats. A pivotal aspect of their effectiveness lies in the adept handling of alerts, particularly at the Tier-1 level. When Tier-1 analysts escalate alerts excessively, it not only burdens higher-tier teams but also hampers the overall efficiency of the SOC. This article delves into strategies to empower Tier-1 analysts, thereby reducing unnecessary escalations and enhancing the SOC’s operational efficacy.
The Escalation Dilemma
Escalation within a SOC should be a deliberate process, reserved for alerts that genuinely necessitate advanced expertise. However, many SOCs experience a scenario where escalation becomes a default response to uncertainty. This reflexive behavior leads to several challenges:
– Overburdened Tier-2 Analysts: An influx of escalated alerts inundates Tier-2 teams, diverting their focus from in-depth investigations to re-evaluating alerts that could have been resolved at Tier-1.
– Tier-1 Analyst Burnout: Facing high alert volumes and lacking confidence, Tier-1 analysts may resort to escalating alerts as a safety net, leading to job dissatisfaction and increased turnover.
– Operational Inefficiencies: Elevated escalation rates can inflate Mean Time to Detect (MTTD) and Mean Time to Respond (MTTR), potentially breaching Service Level Agreements (SLAs) and eroding client trust, especially for Managed Security Service Providers (MSSPs).
Understanding the Root Causes
Several factors contribute to high escalation rates:
– Alert Volume Growth: As detection mechanisms become more sophisticated, the volume of alerts increases. Without corresponding improvements in filtering and prioritization, this can overwhelm analysts.
– Detection Rule Decay: Over time, detection rules may become outdated, leading to an increase in false positives that require manual review.
– Analyst Turnover: Newly onboarded Tier-1 analysts, lacking experience and confidence, may escalate alerts more frequently as a precautionary measure.
– Insufficient Feedback Loops: Without effective communication between Tier-1 and Tier-2 teams, recurring patterns of unnecessary escalations persist, as Tier-1 analysts remain unaware of the outcomes of their escalated alerts.
Empowering Tier-1 Analysts with Enhanced Threat Intelligence
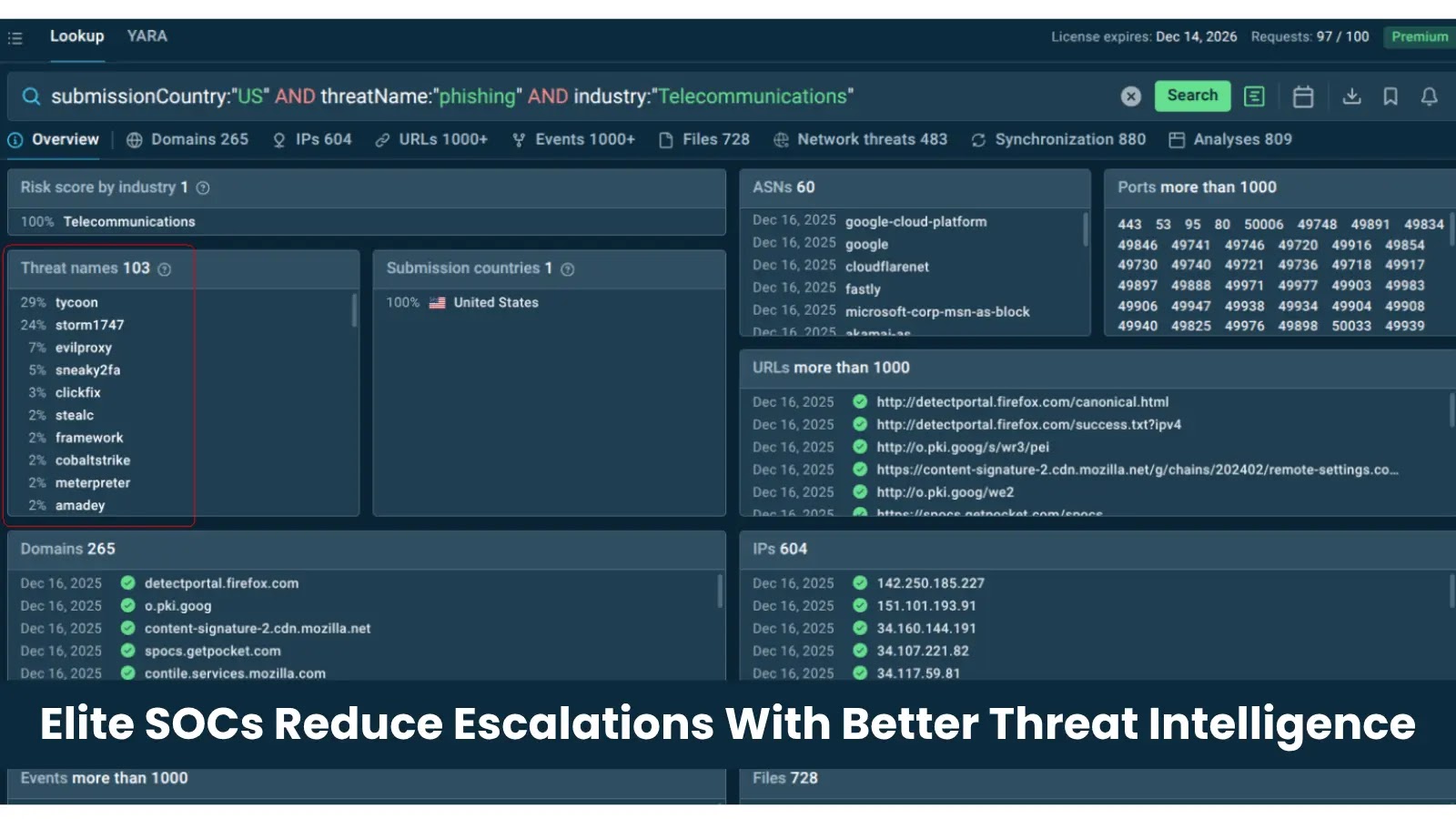
To mitigate excessive escalations, it’s crucial to equip Tier-1 analysts with comprehensive, real-time threat intelligence. By providing immediate access to detailed information about indicators of compromise (IOCs), analysts can make informed decisions without defaulting to escalation.
