Cybercriminals Impersonate IT Support to Deploy Havoc C2 Framework
Cybersecurity researchers have identified a sophisticated campaign where attackers pose as IT support personnel to infiltrate organizations and deploy the Havoc command-and-control (C2) framework. This method serves as a precursor to data theft or ransomware attacks.
The security firm Huntress detected these intrusions last month across five partner organizations. The attackers initiated their scheme with a spam email campaign, followed by phone calls from individuals claiming to be from the IT department. This combination activated a multi-layered malware delivery system.
In one notable case, the attackers progressed from initial access to compromising nine additional endpoints within eleven hours. They deployed a mix of custom Havoc Demon payloads and legitimate Remote Monitoring and Management (RMM) tools to maintain persistence. The rapid lateral movement suggests objectives of data exfiltration, ransomware deployment, or both.
This approach mirrors tactics previously associated with the Black Basta ransomware group, known for email bombing and Microsoft Teams phishing attacks. Although Black Basta has been inactive since a public leak of its internal communications last year, the recurrence of these methods indicates that former affiliates may have joined other ransomware operations or that rival groups have adopted similar strategies.
Attack Chain Breakdown:
1. Email Overload: The attackers begin by flooding the target’s inbox with spam emails.
2. Impersonation Calls: They then call the victims, posing as IT support, and persuade them to grant remote access via tools like Quick Assist or AnyDesk.
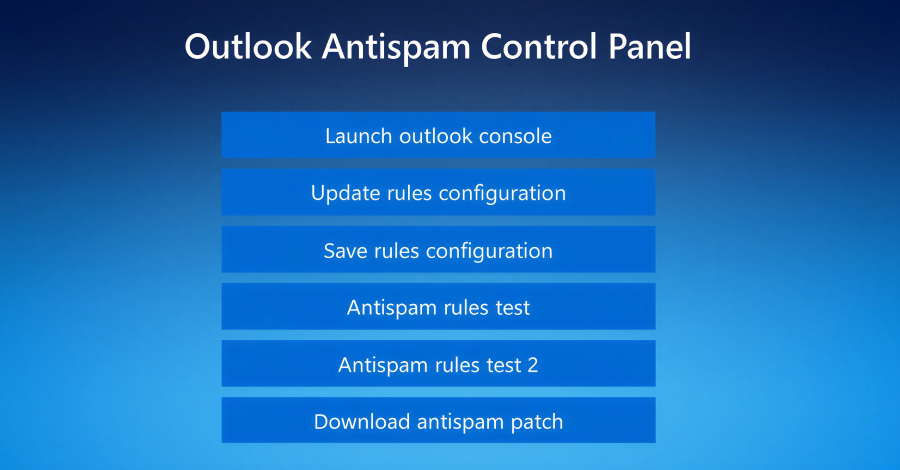
3. Fake Microsoft Page: Once access is obtained, the attackers direct the victim’s browser to a counterfeit Microsoft page hosted on Amazon Web Services (AWS). This page prompts the user to enter their email address to update Outlook’s anti-spam rules.
4. Credential Harvesting: Clicking the Update rules configuration button triggers a script that overlays a password entry prompt. This tactic not only captures the user’s credentials but also adds an air of legitimacy to the process.
5. Malware Deployment: The user is then prompted to download an anti-spam patch, which executes a legitimate binary (e.g., ADNotificationManager.exe) to sideload a malicious DLL. This DLL evades detection and runs the Havoc shellcode payload by initiating a thread containing the Demon agent.
Some DLLs, like vcruntime140_1.dll, employ advanced techniques to bypass security measures. These include control flow obfuscation, timing-based delays, and methods such as Hell’s Gate and Halo’s Gate to hook into ntdll.dll functions, effectively circumventing endpoint detection and response (EDR) systems.
After successfully deploying the Havoc Demon on the initial host, the attackers move laterally within the network. They create scheduled tasks to launch the Havoc Demon payload upon system reboot, ensuring persistent remote access. In some instances, they deploy legitimate RMM tools like Level RMM and XEOX on compromised hosts, diversifying their persistence methods.
Key Takeaways:
– Social Engineering: Attackers are increasingly impersonating IT staff and making direct phone calls to enhance their success rates.
– Advanced Evasion: Techniques once reserved for large-scale or state-sponsored attacks are now common, including defense evasion and customized malware to bypass signature-based detection.
– Rapid Progression: Attacks are executed swiftly, moving from initial compromise to lateral movement in a short timeframe.
– Persistent Access: Multiple methods are employed to maintain access, including deploying legitimate tools for persistence.
This campaign exemplifies how modern adversaries layer sophistication at every stage: using social engineering to gain entry, DLL sideloading to remain undetected, and diversified persistence strategies to withstand remediation efforts.