Critical Supply Chain Attack Compromises Axios NPM Packages
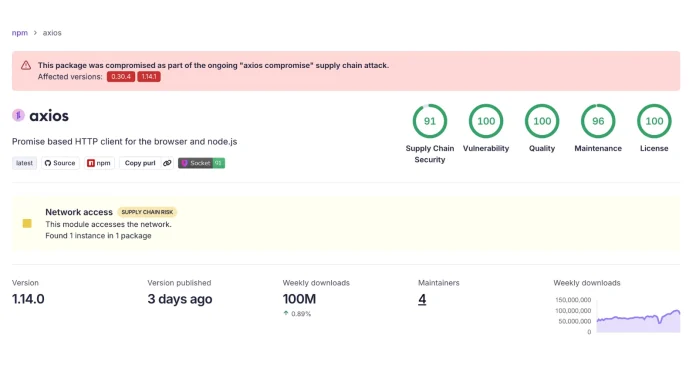
A sophisticated supply chain attack has recently targeted Axios, a widely utilized HTTP client in the JavaScript ecosystem, by introducing a malicious transitive dependency into the official npm registry. Axios, integral to numerous frontend frameworks, backend microservices, and enterprise applications, boasts approximately 83 million weekly downloads on npm.
Details of the Compromise
The attack involved the unauthorized publication of new Axios versions that automatically incorporate `[email protected]`, a newly introduced package confirmed to contain malicious code. Given Axios’s extensive integration in modern web development, the potential impact of this supply chain breach is substantial, necessitating immediate action from affected users.
According to security firm Socket, the attackers deviated from Axios’s standard release procedures. Typically, Axios maintainers publish tagged releases on GitHub concurrently with their npm releases. However, the compromised npm versions do not appear in the project’s official GitHub repository tags. At the time of the incident, `v1.14.0` remained the most recent visible tag on GitHub, indicating that the malicious updates were pushed directly to the npm registry outside the normal deployment pipeline. This bypass of standard version control suggests a highly coordinated effort to inject malicious code discreetly.
Timeline of the Attack
The malicious dependency, `[email protected]`, was published to the npm registry on March 30, 2026, at 23:59:12 UTC. Within minutes, the compromised Axios versions were made live. Automated malware detection by Socket flagged the anomalous `plain-crypto-js` package shortly after at 00:05:41 UTC on March 31, highlighting the rapid execution designed to maximize infection before security tools could respond.
Attack Methodology
To evade immediate detection during the initial infection phase, the attackers introduced minimal alterations to the primary Axios codebase. The sole modification was adding the malicious `plain-crypto-js` package to the dependency tree. Utilizing small, targeted changes is a conventional and highly effective tactic in supply chain attacks. This approach allows threat actors to execute arbitrary code through transitive dependencies while avoiding the scrutiny that typically accompanies large codebase modifications or logic changes.
Investigation Findings
Investigations into the registry logs reveal that the malicious package is associated with the npm publisher account `jasonsaayman`. The appearance of this account in the compromised dependency chain raises significant concerns regarding unauthorized package publishing capabilities. It points toward a potential account takeover, compromised developer credentials, or a hijacked session token that allowed the attackers to authenticate and publish the malicious artifacts directly to the npm registry.
Immediate Actions Required
Security teams, DevOps engineers, and developers must immediately audit their software supply chains to identify and remove the compromised components. Project maintainers should thoroughly review project lockfiles, dependency graphs, feature branches, and open pull requests for any exposure to the affected versions.
Compromised Package Versions and Malicious Dependency:
– Axios 1.14.1: `[email protected]`
– Axios 0.30.4: `[email protected]`
– plain-crypto-js 4.2.1: Primary Malicious Payload
If any of these specific package versions are detected within your environment, it is imperative to remove them entirely or roll back your dependencies to a known safe release, such as Axios `1.14.0`, to prevent the execution of the injected code.
Broader Context of Supply Chain Attacks
This incident is part of a growing trend of supply chain attacks targeting popular npm packages. In recent months, several high-profile attacks have been reported:
– Massive Shai-Halud Supply Chain Attack: In September 2025, a large-scale attack dubbed Shai-Halud compromised 477 npm packages, including those from CrowdStrike. The attack involved stealthy backdoors and trojanized modules designed to siphon credentials, exfiltrate source code, and enable remote code execution on developer machines. The adversary’s campaign began in early August 2025, using compromised maintainer accounts to publish malicious updates under minor version bumps. Each update injected a small, obfuscated payload within the module entry file, which reached out to a command-and-control server to fetch a second-stage payload. The payload searched project directories for `.env` files, SSH private keys, and Git credentials, then transmitted them in encrypted form back to the attacker’s infrastructure. Detection strategies include integrating tools like `npm audit`, Snyk, or OWASP Dependency-Check into CI pipelines to flag anomalous version releases. Mitigations involve locking dependency versions, rotating secrets, and auditing dependencies. ([cybersecuritynews.com](https://cybersecuritynews.com/shai-halud-supply-chain-attack/?utm_source=openai))
– CISA Warns of Shai-Hulud Self-Replicating Worm: In September 2025, the Cybersecurity and Infrastructure Security Agency (CISA) issued an urgent security alert in response to a large-scale software supply chain attack on npmjs.com. A self-replicating worm, dubbed Shai-Hulud, infiltrated more than 500 npm packages, injecting malicious code that aggressively spread by abusing developer credentials and npm publish workflows. The worm deployed a sophisticated payload that scanned for sensitive credentials stored in environment variables and local configuration files, targeting GitHub Personal Access Tokens and API keys for AWS, GCP, and Azure. Once harvested, credentials were exfiltrated to an actor-controlled endpoint and simultaneously uploaded to a public GitHub repository named Shai-Hulud via the GitHub/user/repos API. Mitigations recommended by CISA include examining all package-lock.json and yarn.lock files to identify packages released after September 16, 2025, rotating all developer credentials, implementing IDS/IPS rules to monitor anomalous connections, and pinning dependencies to known safe versions. ([cybersecuritynews.com](https://cybersecuritynews.com/cisa-shai-hulud-npm-attack/?utm_source=openai))
– Ripple XRPL Official NPM Package Hijacked: In April 2025, the official XRPL (Ripple) NPM package, serving as the JavaScript SDK for the XRP Ledger, was compromised with malicious code designed to steal cryptocurrency private keys. The malicious versions—4.2.1, 4.2.2, 4.2.3, 4.2.4, and 2.14.2—did not correspond with any official releases on the project’s GitHub repository, raising red flags. Technical analysis revealed a suspicious function `checkValidityOfSeed` embedded in the package, designed to send private key information to an external domain. The malicious code activated when users created new wallets or interacted with existing ones, sending sensitive cryptographic information to the attackers. In response, clean versions (4.2.5 and 2.14.3) were quickly released to replace the compromised packages. Users who may have installed any of the compromised packages between April 21 and April 22 were urged to inspect their network logs for outbound connections to the suspicious domain. ([cybersecuritynews.com](https://cybersecuritynews.com/ripple-xprl-official-npm-package-hijacked/?utm_source=openai))
Conclusion
The recent compromise of Axios underscores the critical importance of vigilance in managing software dependencies. Supply chain attacks are becoming increasingly sophisticated, targeting widely used packages to maximize their impact. Developers and organizations must implement robust security practices, including regular audits of dependencies, strict version control, and immediate response protocols to mitigate the risks associated with such attacks.