Closing Identity Gaps in 2026: Safeguarding Enterprises Against AI-Driven Threats
In 2026, Chief Information Security Officers (CISOs) and security leaders face a perplexing challenge: despite advancements in identity programs, enterprise risk continues to escalate. Recent research by the Ponemon Institute reveals that numerous applications within typical enterprises remain disconnected from centralized identity systems. These dark matter applications operate beyond standard governance, creating extensive, unmanaged attack surfaces now aggressively exploited by both human threat actors and autonomous AI agents.
The Unseen Danger: Disconnected Applications and AI Amplification
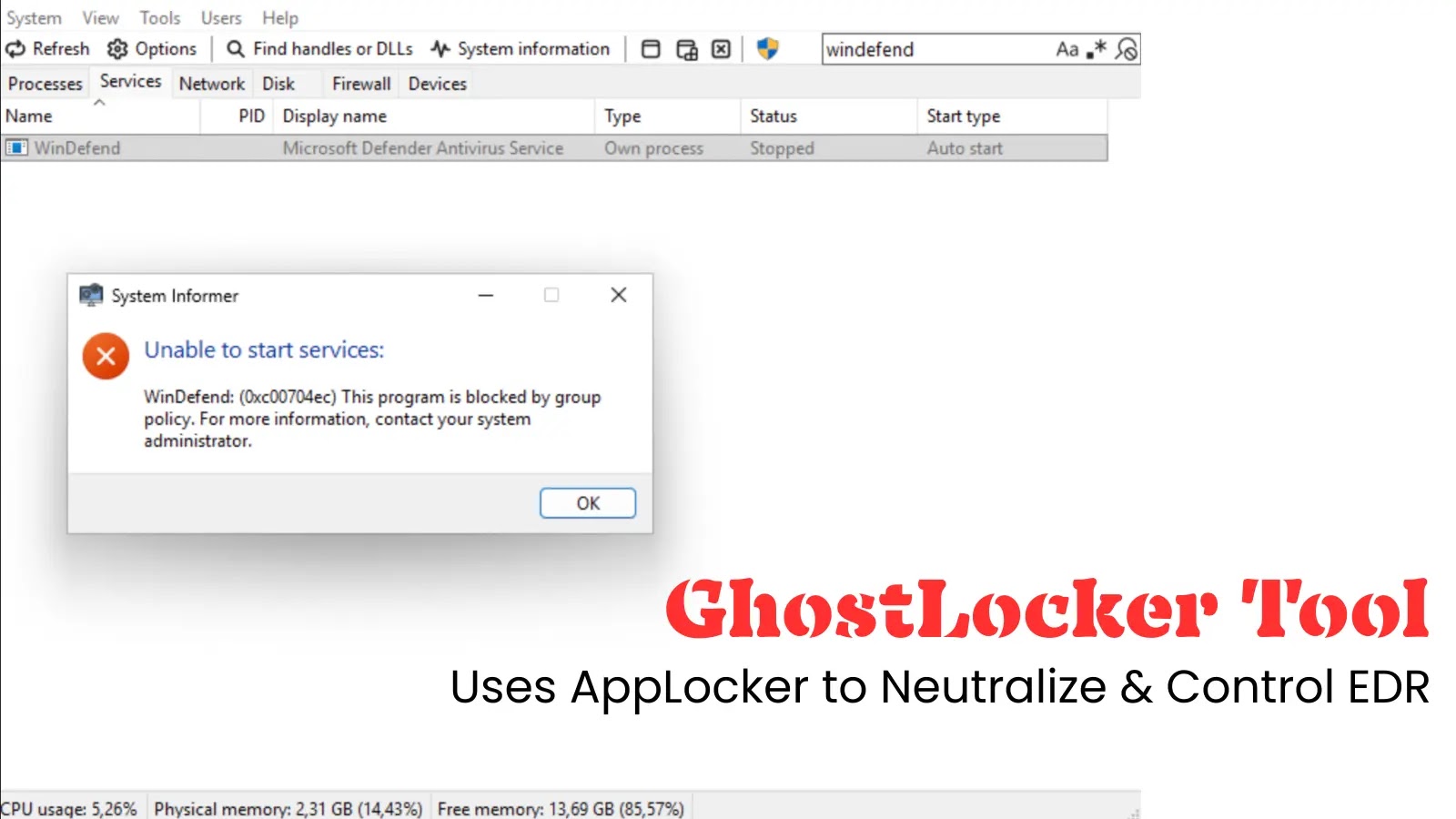
Modern enterprises have heavily invested in Identity and Access Management (IAM) and Zero Trust frameworks. However, the last mile of identity—encompassing legacy applications, localized accounts, and isolated Software as a Service (SaaS) platforms—remains a persistent blind spot.
The integration of AI into the workforce has transformed this gap from a compliance issue into a critical vulnerability. As organizations deploy AI copilots and autonomous agents to enhance productivity, these entities often require access to systems outside centralized control.
Consequently, AI agents inadvertently amplify credential risks by reusing outdated tokens and navigating paths of least resistance that security teams cannot monitor.
Join the 2026 Identity Maturity Briefing
To assist security leaders in addressing this Confidence Gap, The Hacker News is hosting an exclusive webinar featuring Mike Fitzpatrick from the Ponemon Institute and Matt Chiodi, Chief Security Officer at Cerby. They will analyze the latest findings from over 600 IT and security leaders and provide a tactical roadmap for closing identity gaps that lead to audit challenges and hinder digital initiatives.
In this session, participants will discover:
– Exclusive 2026 Benchmark Data: Assess how your identity maturity compares to industry peers.
– The Shadow AI Factor: Understand how AI agents are expanding your disconnected surface area.
– The Cost of Manual Management: Learn why relying on manual password and credential fixes is ineffective in 2026.
– Practical Remediation Steps: Explore strategies leading organizations are implementing to regain control over every application.
Why Attend?
For those leading identity, security, or compliance strategies, continuing with the status quo is no longer viable. This conversation aims to transition from theoretical maturity to operational control.
Secure your spot now to gain data-driven insights essential for protecting your organization’s most fragmented—and most targeted—asset: Identity.