Pixel Perfect Extension Exploited for Covert Script Injection and Security Header Removal
A seemingly innocuous browser extension, once endorsed with Google’s Featured badge, has been transformed into a tool for remote code execution following a clandestine change in ownership. This development has left thousands of users vulnerable to covert script injections and the removal of critical browser security headers. The incident underscores the potential risks associated with browser extensions, even those that appear trustworthy.
The Evolution of QuickLens
QuickLens, initially a practical tool enabling users to search images via Google Lens directly from their browsers, offered features such as screen capture, area selection, YouTube frame search, and Amazon product lookup. Its utility garnered a user base of approximately 7,000 and earned it Google’s Featured badge. The extension debuted on the Chrome Web Store on October 9, 2025. Merely two days later, on October 11, it was listed for sale on ExtensionHub—a marketplace where developers can sell their extensions along with their existing user base.
Ownership Transfer and Malicious Update
On February 1, 2026, ownership of QuickLens transferred to an unverified entity operating under the domain supportdoodlebuggle.top, registered as LLC Quick Lens—a disposable identity with no verifiable online presence. The privacy policy was relocated to kowqlak.lat. Shortly thereafter, on February 17, version 5.8 was released, covertly introducing a fully operational command-and-control (C2) platform to all 7,000 users.
This update incorporated three significant changes:
1. New C2 Server Integration: The background service worker was embedded with a new C2 server at api.extensionanalyticspro.top.
2. Additional Permissions: The extension requested two new permissions—declarativeNetRequestWithHostAccess and webRequest.
3. Implementation of rules.json File: A new rules.json file was introduced.
For most users, these changes appeared as standard permission update prompts, which are often accepted without scrutiny.
Security Header Stripping
The rules.json file had immediate and severe implications. It directed the extension to remove all essential browser security headers from every HTTP response, including Content-Security-Policy (CSP), X-Frame-Options, and X-XSS-Protection. This action effectively stripped protections from every visited page, exposing users to threats such as clickjacking, cross-site scripting, and unrestricted cross-domain requests.
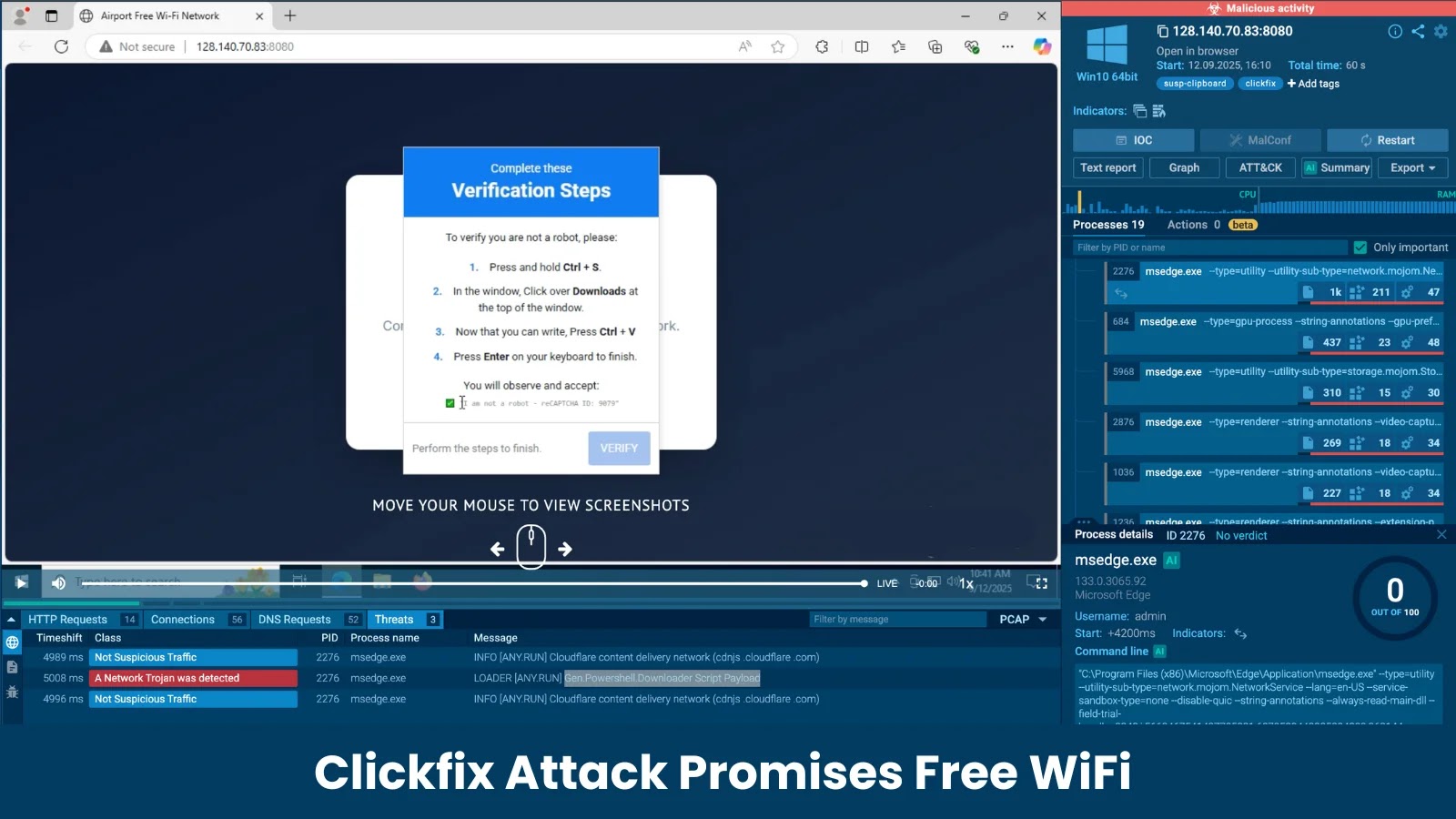
The Pixel Injection Mechanism