For instance, utilizing tools that offer instant, context-rich data on IOCs can transform the triage process. When an analyst encounters a suspicious IP address, they can quickly determine its association with known malicious activities, such as its role as a command-and-control endpoint in recent malware campaigns. This immediate context allows the analyst to confidently resolve the alert at Tier-1, reducing the need for escalation.
Implementing Effective Strategies
To reduce unnecessary escalations, SOCs can adopt the following strategies:
1. Comprehensive Training: Regular training sessions can enhance the analytical skills of Tier-1 analysts, enabling them to handle a broader range of alerts independently.
2. Advanced Tool Integration: Incorporating tools that provide real-time threat intelligence and automated analysis can streamline the triage process, allowing analysts to make quicker, more informed decisions.
3. Robust Feedback Mechanisms: Establishing clear communication channels between Tier-1 and Tier-2 teams ensures that analysts receive feedback on escalated alerts, fostering continuous learning and improvement.
4. Regular Review of Detection Rules: Periodically updating and refining detection rules can minimize false positives, reducing the volume of alerts that require manual review.
5. Workload Management: Implementing strategies to manage alert volumes, such as prioritization protocols and automated filtering, can prevent analyst burnout and maintain operational efficiency.
Measuring Success
To assess the effectiveness of these strategies, SOCs should monitor key performance indicators (KPIs) such as:
– Escalation Rates: A decrease in the percentage of alerts escalated from Tier-1 to Tier-2 indicates improved triage capabilities.
– MTTD and MTTR: Reductions in detection and response times reflect enhanced operational efficiency.
– Analyst Satisfaction and Retention: Improved job satisfaction and lower turnover rates among Tier-1 analysts suggest a healthier work environment.
– False Positive Rates: A decline in false positives indicates more accurate detection mechanisms and better alert filtering.
Conclusion
Reducing unnecessary escalations within a SOC is not merely a technical challenge but an operational imperative. By empowering Tier-1 analysts with the right tools, training, and support, organizations can enhance their SOC’s efficiency, reduce response times, and strengthen their overall security posture. Investing in these areas not only optimizes resource utilization but also fortifies the organization’s defenses against an ever-evolving threat landscape.