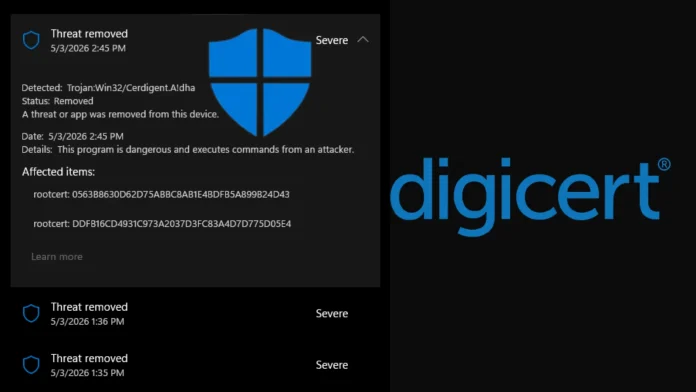
Microsoft Defender’s False Positive Flags DigiCert Root Certificates as Malware
In early May 2026, Microsoft Defender, the built-in antivirus solution for Windows, mistakenly identified two legitimate DigiCert root certificates as malicious software. This error, stemming from a faulty security update, led to widespread disruptions in SSL/TLS validation and code-signing processes across numerous enterprise environments.
The issue originated from an antimalware signature update released around April 30, 2026. This update introduced a detection labeled Trojan:Win32/Cerdigent.A!dha, which incorrectly flagged registry entries associated with two widely trusted root certificates:
– DigiCert Assured ID Root CA: Thumbprint 0563B8630D62D75ABBC8AB1E4BDFB5A899B24D43
– DigiCert Trusted Root G4: Thumbprint DDFB16CD4931C973A2037D3FC83A4D7D775D05E4
These certificates are essential components of the Windows trust store, located under the registry path `HKLM\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates`. They play a critical role in validating SSL/TLS connections and verifying the authenticity of code-signed software.
Upon detecting these certificates as threats, Microsoft Defender automatically quarantined the associated registry entries. This action effectively removed the certificates from the Windows trust store, leading to potential failures in SSL/TLS connections and code-signing verifications. Such disruptions could manifest as browser warnings, application errors, and service outages, particularly affecting organizations that rely on DigiCert-signed software or secure HTTPS endpoints.
The cybersecurity community quickly took notice of the issue. Florian Roth, a well-known security researcher, highlighted the problem on social media, urging administrators to investigate. He provided an Advanced Hunting query to help identify affected devices:
“`
text| where ActionType == RegistryKeyCreated
| where Timestamp > datetime(2026-05-03T04:00:00)
| project Timestamp, DeviceName, ActionType, InitiatingProcessFileName
| order by Timestamp desc
“`
Additionally, Roth recommended using the command `certutil -store AuthRoot | findstr -i digicert` to check for the presence of the DigiCert certificates on systems.
Microsoft promptly acknowledged the issue and released corrective definition updates, notably version .430, which aimed to restore the quarantined certificates on affected machines. Reports indicated that the restoration process was being deployed automatically across managed endpoints, suggesting that Microsoft implemented a silent remediation alongside the updated signature.
For administrators in environments with restricted update policies, it was advised to manually verify the presence of the DigiCert certificates using the `certutil` command and to consult the Advanced Hunting logs in Microsoft Defender for Endpoint to confirm successful restoration.
This incident underscores the challenges associated with automated threat detection and remediation. While such systems are designed to proactively protect against malware, false positives can lead to significant operational disruptions. It highlights the importance of rigorous testing and validation of security updates before deployment, as well as the need for swift response mechanisms to address and rectify errors when they occur.
In the broader context, this event is not isolated. Similar incidents have occurred in the past, where security tools have mistakenly flagged legitimate software components as malicious. For instance, in October 2025, Microsoft Defender for Endpoint incorrectly flagged specific versions of SQL Server as having reached their end-of-life, causing confusion among system administrators. Such occurrences emphasize the delicate balance between aggressive threat detection and the risk of false positives.
Organizations are encouraged to maintain robust monitoring and incident response strategies to quickly identify and mitigate the impact of such false positives. Regular communication with software vendors and staying informed about known issues can also aid in minimizing disruptions caused by similar incidents in the future.