Cybercriminals Exploit Fake Google Meet Pages to Deploy Remote Access Trojans
In a recent wave of cyberattacks, threat actors have been leveraging counterfeit Google Meet pages to deceive users into executing malicious PowerShell scripts, resulting in the installation of Remote Access Trojans (RATs) on their systems. This sophisticated social engineering tactic, known as ClickFix, manipulates users into bypassing standard security protocols through manual actions.
The Deceptive Mechanism
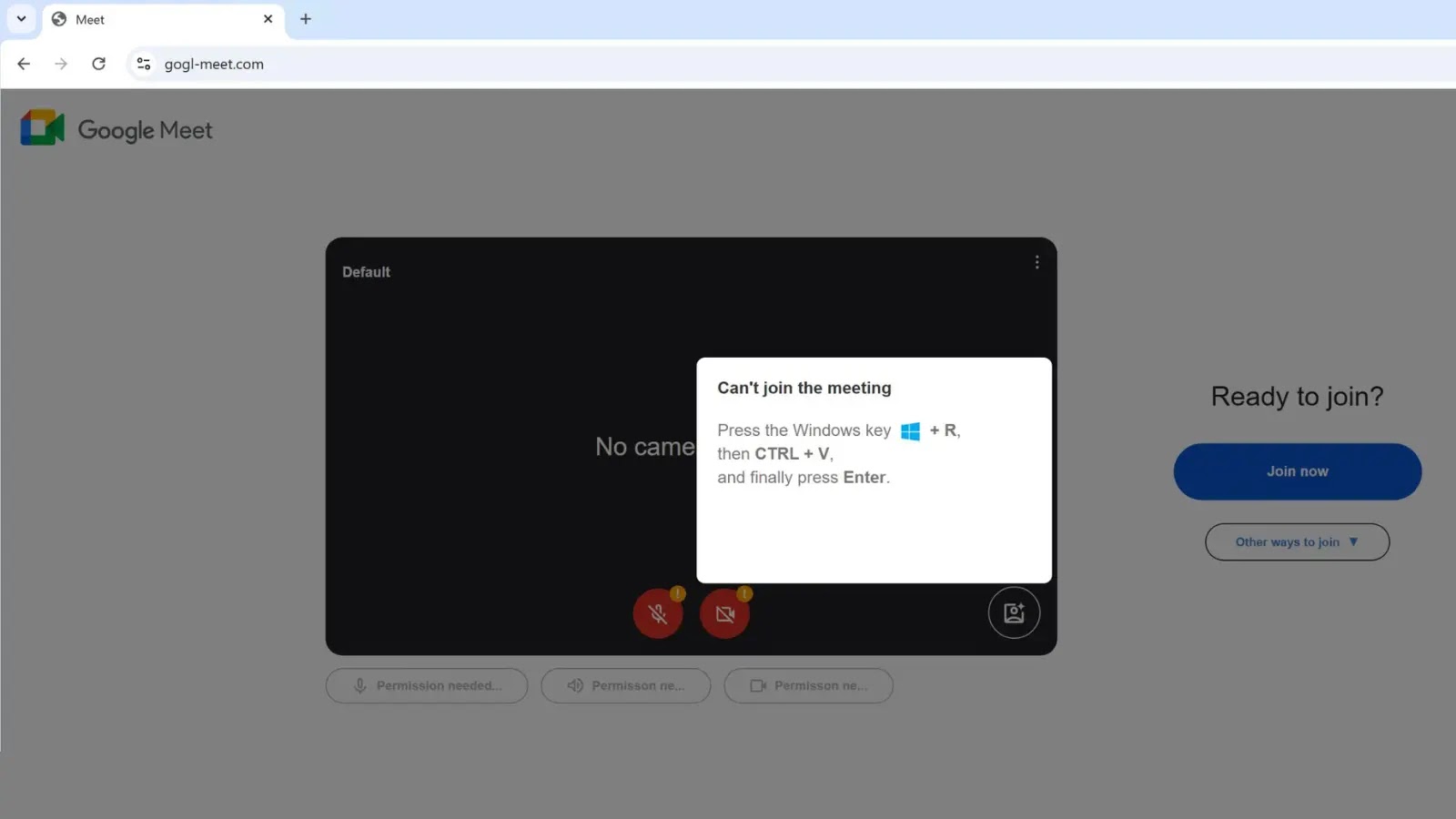
The attack initiates when a user visits a fraudulent Google Meet website, such as gogl-meet[.]com, which closely mimics the authentic interface. Upon attempting to join a meeting, the user encounters a pop-up error message indicating issues with their camera or microphone, titled Can’t join the meeting. Unlike traditional phishing methods that solicit login credentials, this scheme presents a technical fix requiring specific user actions.
The user is instructed to perform a sequence of keystrokes:
1. Press the Windows key + R to open the Run dialog box.
2. Press CTRL + V to paste a command.
3. Press Enter to execute the command.
Unbeknownst to the user, clicking the Join now or Fix button on the page triggers a JavaScript function that copies a malicious PowerShell script to their clipboard. By following the manual keystroke instructions, the user unwittingly pastes and executes this script via the Windows Run dialog, effectively bypassing browser-based security filters such as Google Safe Browsing and SmartScreen.
Forensic Analysis and Indicators
Incident response activities involving gogl-meet[.]com have confirmed that this chain leads to a RAT infection. Forensic analysis of affected systems identified the infection’s root cause through the Master File Table (MFT). Specifically, the MFT entry for the dropped payload revealed critical origin data in its Alternative Data Stream (ADS), capturing both the ClickFix downloaded file and the referrer URL gogl-meet[.]com.
This forensic artifact is crucial for defenders, as it definitively links the execution of the RAT back to the browser-based social engineering event rather than a typical drive-by download or email attachment.
A distinct characteristic of this wave is the obfuscation used within the PowerShell payload itself. Threat actors have begun padding the malicious script with extensive comments containing trusted visual symbols, such as repeated green check marks. When a user pastes the content into the small Windows Run box, these symbols may be the only visible text, visually reassuring the victim that the command is verified or safe.
This tactic also serves a technical purpose: it can push the actual malicious code (often an IEX download cradle) out of the immediate visible area of the dialog box, masking the script’s true intent.
Evolution of ClickFix Attacks
While ClickFix (also associated with clusters like ClearFake) gained significant traction throughout 2024, this latest iteration demonstrates a shift toward hyper-targeted branding. Early campaigns impersonated generic browser updates or Word errors. Still, the shift to Google Meet simulation suggests a pivot toward targeting corporate environments where video conferencing glitches are a common, trusted friction point.
Defense Strategies
To mitigate the risks associated with such sophisticated social engineering attacks, organizations and individuals should adopt comprehensive security measures:
1. User Education and Awareness: Regular training sessions should be conducted to educate users about the latest phishing tactics and the importance of verifying the authenticity of web pages and error messages.
2. Technical Safeguards: Implement endpoint detection and response solutions capable of monitoring and analyzing PowerShell execution. Application whitelisting can prevent unauthorized scripts from running, and web application firewalls can block access to known malicious domains.
3. Incident Response Planning: Develop and regularly update incident response plans to quickly address and mitigate the effects of potential breaches.
4. Regular System Updates: Ensure that all systems and software are up-to-date with the latest security patches to reduce vulnerabilities that could be exploited by attackers.
By staying informed about evolving cyber threats and implementing robust security practices, organizations can better protect themselves against sophisticated attacks like the ClickFix technique.