In a recent cybersecurity incident, a malicious npm package named @kodane/patch-manager was discovered to be draining funds from Solana cryptocurrency wallets. This package, generated using artificial intelligence (AI), masqueraded as a utility for license validation and registry optimization in Node.js applications. Before its removal from the npm registry, it had been downloaded over 1,500 times.
The Deceptive Package
Published on July 28, 2025, by a user named Kodane, @kodane/patch-manager claimed to offer advanced features for high-performance Node.js applications. However, embedded within its code was a stealthy wallet drainer designed to siphon funds from Solana wallets. The malicious functionality was activated through a post-installation script, which, upon execution, deployed its payload across various operating systems, including Windows, Linux, and macOS. This script then established a connection to a command-and-control (C2) server at sweeper-monitor-production.up.railway[.]app.
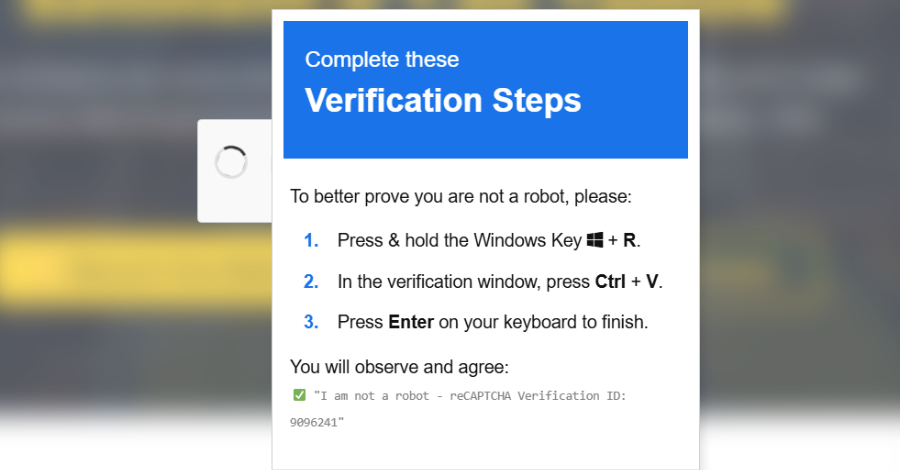
Mechanism of Attack
The post-installation script generated a unique machine identifier for the compromised host and transmitted this information to the C2 server. The malware then scanned the system for Solana wallet files. If such files were detected, the malware proceeded to drain all funds, transferring them to a hard-coded wallet address controlled by the attacker. This method of attack highlights the vulnerabilities associated with post-installation scripts in the npm ecosystem, as they execute automatically after package installation, potentially compromising systems without any manual execution by the user.
AI’s Role in Malware Development
What sets this incident apart is the apparent use of AI in generating the malicious package. Indicators suggest that the package was created using Anthropic’s Claude AI chatbot. Evidence supporting this includes the presence of emojis, extensive JavaScript console logging messages, well-crafted and descriptive comments, and a README.md file consistent with Claude-generated markdown styles. Additionally, the use of the term Enhanced aligns with Claude’s pattern of labeling code changes.
Implications for Software Supply Chain Security
This incident underscores the evolving tactics of threat actors who are leveraging AI to create more convincing and dangerous malware. The use of AI enables the generation of polished, seemingly legitimate packages that can bypass traditional security defenses. This development raises significant concerns for software supply chain security, as AI-generated packages may appear clean or even beneficial, making them more challenging to detect.
Broader Context of Malicious npm Packages
The discovery of @kodane/patch-manager is part of a broader trend of malicious activities targeting the npm ecosystem. For instance, in August 2025, a similar AI-generated malicious npm package was identified, which drained Solana funds from over 1,500 users before its takedown. This package also utilized post-installation scripts to deploy its payload and connect to a C2 server. The malware scanned systems for wallet files and transferred funds to an attacker-controlled address. Notably, this package exhibited characteristics suggesting it was generated using AI, including well-written comments and structured code.
Recommendations for Developers
Given the increasing sophistication of malicious packages, developers are advised to exercise heightened vigilance when incorporating third-party packages into their projects. Best practices include:
– Thoroughly Vet Packages: Before adding any package, review its source code, maintainers, and user feedback.
– Monitor for Suspicious Behavior: Be alert to unexpected post-installation scripts or any unusual network activity following package installation.
– Implement Security Tools: Utilize tools designed to detect and prevent the inclusion of malicious packages in your projects.
– Stay Informed: Keep abreast of the latest security advisories and reports related to the npm ecosystem and other package registries.
Conclusion
The emergence of AI-generated malicious packages like @kodane/patch-manager highlights the need for robust security measures within the software development community. As threat actors continue to refine their methods, leveraging advanced technologies to craft convincing malware, developers must remain vigilant and proactive in safeguarding their projects and users against such sophisticated attacks.