Aeternum C2 Botnet Utilizes Polygon Blockchain for Resilient Command Infrastructure
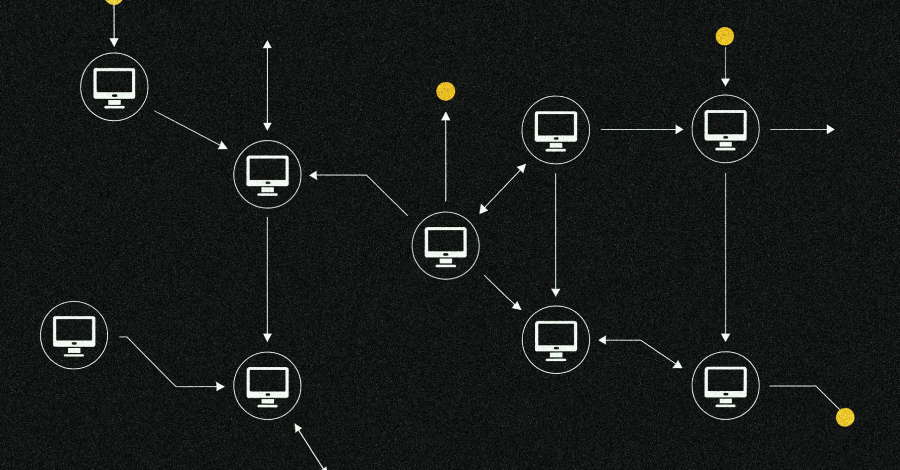
Cybersecurity experts have recently uncovered a sophisticated botnet loader named Aeternum C2, which leverages blockchain technology to establish a command-and-control (C2) infrastructure that is notably resistant to traditional takedown methods. Unlike conventional botnets that depend on centralized servers or domains, Aeternum C2 embeds its operational commands within the public Polygon blockchain. This decentralized approach ensures the botnet’s instructions are virtually immutable and persistently accessible, complicating efforts to disrupt its activities.
The Polygon network, renowned for hosting decentralized applications like Polymarket—the world’s largest prediction market—provides an ideal platform for Aeternum’s operations. By integrating with such a widely used blockchain, the botnet’s C2 infrastructure becomes effectively permanent, evading traditional cybersecurity interventions.
This strategy is not entirely unprecedented. In 2021, Google intervened to disrupt the Glupteba botnet, which utilized the Bitcoin blockchain as a backup C2 mechanism to retrieve its server addresses. However, Aeternum’s implementation signifies a more advanced and resilient use of blockchain technology in cyber threats.
Emergence and Commercialization
Aeternum C2 first surfaced in December 2025 when Outpost24’s KrakenLabs reported that a threat actor known as LenAI was marketing the malware on underground forums. For $200, buyers could access a user-friendly panel and a pre-configured build of the botnet. A more comprehensive package, including the entire C++ codebase and subsequent updates, was offered for $4,000.
The malware, developed in native C++, is available in both 32-bit and 64-bit versions. It operates by writing commands intended for infected hosts into smart contracts on the Polygon blockchain. Compromised devices then query these smart contracts via public remote procedure call (RPC) endpoints to retrieve and execute the commands.
Operational Mechanics
Aeternum’s operations are orchestrated through a web-based control panel, enabling operators to:
– Select specific smart contracts.
– Define command types.
– Specify payload URLs.
– Update commands as needed.
Once a command is embedded into the blockchain as a transaction, it becomes accessible to all infected devices polling the network. Notably, only the wallet holder can alter or remove a confirmed command, enhancing the botnet’s resilience. Operators can manage multiple smart contracts simultaneously, each potentially delivering different payloads or functions, such as clippers, stealers, remote access trojans (RATs), or cryptocurrency miners.
Research by Ctrl Alt Intel reveals that the C2 panel is implemented as a Next.js web application. This platform allows operators to deploy smart contracts on the Polygon blockchain. These contracts contain functions that, when invoked by the malware via Polygon RPC, return encrypted commands. The malware then decrypts and executes these commands on the victim’s machine.
Evasion and Anti-Analysis Features
To prolong the lifespan of infections and evade detection, Aeternum incorporates several anti-analysis mechanisms:
– Virtual Environment Detection: The malware checks for virtualized environments, which are commonly used by researchers for analysis, and can alter its behavior or terminate execution if such environments are detected.
– Antivirus Evasion: Operators can utilize services like Kleenscan to scan their builds, ensuring they are not flagged by antivirus software before deployment.
The operational costs associated with Aeternum are minimal. Approximately $1 worth of MATIC, Polygon’s native token, suffices for 100 to 150 command transactions. This cost-effectiveness eliminates the need for operators to rent servers, register domains, or maintain extensive infrastructure beyond a cryptocurrency wallet and a local copy of the control panel.
Current Status and Implications
The threat actor behind Aeternum, LenAI, has recently attempted to sell the entire toolkit for $10,000, citing a lack of time for support and involvement in other projects. This sale includes full rights for resale and commercial use, along with development notes and tips.
LenAI is also associated with another cybercrime tool named ErrTraffic. This tool automates ClickFix attacks by generating fake glitches on compromised websites, creating a false sense of urgency to deceive users into following malicious instructions.
The emergence of Aeternum C2 underscores a significant evolution in cybercriminal tactics, particularly the exploitation of blockchain technology to create resilient and decentralized command infrastructures. This development poses substantial challenges for cybersecurity professionals, as traditional takedown methods become less effective against such decentralized systems.
As cyber threats continue to evolve, it is imperative for cybersecurity strategies to adapt accordingly. Understanding and mitigating threats like Aeternum C2 require a comprehensive approach that considers the unique challenges posed by blockchain-based infrastructures.