GlassWorm Malware Exploits Solana Blockchain to Deploy RAT and Exfiltrate Sensitive Data
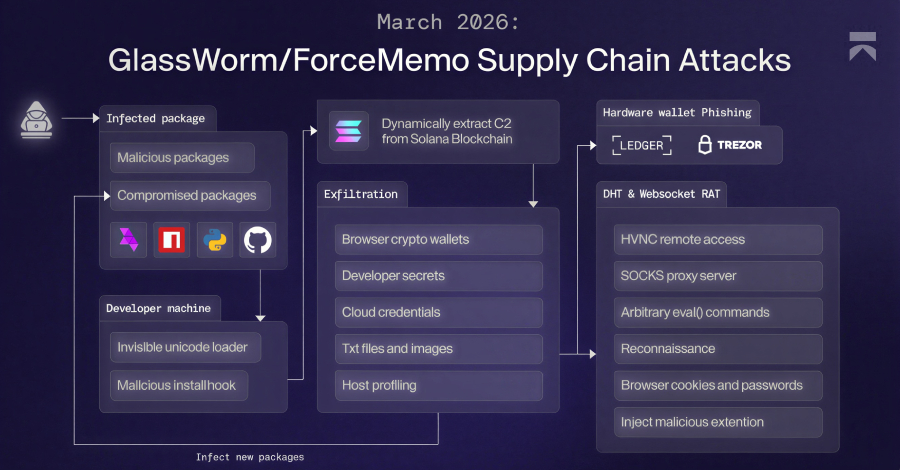
Cybersecurity experts have identified a sophisticated evolution of the GlassWorm malware campaign, which now employs a multi-stage framework to infiltrate systems, deploy a Remote Access Trojan (RAT), and exfiltrate sensitive data. This latest variant utilizes the Solana blockchain as a dead drop mechanism to discreetly retrieve command-and-control (C2) server addresses, enhancing the malware’s resilience against detection and takedown efforts.
Initial Infection Vector
The GlassWorm campaign initiates its attack by distributing malicious packages across various platforms, including npm, PyPI, GitHub, and the Open VSX marketplace. In some instances, the attackers have compromised legitimate project maintainers’ accounts to disseminate these tainted updates, thereby increasing the likelihood of unsuspecting developers downloading and installing the malware.
Avoidance of Russian Locales
A notable characteristic of this malware is its deliberate avoidance of systems configured with a Russian locale. This behavior suggests that the threat actors may be Russian-speaking and are intentionally steering clear of infecting systems within their own region, possibly to evade local law enforcement scrutiny.
Utilization of Solana Blockchain for C2 Communication
To establish communication with its C2 infrastructure, GlassWorm leverages transactions on the Solana blockchain. By embedding C2 server addresses within Solana transaction memos, the malware can dynamically retrieve these addresses without relying on traditional domain-based methods, which are more susceptible to being blocked or taken down. This technique not only enhances the malware’s persistence but also complicates efforts to disrupt its operations.
Multi-Stage Payload Deployment
Once the initial infection is successful, the malware proceeds to download and execute a series of payloads designed to harvest a wide array of sensitive information:
1. Data Theft Framework: This component is engineered to collect credentials, cryptocurrency wallet data, and perform comprehensive system profiling. The harvested information is then compressed into a ZIP archive and transmitted to an external server.
2. Hardware Wallet Phishing Module: A .NET binary monitors for the connection of hardware wallets such as Ledger or Trezor. Upon detecting such devices, it displays counterfeit error messages prompting users to enter their recovery phrases. This deceptive tactic aims to capture the recovery phrases, granting attackers full access to the victims’ cryptocurrency assets.
3. Remote Access Trojan (RAT): The RAT component establishes a covert channel with the C2 server, enabling the execution of various commands on the compromised system. These commands include deploying a Hidden Virtual Network Computing (HVNC) module for remote desktop access, initiating a SOCKS proxy via a WebRTC module, and exfiltrating data from web browsers such as Google Chrome, Microsoft Edge, Brave, Opera, Opera GX, Vivaldi, and Mozilla Firefox. Notably, the RAT can circumvent Chrome’s app-bound encryption (ABE) protections, allowing it to access sensitive browser data.
Malicious Browser Extension
In addition to the aforementioned components, the RAT forcibly installs a Google Chrome extension named Google Docs Offline on both Windows and macOS systems. This extension masquerades as a legitimate tool but is, in reality, an information-stealing module. Once installed, it connects to the C2 server to receive commands from the attackers, enabling further data exfiltration and system manipulation.
Implications and Recommendations
The GlassWorm campaign underscores the escalating sophistication of supply chain attacks targeting developers and their tools. By exploiting trusted platforms and employing advanced evasion techniques, such as utilizing blockchain transactions for C2 communication, the attackers have significantly increased the malware’s effectiveness and persistence.
To mitigate the risks associated with such threats, it is imperative for developers and organizations to adopt the following measures:
– Vigilant Package Management: Exercise caution when incorporating third-party packages into development projects. Verify the authenticity and integrity of packages, especially those from less familiar sources.
– Regular Security Audits: Conduct periodic reviews of development environments and tools to identify and address potential vulnerabilities.
– Multi-Factor Authentication (MFA): Implement MFA for all developer accounts to reduce the risk of unauthorized access and account compromise.
– User Education: Educate developers and staff about the dangers of phishing attacks and the importance of verifying the legitimacy of error messages and prompts, particularly those requesting sensitive information.
By implementing these proactive measures, organizations can enhance their defenses against sophisticated malware campaigns like GlassWorm and safeguard their development environments from compromise.