Cybercriminals Exploit Microsoft’s AzCopy for Stealthy Data Theft in Ransomware Attacks In a concerning evolution of cyber threats, ransomware operators are now repurposing Microsoft’s AzCopy—a […]
Author: The Daily Tech Feed Team
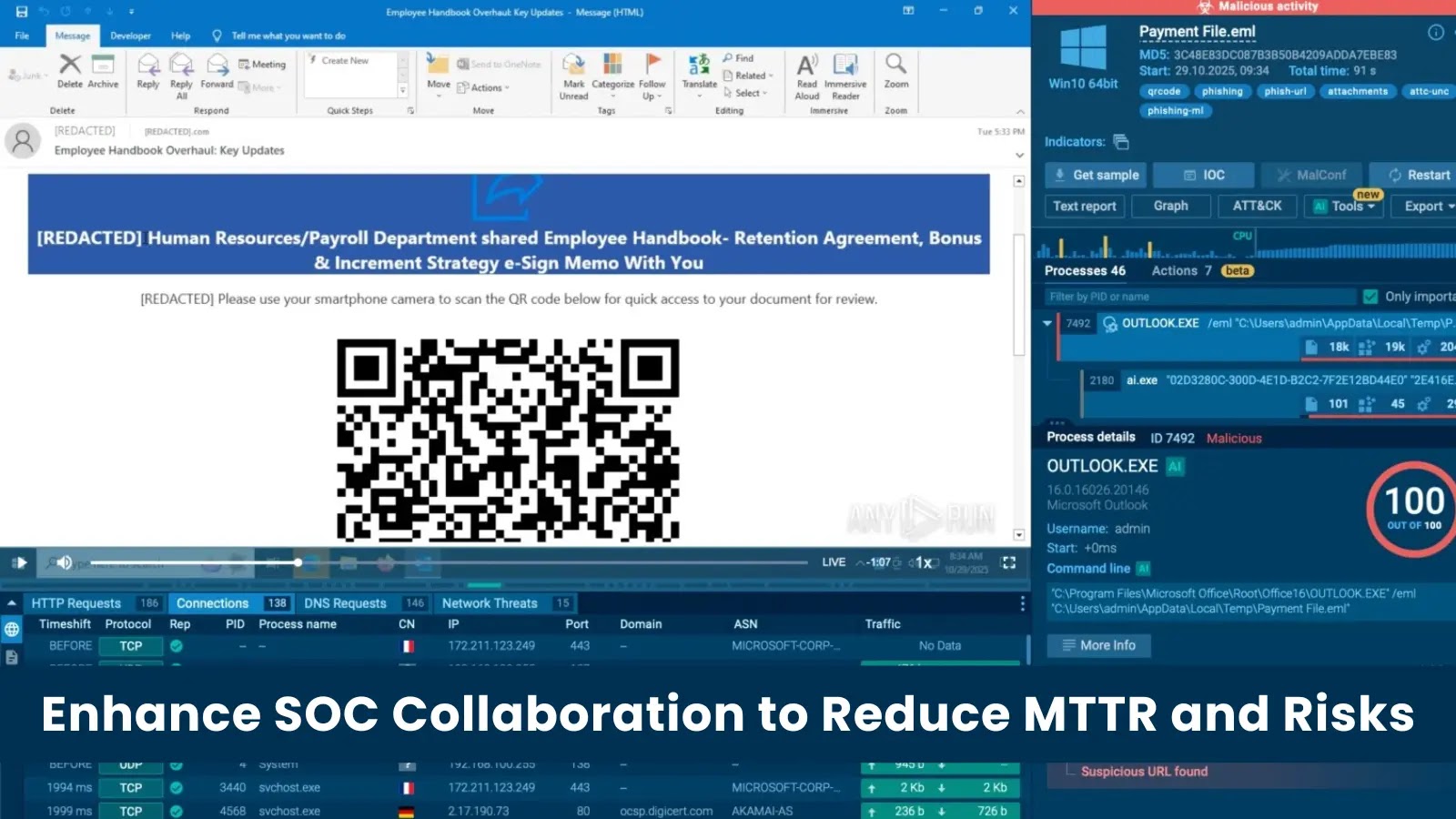
Streamlining SOC Operations: Key to Faster Threat Response and Lower Business Risks
Enhancing SOC Efficiency: The Key to Reducing MTTR and Business Risk In today’s fast-paced digital landscape, Security Operations Centers (SOCs) are under immense pressure to […]
Thousands of Honeywell BMS Controllers Vulnerable Online Due to Unauthenticated Access
Thousands of Honeywell Controllers Exposed Online Without Authentication Recent findings have revealed that thousands of Honeywell building-management controllers are accessible online without requiring authentication. This […]
Stolen Gemini API Key Results in $82,000 Charges for Mexican Team amid Cloud Security Lapses
Stolen Gemini API Key Leads to $82,000 in Unauthorized Charges for Mexican Development Team A small development team in Mexico, consisting of three members, is […]
Urgent Alert: Critical Memory Corruption Flaw in Qualcomm Chipsets Actively Exploited, Affecting Millions of Devices
Critical Memory Corruption Vulnerability in Qualcomm Chipsets Exploited in Active Attacks The Cybersecurity and Infrastructure Security Agency (CISA) has issued an urgent alert regarding a […]
Attackers Use Google Cloud Storage to Evade Email Security, Phish for Financial Data
Cybercriminals Exploit Google Cloud Storage to Bypass Email Security Filters In early March 2026, cybersecurity researchers uncovered a sophisticated phishing campaign that leverages Google Cloud […]
Critical Perplexity Browser Vulnerability Exploited via Google Calendar Invites for Data Theft
Perplexity’s Comet Browser Vulnerability: Exploiting Calendar Invites to Steal Sensitive Data In a recent discovery by Zenity Labs, a critical vulnerability named PerplexedBrowser has been […]
FBI and Global Agencies Dismantle Notorious LeakBase Cybercriminal Forum
Operation Leak: Global Authorities Dismantle LeakBase Cybercriminal Forum In a significant victory against cybercrime, the Federal Bureau of Investigation (FBI), in collaboration with international law […]
Critical Vulnerability in MS-Agent Framework Exposes Systems to Full Control by Attackers
Critical Flaw in MS-Agent Framework Allows Full System Takeover A significant security vulnerability has been identified in the ModelScope MS-Agent framework, a lightweight platform designed […]
Iranian APT ‘Dust Specter’ Launches AI-Enhanced Malware Attack on Iraqi Officials
Iranian APT ‘Dust Specter’ Targets Iraqi Officials with AI-Enhanced Malware In January 2026, a sophisticated cyberattack campaign emerged, targeting Iraqi government officials. The threat actor, […]