ODINI Malware: Breaching Air-Gapped Systems via CPU Magnetic Emissions
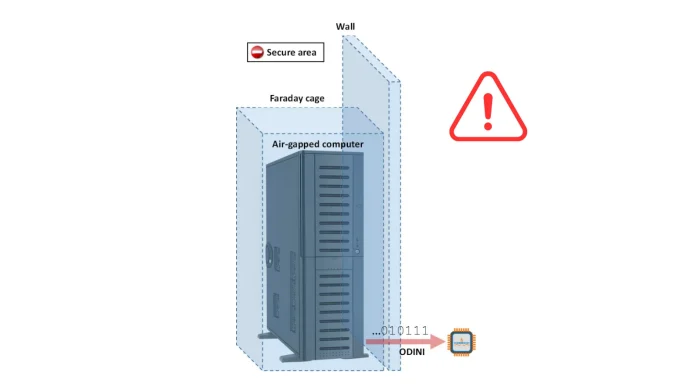
In a groundbreaking development, cybersecurity researchers have unveiled ODINI, a proof-of-concept malware capable of extracting sensitive data from air-gapped computers protected by Faraday cages. This discovery challenges the long-held belief that such systems are impervious to external threats.
Understanding Air-Gapped Systems and Faraday Cages
Air-gapped systems are computers or networks that are physically isolated from unsecured networks, including the internet. This isolation is a security measure designed to prevent unauthorized access and data breaches. Faraday cages, on the other hand, are enclosures made of conductive materials that block electromagnetic fields, providing an additional layer of protection against electromagnetic interference and potential cyber threats.
The Emergence of ODINI Malware
Developed by a team led by Mordechai Guri at Israel’s Ben-Gurion University, ODINI exploits the very components designed to protect sensitive information. By manipulating a computer’s central processing unit (CPU) to generate low-frequency magnetic fields, ODINI creates a covert channel to transmit data, effectively bypassing the physical barriers of air-gapped systems and Faraday cages.
Mechanism of Data Exfiltration
ODINI operates by overloading the CPU cores with specific calculations, leading to dynamic fluctuations in power consumption. These fluctuations generate low-frequency magnetic fields that can penetrate standard computer chassis and the metal shielding of Faraday cages. The malware employs advanced data modulation techniques, such as amplitude-shift keying and frequency-shift keying, to encode stolen information onto these magnetic waves.
To receive the transmitted data, an attacker must place a magnetic sensor within 100 to 150 centimeters of the compromised machine. This setup allows for a data transfer rate of up to 40 bits per second. A variant of this attack, known as MAGNETO, utilizes an infected smartphone’s built-in magnetometer as the receiver. MAGNETO is effective at distances up to 12.5 centimeters and can transfer data at 5 bits per second, even if the smartphone is inside a Faraday bag or in airplane mode.
Implications for Security
The advent of ODINI underscores the evolving nature of cyber threats and the need for continuous innovation in security measures. Traditional defenses, such as air gaps and Faraday cages, are no longer sufficient to thwart determined adversaries. Organizations, especially those in the military, financial, and critical infrastructure sectors, must reassess their security protocols to address these emerging vulnerabilities.
Potential Countermeasures
Defending against magnetic field exfiltration presents significant challenges. Conventional Faraday cages are ineffective against low-frequency transmissions. Implementing physical shields made from specialized ferromagnetic materials like mu-metal is often prohibitively expensive and impractical. Security professionals recommend hardware-based signal jamming, which uses commercial magnetic field generators to produce counter-magnetic noise, effectively drowning out covert transmissions.
Broader Context of Air-Gap Breaches
ODINI is not the first instance of malware targeting air-gapped systems. Previous research has demonstrated various methods to exfiltrate data from such systems, including:
– RAMBO (Radiation of Air-gapped Memory Bus for Offense): Exploits electromagnetic emissions from a computer’s RAM to leak data.
– AIR-FI: Leverages electromagnetic emissions from DDR SDRAM memory buses to generate Wi-Fi signals that nearby devices can pick up.
– POWER-SUPPLaY: Utilizes acoustic noise generated by computer power supplies to encode data in inaudible sounds, which can be captured by nearby microphones.
– LED-it-GO: Employs the hard drive activity LED to rapidly flicker in patterns that encode binary data, which can be recorded by a camera and later decoded.
– BitWhisper: Uses temperature changes induced by CPU operations to transmit data between adjacent air-gapped systems.
– GAIROSCOPE: Utilizes a smartphone’s gyroscope to receive vibrations from a compromised computer, detecting subtle oscillations caused by the PC’s fans and hard drive.
– LANTENNA: Leverages Ethernet cables as antennas to broadcast radio signals by toggling the cable’s transmission lines, generating electromagnetic emissions detectable several meters away.
Conclusion
The emergence of ODINI malware highlights the need for a paradigm shift in cybersecurity strategies. As attackers develop increasingly sophisticated methods to breach even the most secure systems, organizations must adopt a multi-layered defense approach. This includes not only physical and network security measures but also continuous monitoring, anomaly detection, and employee training to recognize and mitigate potential threats.