China-Linked GopherWhisper Targets Mongolian Government with Advanced Go-Based Malware
A previously unidentified China-aligned advanced persistent threat (APT) group, dubbed GopherWhisper, has been implicated in a series of cyberattacks targeting Mongolian governmental institutions. This group employs a sophisticated suite of tools, predominantly developed in the Go programming language, to infiltrate systems and deploy various backdoors.
According to a report by Slovakian cybersecurity firm ESET, GopherWhisper utilizes injectors and loaders to execute its malware arsenal. Notably, the group exploits legitimate services such as Discord, Slack, Microsoft 365 Outlook, and file.io for command-and-control (C&C) communications and data exfiltration.
Discovery and Activity Timeline
GopherWhisper first came to light in January 2025 following the detection of a novel backdoor, named LaxGopher, on a system belonging to a Mongolian government entity. Further analysis suggests that the group’s activities date back to at least November 2023.
Malware Arsenal and Techniques
The group’s toolkit includes several Golang-based malware families designed to receive instructions from C&C servers, execute commands, and relay results. Key components of their arsenal are:
– LaxGopher: A Go-based backdoor that leverages Slack channels for C&C operations, enabling command execution via cmd.exe and facilitating the download of additional malware.
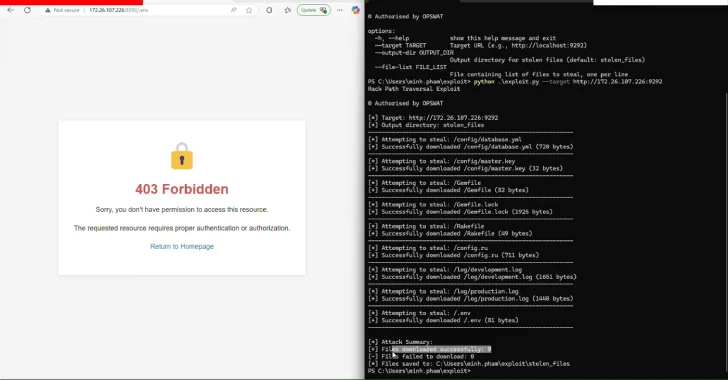
– CompactGopher: A file collection utility that filters files by specific extensions (.doc, .docx, .jpg, .xls, .xlsx, .txt, .pdf, .ppt, and .pptx), compresses them into encrypted ZIP archives using AES-CFB-128, and uploads them to file.io.
– RatGopher: Another Go-based backdoor that uses private Discord servers for C&C communications, allowing for command execution and file transfers via file.io.
– SSLORDoor: A C++-based backdoor utilizing OpenSSL BIO for communication over raw sockets on port 443, capable of drive enumeration, file operations, and command execution through cmd.exe.
– FriendDelivery and BoxOfFriends: A malicious DLL (FriendDelivery) that acts as a loader and injector for BoxOfFriends, a Go-based backdoor using the Microsoft Graph API to create draft emails for C&C purposes with hard-coded credentials.
Infection Scope and Methodology
ESET’s telemetry indicates that approximately 12 systems associated with Mongolian governmental institutions were compromised by these backdoors. C&C traffic analysis from attacker-controlled Discord and Slack servers suggests the existence of numerous other victims.
The exact methods GopherWhisper employs to gain initial access to target networks remain unclear. However, once a foothold is established, the group deploys a range of tools and implants, including:
– JabGopher: An injector that executes the LaxGopher backdoor.
– LaxGopher: As described above, a Go-based backdoor using Slack for C&C.
– CompactGopher: A file collection utility for exfiltrating specific file types.
– RatGopher: A Go-based backdoor utilizing Discord for C&C.
– SSLORDoor: A C++-based backdoor for remote control over compromised hosts.
– FriendDelivery and BoxOfFriends: A loader and injector pair facilitating C&C via Microsoft 365 Outlook draft emails.
Operational Insights
Analysis of Slack and Discord message timestamps reveals that the majority of communications occur during working hours, specifically between 8 a.m. and 5 p.m., aligning with China Standard Time. Additionally, the locale settings in Slack metadata correspond to this time zone, leading researchers to attribute GopherWhisper’s activities to a China-aligned group.
Implications and Recommendations
The emergence of GopherWhisper underscores the evolving landscape of cyber threats, particularly those targeting governmental institutions. The group’s use of legitimate services for C&C communications highlights the need for organizations to monitor and secure these platforms diligently.
To mitigate such threats, it is recommended that organizations:
1. Enhance Monitoring: Implement comprehensive monitoring of network traffic, especially concerning communications with external services like Discord, Slack, and file-sharing platforms.
2. Regularly Update Systems: Ensure all systems and software are up-to-date with the latest security patches to prevent exploitation of known vulnerabilities.
3. Conduct Security Training: Educate employees about phishing tactics and the importance of verifying the authenticity of communications and software sources.
4. Implement Access Controls: Restrict access to critical systems and data based on the principle of least privilege, minimizing potential entry points for attackers.
5. Develop Incident Response Plans: Establish and regularly update incident response protocols to swiftly address and mitigate breaches.
By adopting these measures, organizations can bolster their defenses against sophisticated APT groups like GopherWhisper and safeguard sensitive information from unauthorized access and exfiltration.