A critical local privilege escalation (LPE) vulnerability has been identified in Microsoft’s Windows Error Reporting (WER) service, designated as CVE-2026-20817. This flaw enables authenticated users with minimal privileges to execute arbitrary code with SYSTEM-level access, posing a significant security risk to affected systems.
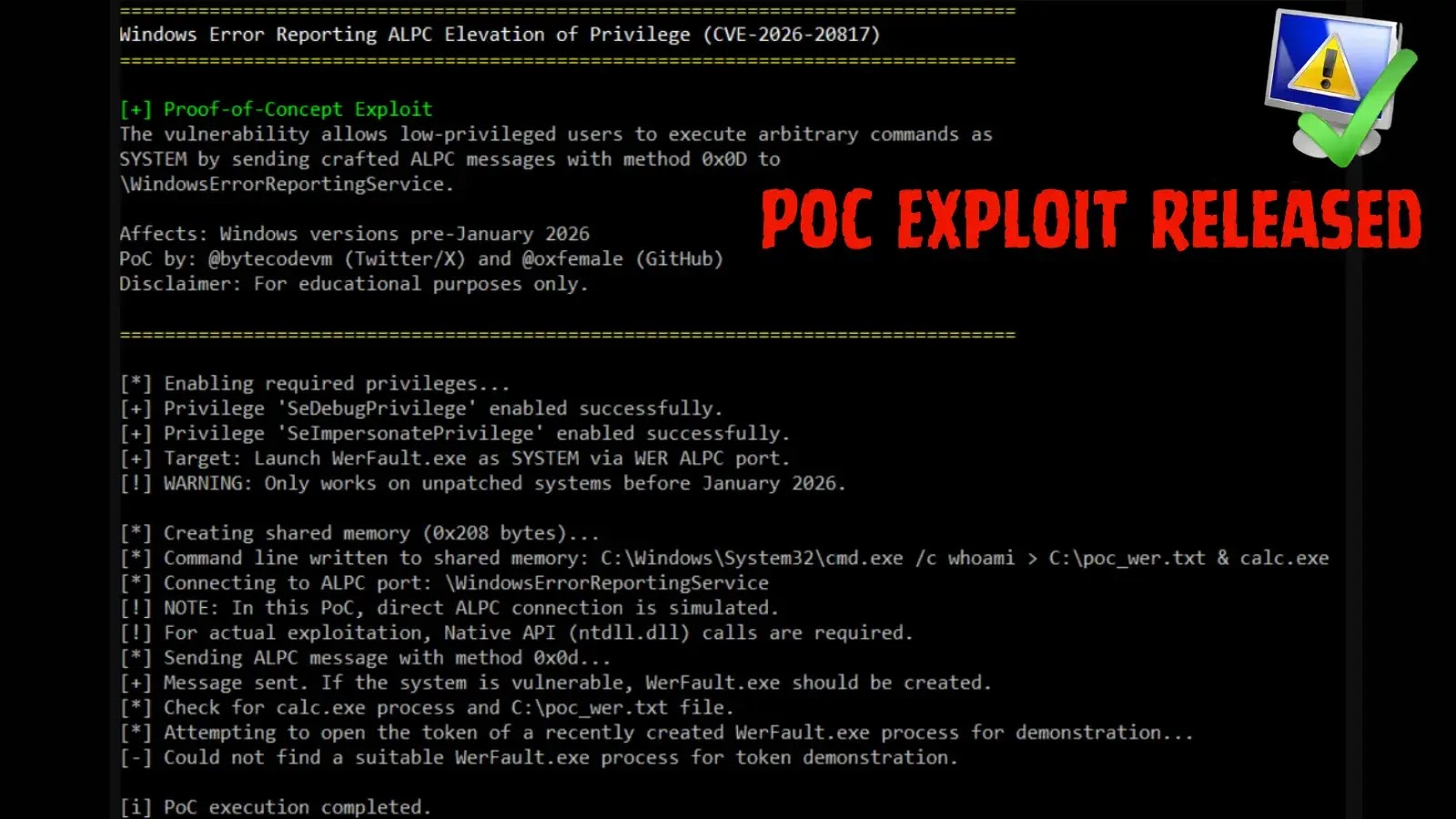
The vulnerability resides in the WER service’s handling of the Advanced Local Procedure Call (ALPC) protocol, specifically within the `SvcElevatedLaunch` method (method 0x0D). The service fails to adequately validate the permissions of the calling user, allowing attackers to exploit this oversight. By crafting a shared memory block containing a malicious command line and sending an ALPC message to the WER service, an attacker can prompt the service to launch `WerFault.exe` with the supplied parameters. Since the WER service operates with elevated privileges, the spawned process inherits SYSTEM-level access, granting the attacker extensive control over the system.
Exploit Execution Steps:
1. Create Shared Memory: Develop a shared memory block containing the desired malicious command line.
2. Connect to WER ALPC Port: Establish a connection to the WER service’s ALPC port named `\WindowsErrorReportingService`.
3. Send ALPC Message (Method 0x0D): Dispatch an ALPC message using method 0x0D, including the client process ID, the shared memory handle, and the command-line length.
4. Trigger Command Execution: The WER service duplicates the handle and initiates `WerFault.exe` with the provided command line, resulting in the execution of the malicious code with SYSTEM privileges.
This vulnerability affects all versions of Windows 10 and Windows 11 prior to the January 2026 updates, as well as Windows Server 2019 and Windows Server 2022. Microsoft addressed this issue in their January 2026 Security Update.
Mitigation Recommendations:
– Apply Security Patches: Ensure that all systems are updated with the latest security patches released by Microsoft to remediate this vulnerability.
– Monitor System Behavior: Implement monitoring for unusual child processes spawned by `WerFault.exe` and any irregular behaviors associated with SYSTEM tokens to detect potential exploitation attempts.
By promptly applying the necessary updates and maintaining vigilant monitoring practices, organizations can protect their systems from potential exploits targeting this vulnerability.