Mastering Autonomous Exposure Validation to Counter AI-Driven Cyber Threats
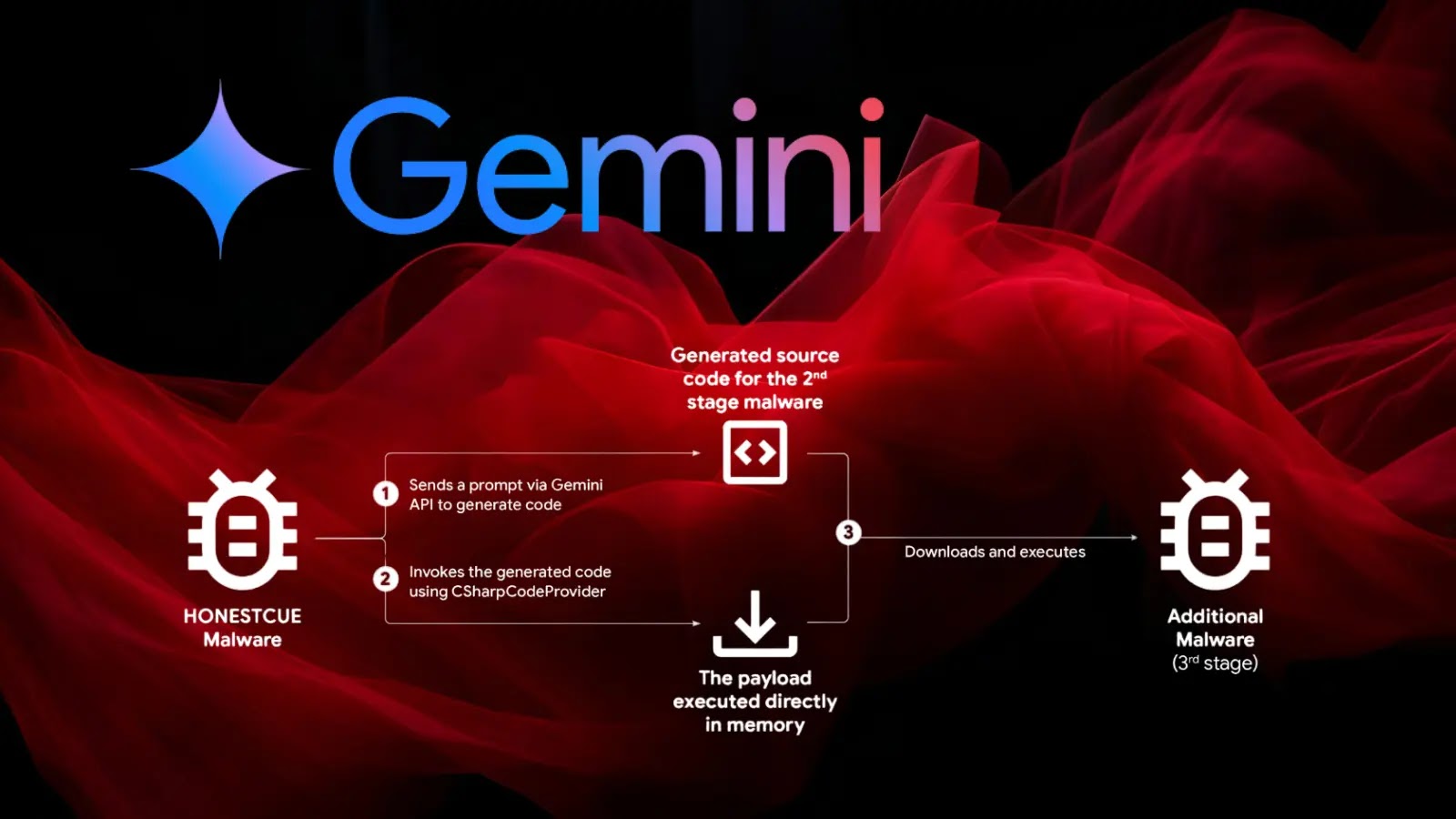
In February 2026, cybersecurity researchers identified a significant shift in cyberattack methodologies: adversaries are now leveraging custom artificial intelligence (AI) systems to automate attacks within the kill chain. This evolution transcends the realm of AI-generated phishing emails, introducing autonomous agents capable of mapping Active Directory structures and obtaining Domain Admin credentials within minutes.
Traditional defensive workflows are ill-equipped to counter such rapid advancements. Typically, a Cyber Threat Intelligence (CTI) team identifies a threat, relays it to the Red Team for testing, and eventually, the Blue Team implements patches. This sequential process is plagued by friction, silos, and delays, rendering it ineffective against AI-driven adversaries operating at machine speed.
To address this critical gap, The Hacker News is hosting a technical deep dive in collaboration with Picus Security, introducing a new defensive paradigm: Autonomous Exposure Validation.
Webinar Details:
– Title: How to Automate Exposure Validation to Match the Speed of AI Attacks
– Date: [Insert Date]
– Time: [Insert Time]
– Registration Link: [Insert Registration Link]
Presenters:
– Kevin Cole: Vice President of Product Marketing at Picus Security
– Gursel Arici: Senior Director of Solution Architecture at Picus Security
Together, they bring a unique blend of strategic threat intelligence and deep technical engineering to demonstrate how to transform defensive strategies.
Key Takeaways:
1. Understanding Speed Asymmetry: Gain insights into the mechanics of autonomous, AI-driven attacks and their operational dynamics.
2. Agent Architecture: Learn how to safely automate threat intelligence ingestion, simulate attacks, and coordinate fixes without disrupting your network.
3. Breaking Down Silos: Discover methods to eliminate slow hand-offs between CTI, Red, and Blue teams, fostering unified operations.
4. Achieving the Team Multiplier Effect: Explore strategies for lean security teams to attain enterprise-level protection without increasing headcount.
As attackers enhance their toolkits with AI capabilities, it is imperative for defenders to evolve correspondingly. This webinar offers invaluable insights for cybersecurity professionals aiming to stay ahead in this rapidly changing landscape.
Registration Information:
Secure your spot today by registering at [Insert Registration Link]. Even if you cannot attend the live session, registering ensures you receive the full recording, so you don’t miss out on these critical insights.