Critical Dgraph Database Vulnerability Exposes Systems to Unauthenticated Attacks
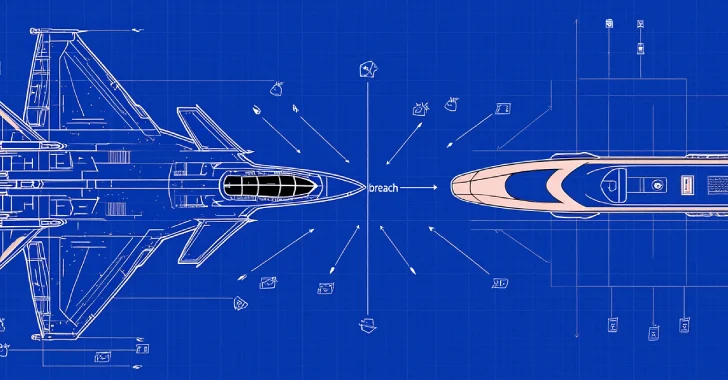
A critical security flaw has been identified in Dgraph, a widely used open-source graph database, posing significant risks to organizations worldwide. Designated as CVE-2026-34976, this vulnerability has been assigned a perfect CVSS score of 10.0, indicating its maximum severity. The flaw enables unauthenticated remote attackers to bypass all security controls, allowing them to overwrite entire databases, access sensitive server files, and execute Server-Side Request Forgery (SSRF) attacks.
Discovery and Impact
Security researchers Matthew McNeely and Koda Reef uncovered this vulnerability, highlighting the substantial threat it poses to organizations that expose their Dgraph administration endpoints to the internet. The flaw resides in Dgraph’s GraphQL administration API, where an administrative command called `restoreTenant` was inadvertently omitted from the security middleware configuration. This omission means that when the system processes a `restoreTenant` request, it bypasses all authentication checks, allowing any external user to restore a database from a backup URL without proper authorization.
Potential Exploits
Attackers can exploit this vulnerability in several ways:
1. Complete Database Overwrite: By hosting a crafted database backup on a public cloud storage service, such as Amazon S3, an attacker can send a request to the Dgraph server, compelling it to fetch the malicious backup and overwrite the target database, thereby destroying all existing data.
2. Local Filesystem Probing: Attackers can input local file paths using the `file://` scheme, enabling them to scan the server’s internal directories and read sensitive files, including password hashes and Kubernetes security tokens.
3. Server-Side Request Forgery (SSRF): By tricking the database into making outbound HTTP requests to internal, private networks or cloud metadata endpoints, attackers can expose internal services that are typically protected behind a firewall.
Affected Versions and Mitigation
This vulnerability affects Dgraph versions 25.3.0 and earlier. The impact is severe, leading to a total loss of data confidentiality, integrity, and availability. Given that the exploit requires no user interaction or credentials, it is highly exploitable. At the time of disclosure, an official patched version of Dgraph had not been released. However, the software fix is straightforward; developers need to add the `restoreTenant` mutation to the existing administrative middleware list.
Until an official patch is available, network administrators are urged to take immediate defensive actions. Organizations should strictly isolate their Dgraph administration ports (typically port 8080) from the public internet and restrict access to trusted internal IP addresses only. Monitoring updates on Dgraph’s official GitHub repository is also recommended to stay informed about the release of security patches.
Broader Implications
This vulnerability underscores the critical importance of comprehensive security configurations in database management systems. Similar vulnerabilities have been identified in other database systems, highlighting a recurring issue in the industry. For instance, a critical SQL injection vulnerability in Microsoft Configuration Manager (SCCM), tracked as CVE-2024-43468, allows unauthenticated attackers to execute malicious commands on servers and databases. This flaw was added to CISA’s Known Exploited Vulnerabilities (KEV) catalog, emphasizing the need for prompt patching and mitigation strategies.
In another case, a severe remote code execution (RCE) flaw was discovered in pgAdmin4, an open-source interface for PostgreSQL databases. Known as CVE-2025-12762, this vulnerability affects versions up to 9.9 and could allow attackers to run arbitrary commands on the hosting server, potentially compromising entire database infrastructures.
These examples highlight the necessity for organizations to maintain vigilant security practices, including regular software updates, thorough security audits, and the implementation of robust access controls.
Conclusion
The discovery of CVE-2026-34976 in Dgraph serves as a stark reminder of the potential risks associated with misconfigurations and overlooked security measures in database systems. Organizations utilizing Dgraph are strongly advised to implement the recommended mitigations immediately and monitor official channels for updates on security patches. By proactively addressing such vulnerabilities, organizations can safeguard their data assets and maintain the integrity of their database systems.