Enhancing SOC Efficiency: Leveraging High-Quality Threat Intelligence to Reduce Costs
In the ever-evolving landscape of cybersecurity, Security Operations Centers (SOCs) are under constant pressure to detect and respond to threats swiftly and effectively. However, many SOCs grapple with challenges such as alert fatigue, high operational costs, and inefficient triage processes. A pivotal solution to these issues lies in integrating high-quality threat intelligence that is relevant, actionable, and curated to minimize false positives.
The Impact of Low-Quality Threat Data on SOC Operations
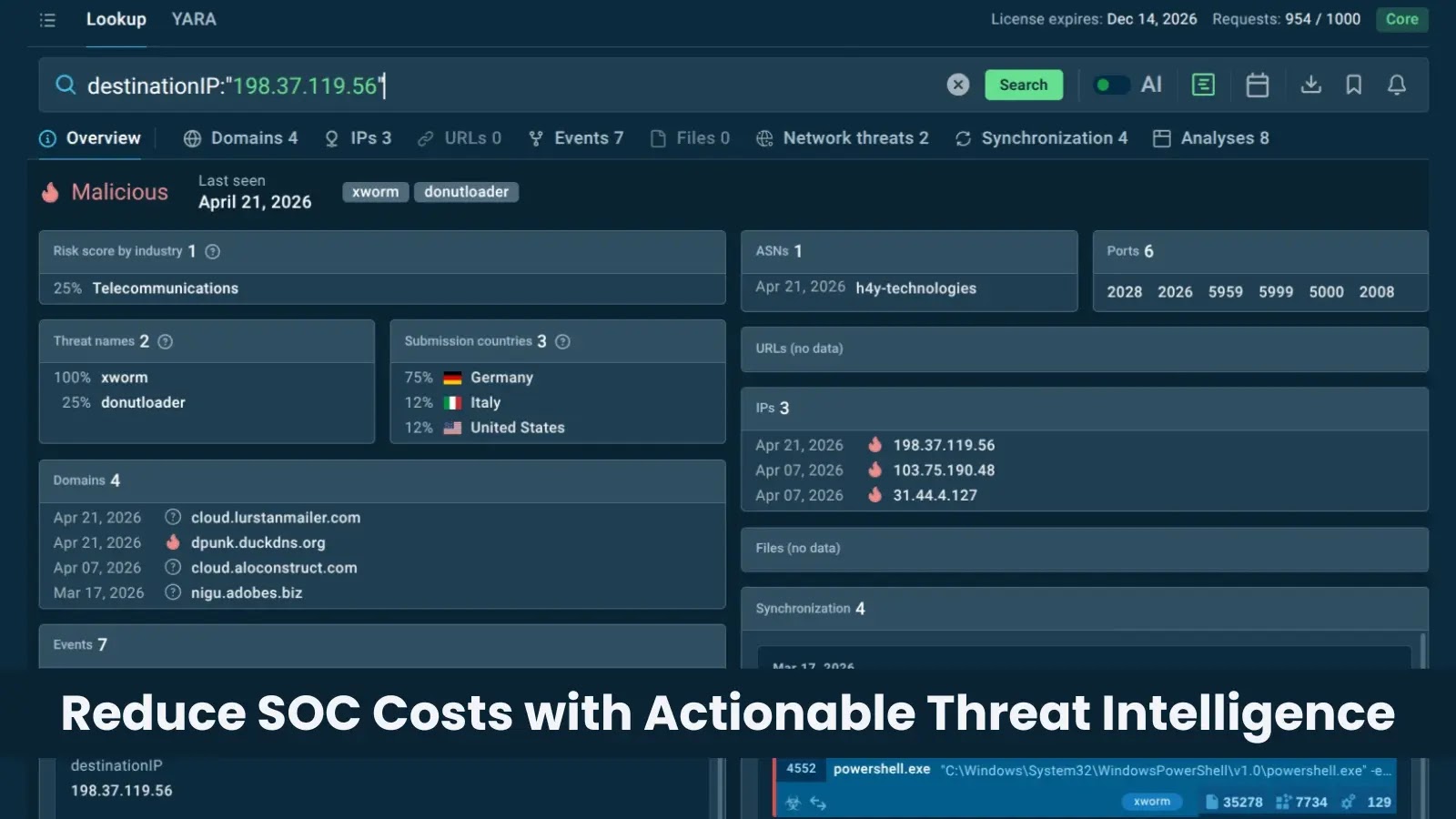
Inefficient triage processes often stem from the reliance on threat data that lacks context and validation. When analysts are inundated with ambiguous or irrelevant alerts, they face the dilemma of balancing speed with accuracy. This scenario leads to wasted time on false alarms and an increased risk of overlooking genuine threats. The root cause is not merely operational inefficiencies but the influx of low-quality threat data that clutters detection systems. To address this, it’s essential to reduce noise at the source by ensuring that threat intelligence is derived from real-world attack behaviors and validated before integration into detection pipelines.
Operational Benefits of High-Quality Threat Intelligence Feeds
Integrating high-quality Threat Intelligence Feeds into SOC workflows offers several advantages:
– Unique Indicators: Access to a vast array of unique indicators structured for rapid retrieval enhances detection capabilities.
– Reduced False Positives: A near-zero false positive rate alleviates alert fatigue, allowing analysts to focus on genuine threats.
– Behavioral Context: Embedded behavioral insights expedite investigations by providing context to alerts.
– Seamless Integration: Compatibility with existing SIEM, SOAR, and EDR systems ensures smooth incorporation into current workflows.
By leveraging threat intelligence derived from extensive investigations conducted by numerous SOC teams and security professionals, organizations can achieve more consistent outcomes, prioritize incidents effectively, and refine automated response playbooks.
Enhancing Alert Enrichment with Relevant Threat Context
Beyond initial alert processing, investigations often stall during the enrichment phase due to tool sprawl, isolated indicators, and a lack of context. These factors hinder analysts’ ability to fully comprehend threats and respond confidently. To overcome these challenges, it’s crucial to integrate threat intelligence that provides relevant context, enabling analysts to make informed decisions and streamline the investigation process.
Conclusion
Optimizing SOC costs and enhancing operational efficiency require a strategic approach to threat intelligence. By integrating high-quality, context-rich threat intelligence feeds, SOCs can reduce noise, improve detection accuracy, and respond to threats more effectively. This proactive stance not only mitigates risks but also ensures that security teams can operate with greater confidence and precision in the face of evolving cyber threats.