Cybercriminals Exploit Google Ads to Hijack ManageWP Credentials
In a sophisticated cyberattack campaign dubbed WrongPress, hackers are leveraging fraudulent Google Ads to steal login credentials from users of ManageWP, a popular platform owned by GoDaddy that allows centralized management of multiple WordPress websites. This campaign underscores the growing trend of cybercriminals exploiting trusted advertising platforms to execute phishing schemes.
The Mechanics of the Attack
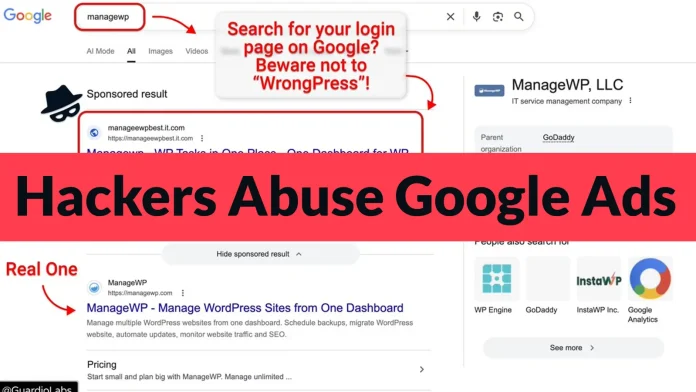
The attack initiates when a user searches for ManageWP on Google. A malicious sponsored advertisement appears prominently above the legitimate search result, enticing users to click on it. This deceptive placement increases the likelihood of users inadvertently accessing the fraudulent site.
Upon clicking the malicious ad, users are redirected to a counterfeit ManageWP login page that is meticulously designed to mirror the authentic site. This high level of replication makes it challenging for users to discern the fraud. When users enter their login credentials, the information is immediately transmitted to the attackers, who can then gain unauthorized access to the users’ ManageWP accounts.
The Significance of ManageWP Accounts
ManageWP is extensively utilized by web developers, digital agencies, and enterprises to oversee numerous WordPress websites from a single dashboard. A single set of credentials can provide control over a vast array of websites, making these accounts highly attractive targets for cybercriminals. According to WordPress.org, the ManageWP Worker plugin is active on over one million websites, highlighting the potential scale of impact from such breaches.
Detection and Response
Researchers at Guardio Labs were the first to identify and report this campaign. They observed that the malicious ads were strategically placed to appear above the legitimate ManageWP search result, increasing the likelihood of user engagement. Guardio Labs has been actively reaching out to alert affected users and has infiltrated the attackers’ command-and-control infrastructure to better understand the operation’s scale and mechanics.
Technical Aspects of the Attack
The attackers employ several sophisticated techniques to evade detection and enhance the effectiveness of their campaign:
1. Cloaking Mechanisms: Before redirecting users to the fake login page, the attackers use cloaking tools to filter out automated bots and security scanners. This ensures that only genuine users are targeted, reducing the chances of the malicious ad being flagged and removed.
2. Adversary-in-the-Middle (AiTM) Techniques: Once on the counterfeit login page, the attackers’ server acts as an intermediary, capturing the entered credentials in real-time. This allows them to bypass security measures such as two-factor authentication (2FA) by prompting users for their 2FA codes and using them immediately to access the real ManageWP accounts.
3. Command-and-Control Infrastructure: The operation is managed through a centralized server that provides the attackers with a live dashboard to monitor and control ongoing phishing sessions. This infrastructure enables real-time data collection and account exploitation.
Broader Implications and Similar Campaigns
The WrongPress campaign is part of a larger trend where cybercriminals exploit trusted platforms like Google Ads to execute phishing attacks. Similar tactics have been observed in other campaigns:
– Malvertising Campaigns Targeting Graphic Design Professionals: In December 2024, researchers identified malvertising campaigns using Google Search ads to target graphic design professionals. These campaigns directed users to malicious downloads, posing significant risks to both corporate environments and individual security. ([cybersecuritynews.com](https://cybersecuritynews.com/hackers-exploiting-google-search-ads/?utm_source=openai))
– Exploitation of Google Ads Tracking Features: In April 2024, hackers exploited Google Ads tracking features to deliver malware, highlighting the vulnerabilities within advertising platforms that can be leveraged for malicious purposes. ([cybersecuritynews.com](https://cybersecuritynews.com/google-adstracking-malware/?utm_source=openai))
– Distribution of Fakebat Malware via Google Ads: In November 2024, the Fakebat malware loader resurfaced, being distributed through malicious Google Ads that impersonated popular productivity software, leading users to download trojanized versions of the software. ([cybersecuritynews.com](https://cybersecuritynews.com/fakebat-malware-via-google-ads/?utm_source=openai))
Preventive Measures and Recommendations
To mitigate the risks associated with such phishing campaigns, users and organizations are advised to adopt the following measures:
1. Vigilance with Sponsored Ads: Exercise caution when clicking on sponsored search results. Verify the authenticity of the URL and ensure it matches the official domain of the service.
2. Direct Navigation: Whenever possible, navigate directly to the official website by typing the URL into the browser’s address bar, rather than relying on search engine results.
3. Enhanced Security Protocols: Implement multi-factor authentication (MFA) and monitor account activities for any unauthorized access attempts.
4. Regular Security Training: Educate employees and users about the latest phishing tactics and the importance of scrutinizing emails and links before interacting with them.
5. Utilize Security Tools: Deploy advanced security solutions that can detect and block malicious ads and phishing attempts.
Conclusion
The WrongPress campaign serves as a stark reminder of the evolving tactics employed by cybercriminals to exploit trusted platforms for malicious purposes. By understanding these methods and implementing robust security measures, users and organizations can better protect themselves against such sophisticated phishing attacks.