Critical Vulnerability in MetInfo CMS Exploited for Remote Code Execution
A critical security vulnerability, identified as CVE-2026-29014 with a CVSS score of 9.8, has been discovered in MetInfo CMS, an open-source content management system. This flaw allows unauthenticated remote attackers to execute arbitrary PHP code by sending specially crafted requests, potentially leading to full control over affected servers.
The vulnerability affects MetInfo CMS versions 7.9, 8.0, and 8.1. According to the National Institute of Standards and Technology (NIST) National Vulnerability Database, the issue arises from insufficient input neutralization in the execution path, enabling attackers to inject malicious PHP code.
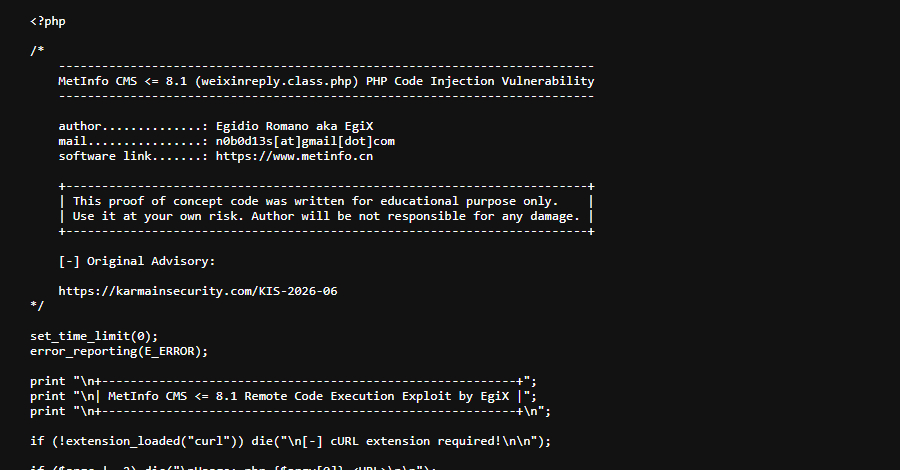
Security researcher Egidio Romano pinpointed the root cause to the /app/system/weixin/include/class/weixinreply.class.php script. The flaw stems from inadequate sanitization of user-supplied input when processing Weixin (WeChat) API requests. This oversight allows remote, unauthenticated attackers to inject and execute arbitrary PHP code.
For successful exploitation on non-Windows servers, the /cache/weixin/ directory must exist. This directory is typically created during the installation and configuration of the official WeChat plugin.
MetInfo released patches addressing CVE-2026-29014 on April 7, 2026. Despite this, active exploitation began on April 25, with initial attacks targeting honeypots in the U.S. and Singapore. These early attempts were limited and appeared to be automated probes.
However, on May 1, 2026, there was a significant increase in exploitation activity, particularly targeting IP addresses in China and Hong Kong. Caitlin Condon, Vice President of Security Research at VulnCheck, noted that approximately 2,000 instances of MetInfo CMS are accessible online, with the majority located in China.