MuddyWater Exploits Microsoft Teams in Sophisticated Credential Theft Scheme
In early 2026, cybersecurity experts uncovered a deceptive operation by the Iranian state-sponsored hacking group MuddyWater, also known as Mango Sandstorm, Seedworm, and Static Kitten. This campaign cleverly disguised itself as a ransomware attack under the Chaos brand, utilizing Microsoft Teams to infiltrate organizations and steal sensitive credentials.
Deceptive Tactics and Social Engineering
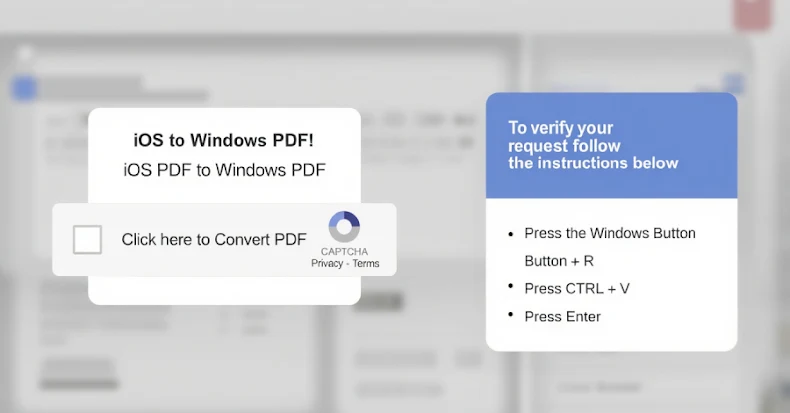
MuddyWater’s operation began with a high-touch social engineering phase conducted via Microsoft Teams. Attackers initiated interactive screen-sharing sessions, posing as IT support personnel to gain the trust of their targets. During these sessions, they harvested login credentials and manipulated multi-factor authentication (MFA) processes to gain unauthorized access to systems. This method allowed them to bypass traditional security measures effectively.
Beyond Traditional Ransomware
Unlike typical ransomware attacks that encrypt files to demand a ransom, MuddyWater’s approach focused on data exfiltration and establishing long-term access. They employed remote management tools like DWAgent to maintain persistence within the compromised networks. This strategy indicates a shift towards espionage and prolonged surveillance rather than immediate financial gain.
False Flag Operations and Attribution Challenges
By masquerading as the Chaos ransomware group, MuddyWater aimed to obscure its true identity and intentions. This tactic complicates attribution efforts and delays defensive responses. The use of off-the-shelf tools and existing cybercriminal infrastructure further blurs the lines between state-sponsored activities and conventional cybercrime.
Historical Context and Evolving Strategies
MuddyWater has a history of employing deceptive tactics. In September 2020, they targeted Israeli organizations with a loader called PowGoop, deploying a variant of Thanos ransomware with destructive capabilities. In 2023, they collaborated with DEV-1084, known for using the DarkBit persona, to conduct destructive attacks under the guise of ransomware. By October 2025, they were linked to attacks on Israeli government hospitals using Qilin ransomware.
Implications for Cybersecurity
The blending of state-sponsored motives with cybercriminal methods presents significant challenges for cybersecurity professionals. Organizations must remain vigilant against sophisticated social engineering tactics and ensure robust security protocols are in place. Regular training, advanced threat detection systems, and a culture of security awareness are essential to defend against such multifaceted threats.