Critical Docker Vulnerability CVE-2026-34040 Enables Authorization Bypass and Potential Host Compromise
A significant security flaw has been identified in Docker Engine, designated as CVE-2026-34040, carrying a CVSS score of 8.8. This vulnerability allows attackers to circumvent authorization plugins (AuthZ) under certain conditions, potentially leading to unauthorized access and control over host systems.
Background and Discovery
CVE-2026-34040 arises from an incomplete resolution of a prior vulnerability, CVE-2024-41110, which was disclosed in July 2024. The initial fix failed to adequately address issues related to oversized HTTP request bodies, leaving the system susceptible to exploitation. Security researchers Asim Viladi Oglu Manizada, Cody, Oleh Konko, and Vladimir Tokarev independently discovered and reported this flaw. Docker has since released a patch in version 29.3.1 to mitigate this issue.
Technical Details
The vulnerability exploits the Docker daemon’s handling of API requests. By crafting a specific API request, an attacker can cause the Docker daemon to forward the request to an authorization plugin without including the request body. As a result, the authorization plugin may approve a request it would typically deny if it had access to the complete request body. This flaw is particularly concerning for systems that rely on authorization plugins to enforce access control policies.
Attack Scenario
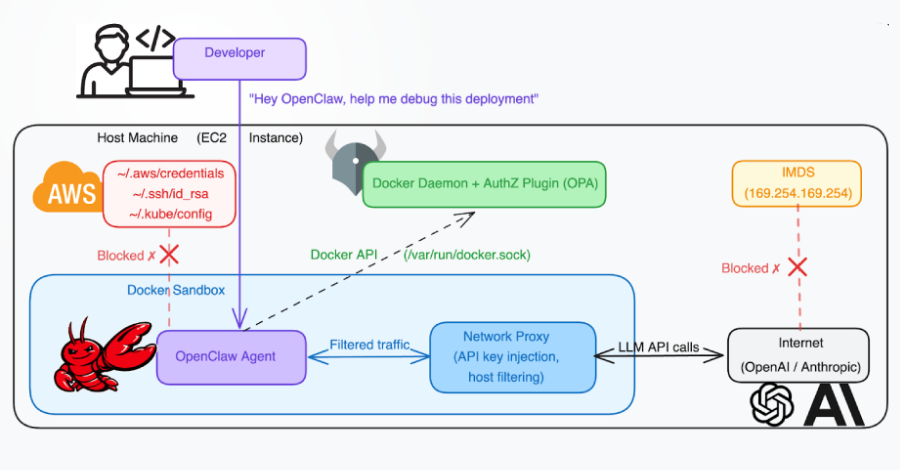
In a potential attack scenario, an adversary with restricted Docker API access can manipulate a container creation request by padding it to exceed 1MB. This oversized request is then dropped before reaching the authorization plugin, effectively bypassing the intended security checks. Consequently, the Docker daemon processes the full request, leading to the creation of a privileged container with root access to the host system. This access can expose sensitive information such as AWS credentials, SSH keys, and Kubernetes configurations, posing a severe security risk.
Implications for AI Coding Agents
The vulnerability also has implications for artificial intelligence (AI) coding agents operating within Docker-based environments. An AI agent can be deceived into executing a prompt injection hidden within a specially crafted GitHub repository. This deception can lead to the execution of malicious code that exploits CVE-2026-34040, resulting in the creation of a privileged container and mounting of the host file system. With such access, an attacker can extract cloud service credentials and potentially gain control over cloud accounts, Kubernetes clusters, and production servers.
Mitigation Strategies
To protect systems from this vulnerability, the following measures are recommended:
– Immediate Upgrade: Update Docker Engine to version 29.3.1 or later to incorporate the security patch addressing CVE-2026-34040.
– Access Control: Limit access to the Docker API to trusted entities, adhering to the principle of least privilege.
– Rootless Mode: Operate Docker in rootless mode, which maps the root user inside the container to an unprivileged user on the host, thereby reducing the potential impact of a security breach.
– User Namespace Remapping: For environments where full rootless operation isn’t feasible, implement user namespace remapping to achieve similar UID mapping benefits.
Conclusion
CVE-2026-34040 represents a critical security vulnerability within Docker Engine, enabling attackers to bypass authorization mechanisms and potentially gain unauthorized access to host systems. Prompt application of the provided security patch and adherence to recommended security practices are essential to mitigate the risks associated with this flaw.