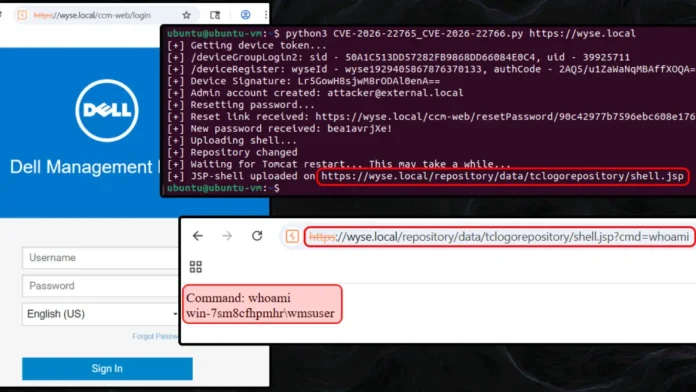
Critical Vulnerabilities in Dell Wyse Management Suite Lead to Full System Compromise
Recent security analyses have uncovered critical vulnerabilities within Dell’s Wyse Management Suite (WMS) On-Premises, which, when exploited in tandem, can lead to complete system compromise. These findings underscore the importance of timely software updates and vigilant system management.
Understanding the Vulnerabilities
Two primary vulnerabilities have been identified:
1. CVE-2026-22765 (CVSS 8.8): This flaw pertains to missing authorization checks, allowing a low-privileged remote attacker to escalate their privileges to that of a full administrator. The absence of proper authorization mechanisms means that certain functions or API endpoints can be accessed without the necessary permissions, leading to potential unauthorized actions within the system. ([dell.com](https://www.dell.com/support/kbdoc/en-us/000429141/dsa-2026-103?utm_source=openai))
2. CVE-2026-22766 (CVSS 7.2): This vulnerability involves unrestricted file uploads, enabling a high-privileged remote attacker to execute arbitrary code on the underlying system. The system fails to validate the type or content of uploaded files adequately, allowing malicious files to be introduced and executed, potentially leading to remote code execution. ([dell.com](https://www.dell.com/support/kbdoc/en-us/000429141/dsa-2026-103?utm_source=openai))
The Exploitation Chain
The path to unauthenticated remote code execution involves a series of steps that exploit device registration flaws, unprotected API endpoints, and path traversal bypasses:
1. Device Registration Exploit: In the default configuration of the on-premises version, an attacker can register a rogue device by submitting an empty group token. This action places the device into a restricted quarantine group but returns a device identifier and authentication code, providing the initial foothold needed to interact with the WMS API.
2. API Endpoint Manipulation: With a valid device signature, the attacker can exploit improperly exposed Active Directory (AD) import routes. By sequentially calling the `importADUserGroups` and `addRoleToADGroup` API endpoints, the attacker constructs a custom role group with administrative privileges. The `importADUsers` endpoint is then manipulated to provision a new administrator account linked to this role.
3. Authentication Bypass: Accessing the newly created account requires overcoming an authentication barrier. Attackers have two distinct methods to achieve this:
– Password Reset Exploit: By importing the administrator with an empty Active Directory User Principal Name (UPN), the system’s AD user check fails, allowing the attacker to request a password reset to an external email address.
– LDAP Configuration Exploit: In Pro environments with LDAP configured, an attacker can supply the identifier of a compromised low-privileged domain user during the import process, allowing them to authenticate as the administrator using standard domain credentials.
4. Deployment of Malicious Web Shell: With administrative privileges, the attacker can deploy a malicious JSP web shell. Although the application implements filters against traditional path traversal attacks, an administrator can maliciously reconfigure the local file repository settings. By modifying the repository path to point directly to the Tomcat web root directory and issuing an API command to restart the Tomcat service, the attacker clears the path configuration cache and bypasses all file upload restrictions. A JSP payload can then be uploaded through an image upload route, resulting in complete unauthenticated remote code execution.
Mitigation and Recommendations
Dell addressed these security flaws with the release of WMS version 5.5 on February 23, 2026. The vulnerabilities specifically impact the on-premises deployments of both the free Standard and paid Pro editions. System administrators managing Dell WMS On-Premises deployments are strongly advised to update their infrastructure immediately to secure their environments against these attack vectors.
Conclusion
The discovery of these vulnerabilities highlights the critical importance of regular software updates and proactive security measures. Organizations utilizing Dell’s Wyse Management Suite should prioritize patching their systems to prevent potential exploits that could lead to full system compromise.