At the heart of this attack is a deceptively simple yet effective technique. The C2 server delivers JavaScript code to the extension as an array of strings, which is then stored in the browser’s local storage under the label `cached-agents-data`. Upon visiting any webpage, the extension retrieves this stored payload and executes it through a 1×1 transparent GIF image—a method researchers refer to as the pixel trick.
The extension creates a hidden image element within the webpage, with its source set to a 1×1 transparent GIF encoded as a base64 data URI. This image loads instantly without making any outbound network requests. The JavaScript payload from the C2 server is then attached as an inline `onload` attribute on that image element. As the browser processes the image, the script executes within the full context of the current page, granting the attacker direct access to all on-screen content.
This technique is particularly effective because Content-Security-Policy would typically block inline event handlers on well-configured sites. However, since version 5.8 globally stripped CSP headers, the payload runs unimpeded across every visited page.
Broader Implications and Similar Incidents
This incident is not isolated. Similar cases have been documented where browser extensions, after gaining a substantial user base and trust, were sold and subsequently weaponized. For instance, the Malicious11 campaign involved eleven Chrome extensions, all bearing Google’s verified badge, which collectively infected over 1.7 million users. These extensions, masquerading as productivity and entertainment tools, covertly implemented surveillance and hijacking capabilities.
Another notable case involved a malicious Chrome extension targeting digital marketers by posing as a productivity tool for Meta ad campaigns. Dubbed Madgicx Plus, this extension was distributed through deceptive websites and, once installed, hijacked user sessions to exfiltrate login tokens for Facebook and Instagram.
Mitigation Strategies
To protect against such threats, users and organizations should adopt the following measures:
1. Vigilant Extension Management: Regularly review and audit installed browser extensions. Be cautious of extensions requesting extensive permissions or those that have recently changed ownership.
2. Prompt Updates: Keep all software, including browser extensions, updated to the latest versions to benefit from security patches.
3. User Education: Educate users about the risks associated with browser extensions and the importance of scrutinizing permission requests.
4. Security Tools: Utilize security solutions that can detect and block malicious browser extensions.
5. Policy Enforcement: Implement organizational policies that restrict the installation of unapproved extensions.
By remaining vigilant and proactive, users can mitigate the risks posed by malicious browser extensions and safeguard their online security.