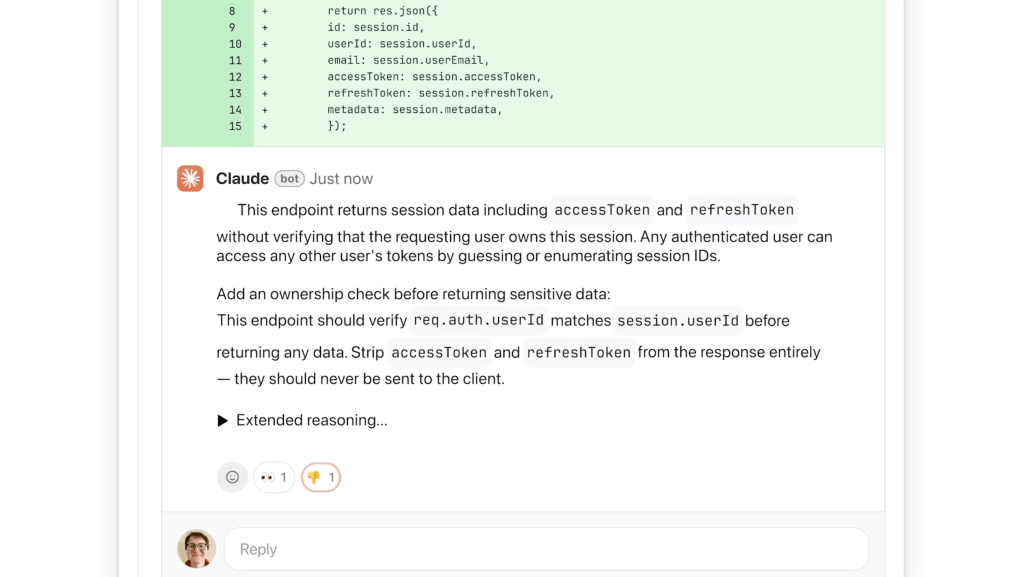
Anthropic Unveils ‘Code Review’ to Tackle AI-Generated Code Challenges In the evolving landscape of software development, peer code reviews have long been essential for identifying […]
Author: The Daily Tech Feed Team
U.S. Military Contractor’s iPhone Hacking Tools Exploited by Russian, Chinese Operatives
U.S. Military Contractor’s iPhone Hacking Tools Misused by Russian Spies In a startling revelation, sophisticated iPhone hacking tools originally developed by U.S. military contractor L3Harris […]
Vietnam-Based Cybercrime Network Fuels Global Fraud with Fake Account Ecosystem
Unveiling Vietnam’s Cybercrime Network: A Global Threat to Online Security A vast cybercrime network operating out of Vietnam has been identified as the driving force […]
Signal Users Face Phishing Attacks Exploiting Human Vulnerabilities for Account Takeovers
Signal Users Targeted in Sophisticated Phishing Attacks Leading to Account Takeovers Signal, the renowned encrypted messaging platform, has recently acknowledged a series of targeted phishing […]
Researchers Unveil ScamAgent: Autonomous AI Framework for Sophisticated Scam Calls
ScamAgent: Unveiling the AI Framework Behind Fully Autonomous Scam Calls In a groundbreaking development, researchers at Rutgers University have introduced ScamAgent, an autonomous AI framework […]
Critical Nginx UI Flaw Lets Attackers Access System Backups Without Authentication
Critical Nginx UI Vulnerability Exposes Full System Backups to Unauthenticated Attackers A critical security vulnerability has been identified in Nginx UI, a widely used web-based […]
CISA Warns of Active Exploitation in Critical macOS and iOS Vulnerabilities, Urges Immediate Patching
CISA Issues Urgent Alert on Actively Exploited macOS and iOS Vulnerabilities The Cybersecurity and Infrastructure Security Agency (CISA) has recently sounded the alarm over multiple […]
Advanced Cyber Threat: VIP Keylogger Uses Steganography for Mass Credential Theft
Stealthy VIP Keylogger Campaign Exploits Steganography for Mass Credential Theft A sophisticated cyberattack leveraging the VIP Keylogger has emerged, posing a significant threat to both […]
M365Pwned Toolkit Enhances Red Team Exploits in Microsoft 365 Environments
In the ever-evolving landscape of cybersecurity, red teamers and penetration testers continually seek advanced tools to simulate real-world attacks and assess organizational defenses. A significant […]
Iranian Cyber Threats Intensify as Seedworm Targets U.S. Infrastructure Amid Escalating Tensions
Iranian Cyber Threats Escalate: U.S. Critical Infrastructure Under Siege In early February 2026, the Iranian advanced persistent threat (APT) group known as Seedworm—also referred to […]