DarkSword Exploit Leaks on GitHub: A Critical Threat to Outdated iOS Devices
In a significant development for iOS security, the DarkSword exploit, previously identified by Google’s Threat Intelligence Group, has been publicly released on GitHub. This leak poses a substantial risk to users operating older versions of iOS and iPadOS, underscoring the critical need for timely software updates.
Understanding the DarkSword Exploit
DarkSword is a sophisticated exploit that chains multiple vulnerabilities within iOS and iPadOS to compromise devices running outdated software versions. By leveraging weaknesses in WebKit and other system components, attackers can gain unauthorized access to user data or even take full control of the device. The exploit specifically targets devices that have not been updated to the latest available versions of iOS and iPadOS.
The Implications of the GitHub Leak
The recent publication of DarkSword’s code on GitHub significantly amplifies the threat landscape. With the exploit now accessible to a broader audience, including potential malicious actors, the likelihood of widespread attacks has increased. Security experts have expressed deep concern over this development. Matthias Frielingsdorf, co-founder of iVerify, stated, This is bad. They are way too easy to repurpose… The exploits will work out of the box. There is no iOS expertise required.
Apple’s Response and Recommendations
In response to the emerging threats posed by DarkSword and similar exploits, Apple has taken proactive measures. The company released emergency updates on March 11, 2026, specifically designed for devices unable to run the latest versions of iOS and iPadOS. These updates aim to patch the vulnerabilities exploited by DarkSword, thereby safeguarding users from potential attacks.
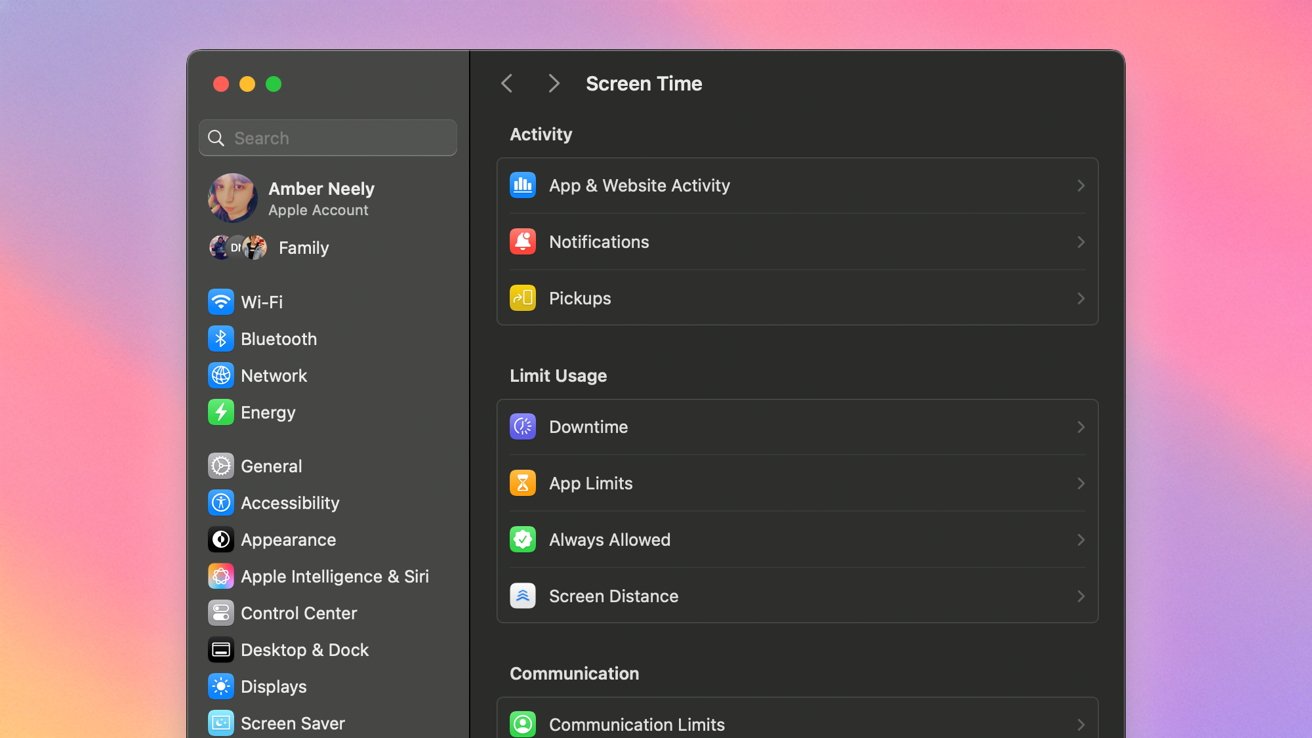
Apple has also emphasized the importance of enabling Lockdown Mode, a feature introduced to provide an additional layer of security against sophisticated cyber threats. Lockdown Mode restricts certain functionalities that could be exploited by malicious software, offering enhanced protection for users who may be at higher risk.
The Broader Context of iOS Exploits
The DarkSword incident is not an isolated case. Over the years, several significant exploits have targeted iOS devices:
– Coruna Exploit: Disclosed by Google’s Threat Intelligence Group and iVerify, Coruna chains multiple vulnerabilities to target iPhones running older iOS versions. It leverages five full iOS exploit chains and 23 vulnerabilities to compromise devices running iOS 13 through iOS 17.2.1. ([9to5mac.com](https://9to5mac.com/2026/03/03/google-and-iverify-reveal-government-grade-iphone-exploit-kit-spreading-to-hackers/?utm_source=openai))
– KeyRaider Malware: In 2015, KeyRaider stole over 225,000 Apple IDs from jailbroken devices across 18 countries. The malware intercepted app purchase requests and emulated the iTunes protocol to make unauthorized purchases. ([9to5mac.com](https://9to5mac.com/2015/09/01/ios-jailbreak-keyraider-malware/?utm_source=openai))
– Checkm8 Exploit: Discovered in 2019, Checkm8 is an unpatchable bootrom exploit affecting iPhone 4s through iPhone X. It allows for permanent jailbreaking of affected devices, posing a significant security risk. ([9to5mac.com](https://9to5mac.com/2019/09/27/ios-unpatchable-ios-exploit-jailbreak-iphone-x/?utm_source=openai))
– Pegasus Spyware: In 2023, Apple released iOS 16.6.1 to fix a zero-day exploit used by Pegasus spyware, which could compromise iPhones without any user interaction. ([9to5mac.com](https://9to5mac.com/2023/09/07/apple-fixed-zero-day-exploit-used-by-pegasus-spyware-with-ios-16-6-1/?extended-comments=1&utm_source=openai))
The Importance of Regular Software Updates
These incidents highlight a recurring theme: the critical importance of keeping devices updated with the latest software releases. Regular updates not only provide new features but also patch known vulnerabilities that could be exploited by malicious actors. Users are strongly encouraged to:
1. Regularly Check for Updates: Ensure that your device is running the latest version of iOS or iPadOS available for your model.
2. Enable Automatic Updates: This feature allows your device to download and install updates automatically, reducing the risk of missing critical security patches.
3. Utilize Security Features: Features like Lockdown Mode can provide additional protection against sophisticated exploits.
4. Be Cautious with Third-Party Software: Avoid jailbreaking your device or installing software from untrusted sources, as these actions can expose your device to additional risks.
Conclusion
The public release of the DarkSword exploit on GitHub serves as a stark reminder of the ever-present threats in the digital landscape. While technology companies like Apple work diligently to patch vulnerabilities, the responsibility also lies with users to ensure their devices are updated and secure. By staying informed and proactive, users can significantly reduce their risk of falling victim to such exploits.